


New Threat Actor Exploiting cPanel Vulnerability Targeting Government and Military Entities in Southeast Asia An unidentified threat actor has been detected targeting government and military organizations...


A newly discovered Linux implant known as Quasar Linux (QLNX) has been found to target developers’ systems with a combination of rootkit, backdoor, and credential-stealing capabilities....



A large-scale cyber campaign is underway, orchestrated by hackers to pilfer credentials through automated means by exploiting React2Shell (CVE-2025-55182) in vulnerable Next.js applications. Over 766 hosts...


Fake VS Code Alerts on GitHub Spread Malware to Developers A large-scale campaign is targeting developers on GitHub with fraudulent Visual Studio Code (VS Code) security...



Alphabet’s X Moonshot Factory Spins Out Anori, a Game-Changing Building Approval Platform Alphabet’s X moonshot factory has been working tirelessly for over a decade to revolutionize...
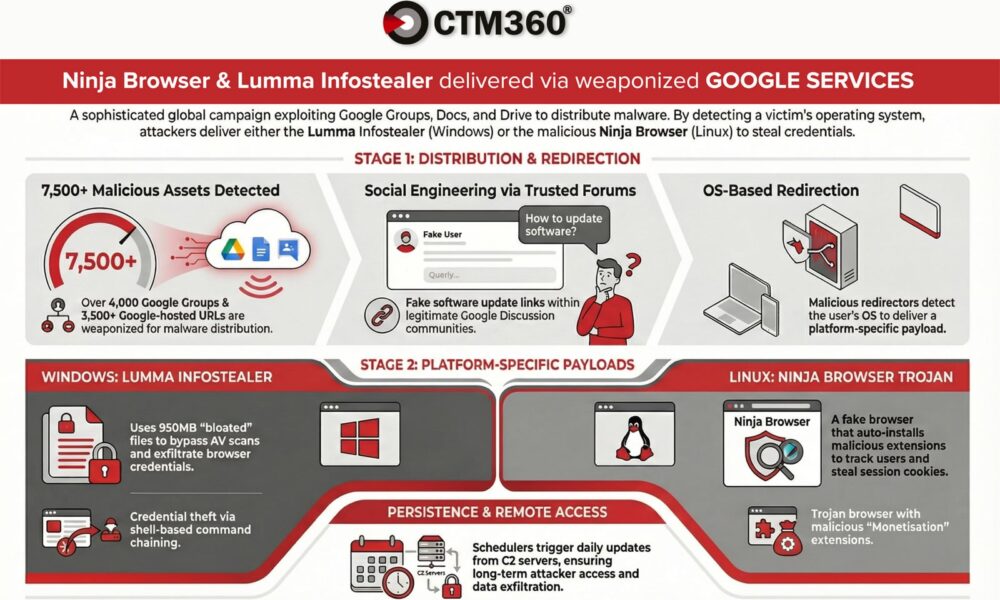

According to CTM360, a recent malware campaign is utilizing over 4,000 malicious Google Groups and 3,500 Google-hosted URLs to target organizations worldwide. Criminals are exploiting Google’s...



Keeping your personal information secure on your iPhone is crucial. From personal notes to bank apps, your device holds a lot of sensitive data that, if...



Germany Warns of State-Sponsored Phishing Attacks Targeting Senior Figures In a recent development, Germany’s domestic intelligence agency has issued a warning regarding suspected state-sponsored threat actors...



Amazon is not just a popular e-commerce store and streaming platform; it also boasts its cloud computing platform known as AWS (Amazon Web Services). AWS offers...



There is a growing trend of multiple threat actors targeting Microsoft 365 accounts through phishing attacks that exploit the OAuth device code authorization mechanism. In these...
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.