Security
Urgent Alert: CISA Urges Immediate Patching for iOS Vulnerabilities Linked to Crypto Theft

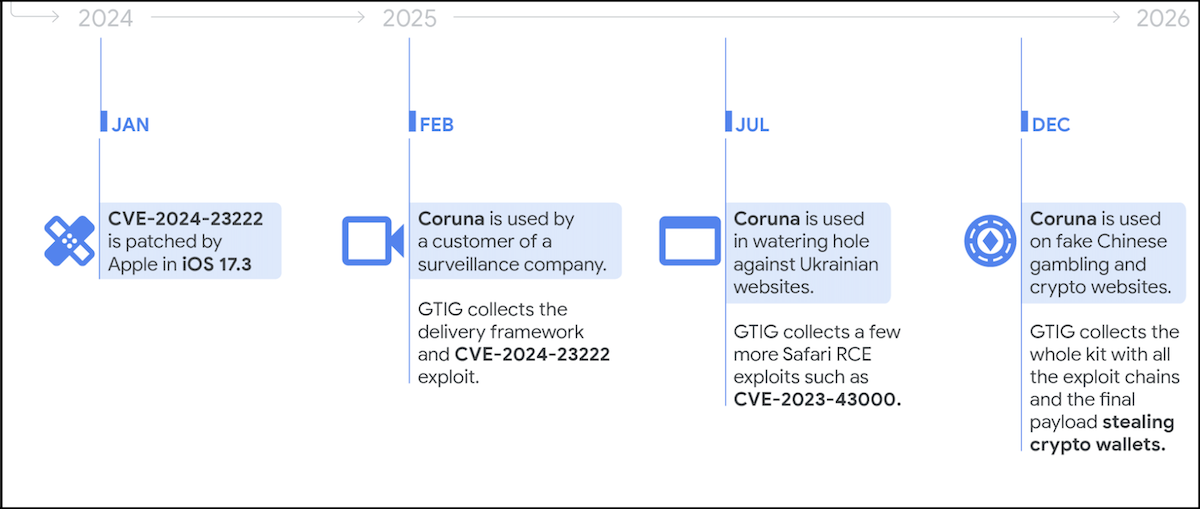
The Cybersecurity and Infrastructure Security Agency (CISA) in the United States has directed federal agencies to address three critical iOS security vulnerabilities that have been exploited in cyberespionage and crypto-theft attacks using the Coruna exploit kit.
Recent findings by the Google Threat Intelligence Group (GTIG) have uncovered that the Coruna exploit kit employs various exploit chains to target a total of 23 iOS vulnerabilities, with many of them being leveraged in zero-day attacks.
It is important to note that these exploits are ineffective on newer iOS versions and are thwarted if the target is utilizing private browsing or has activated Apple’s Lockdown Mode anti-spyware feature.
The Coruna exploit kit equips threat actors with capabilities such as Pointer Authentication Code (PAC) bypass, sandbox escape, and PPL (Page Protection Layer) bypass, allowing them to achieve WebKit remote code execution and elevate permissions to Kernel privileges on vulnerable devices.
GTIG has observed multiple threat actors utilizing the exploit kit, including a customer of a surveillance vendor, a suspected state-backed hacking group from Russia (UNC6353), and a financially motivated threat actor from China (UNC6691).
The latter group deployed the kit on fraudulent gambling and cryptocurrency websites to distribute a malware payload aimed at stealing the cryptocurrency wallets of infected victims.
iVerify, a mobile security firm, has characterized Coruna as an example of “sophisticated spyware-grade capabilities” that have transitioned “from commercial surveillance vendors to nation-state actors and, ultimately, mass-scale criminal operations.”
In response to these threats, CISA has identified three of the 23 Coruna vulnerabilities as Known Exploited Vulnerabilities and has instructed Federal Civilian Executive Branch (FCEB) agencies to secure their devices by March 26, following the directives of Binding Operational Directive (BOD) 22-01.
CISA emphasized the importance of implementing mitigations as per the vendor’s instructions, adhering to BOD 22-01 guidance for cloud services, or discontinuing product usage if mitigations are unavailable to combat these vulnerabilities effectively.
Given that such vulnerabilities are commonly exploited by malicious cyber actors and pose significant risks to the federal enterprise, CISA has urged all organizations, including private sector entities, to prioritize the patching of these flaws to enhance device security against potential attacks promptly.

Malicious software is becoming increasingly sophisticated. The Red Report 2026 details how emerging threats leverage mathematical techniques to evade sandboxes and remain undetected.
Access our analysis of over 1.1 million malicious samples to identify the top 10 tactics and assess the effectiveness of your security measures.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS































