Security
Security Alert: Cybercriminals Targeting Cisco and PAN VPN Gateways with Password Spraying Attacks

Password Spraying Attacks Targeting Cisco and PAN VPN Gateways
Recent automated campaigns have been observed targeting multiple VPN platforms, with a focus on credential-based attacks against Palo Alto Networks GlobalProtect and Cisco SSL VPN.
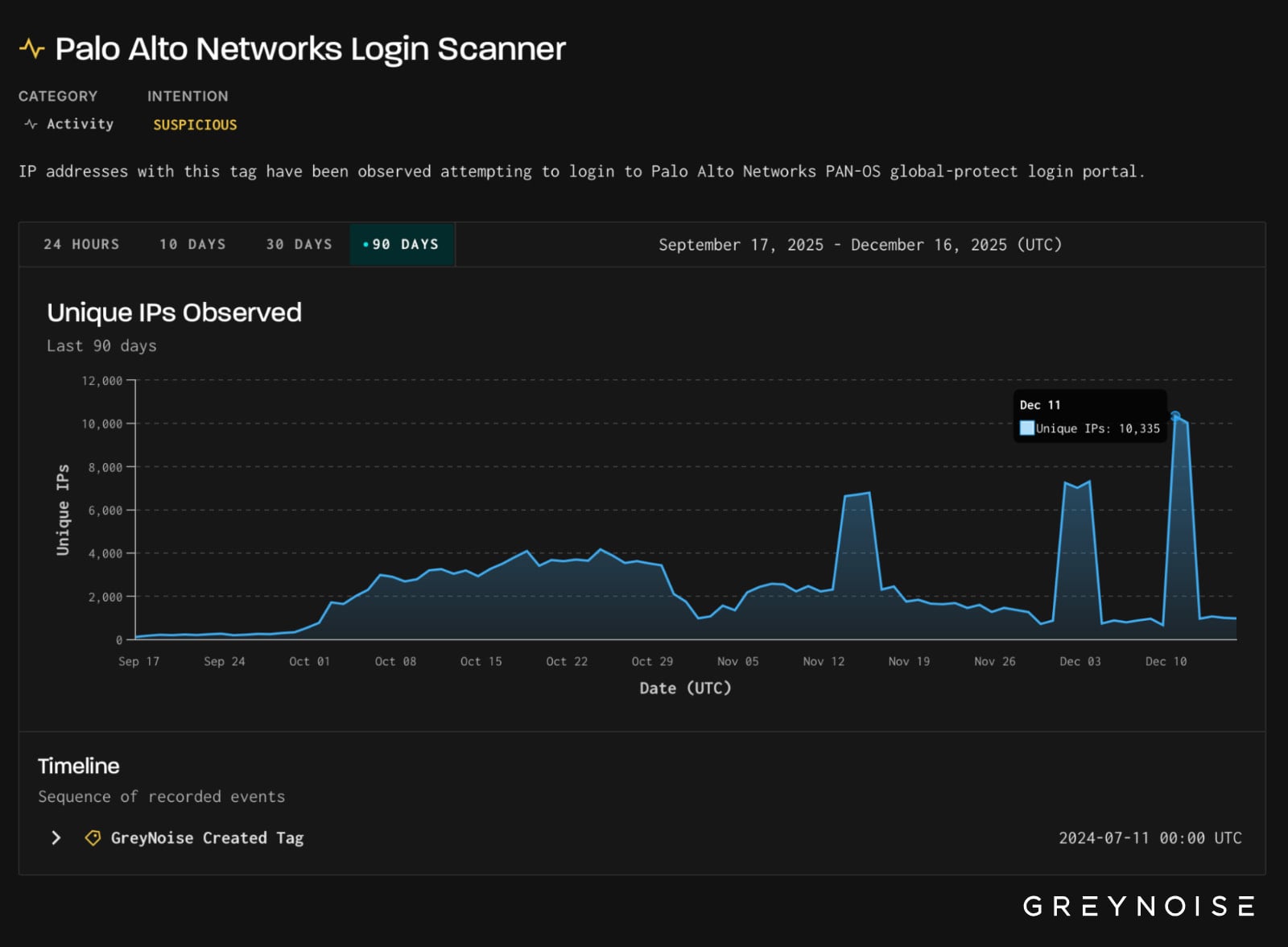
GreyNoise, a threat monitoring platform, reported a significant spike in login attempts aimed at GlobalProtect portals, reaching 1.7 million within a 16-hour period on December 11. These attacks originated from over 10,000 unique IP addresses and targeted infrastructure in the United States, Mexico, and Pakistan.
The majority of malicious traffic came from the 3xK GmbH (Germany) IP space, indicating a centralized cloud infrastructure. The threat actor behind these attacks primarily used common username and password combinations, with most requests originating from a Firefox user agent, which is uncommon for automated login activities through this provider.
According to GreyNoise, the consistent user agent, request structure, and timing suggest a scripted credential probing strategy to identify exposed or weakly protected GlobalProtect portals, rather than interactive access attempts or vulnerability exploitation.
This pattern of attacks against enterprise VPN authentication endpoints reflects ongoing pressure from threat actors, as observed by GreyNoise during periods of heightened attacker activity.
Source: GreyNoise
Subsequently, on December 12, GreyNoise detected activity from the same hosting provider targeting Cisco SSL VPN endpoints. The number of unique attack IPs rose to 1,273, significantly higher than the normal baseline of less than 200. This marked the first large-scale use of 3xK-hosted IPs against Cisco SSL VPNs in the past 12 weeks.
Similar to the GlobalProtect attacks, the login payloads in the Cisco SSL VPN probes followed standard SSL VPN authentication flows, including CSRF handling, indicating automated credential attacks rather than exploits.

Source: GreyNoise
While Cisco recently warned about a zero-day vulnerability (CVE-2025-20393) actively exploited in attacks targeting Secure Email Gateway (SEG) and Secure Email and Web Manager (SEWM) appliances, GreyNoise found no evidence linking the observed activity to this specific vulnerability.
A spokesperson from Palo Alto Networks acknowledged the reported credential-based activity targeting VPN gateways and emphasized the importance of using strong passwords and multi-factor authentication for protection against such attacks.
GreyNoise recommends administrators to conduct audits of network appliances, monitor for unexpected login attempts, and block known malicious IPs involved in these probing activities.

Broken IAM isn’t just an IT problem – the impact ripples across your whole business.
This practical guide covers why traditional IAM practices fail to keep up with modern demands, examples of what “good” IAM looks like, and a simple checklist for building a scalable strategy.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS































