Security
Stealthy Infostealer: The Malicious NPM Package Targeting Windows, Linux, and macOS

Recent reports have unveiled a concerning discovery within the npm registry, where ten malicious packages disguised as legitimate software projects have been found to download an information-stealing component on Windows, Linux, and macOS systems.
These nefarious packages, uploaded on July 4, managed to evade detection for an extended period by employing sophisticated layers of obfuscation that outwitted standard static analysis techniques.
Security experts at Socket have identified that these ten deceptive packages, boasting nearly 10,000 downloads, have been actively stealing sensitive data, including credentials from system keyrings, browsers, and authentication services.
Despite being reported to npm, these malicious packages, named as follows, are still accessible:
- typescriptjs
- deezcord.js
- dizcordjs
- dezcord.js
- etherdjs
- ethesjs
- ethetsjs
- nodemonjs
- react-router-dom.js
- zustand.js
Socket’s researchers have revealed that these packages utilize a fake CAPTCHA challenge to masquerade as legitimate software, ultimately leading users to unwittingly download a 24MB infostealer packaged with PyInstaller.
To entice unsuspecting victims, the threat actor behind this scheme employed typosquatting, a tactic that capitalizes on misspelled or slightly altered versions of well-known software names such as TypeScript, discord.js, ethers.js, nodemon, react-router-dom, and zustand.
Developers searching for these legitimate packages on npm may fall prey to these malicious imposters due to the subtle differences in their names.
Upon installation, a ‘postinstall’ script is triggered automatically, launching a new terminal window tailored to the host’s operating system. This script executes ‘app.js’ discreetly to avoid detection, using obfuscation techniques to conceal its malicious intent.
The ‘app.js’ file acts as the malware loader, employing multiple obfuscation layers, including self-decoding eval wrappers, XOR decryption with dynamically generated keys, URL-encoded payloads, and intricate control-flow obfuscation.
As part of the installation process, a fake CAPTCHA prompt is displayed in the terminal using ASCII art to deceive users into believing in the legitimacy of the process.
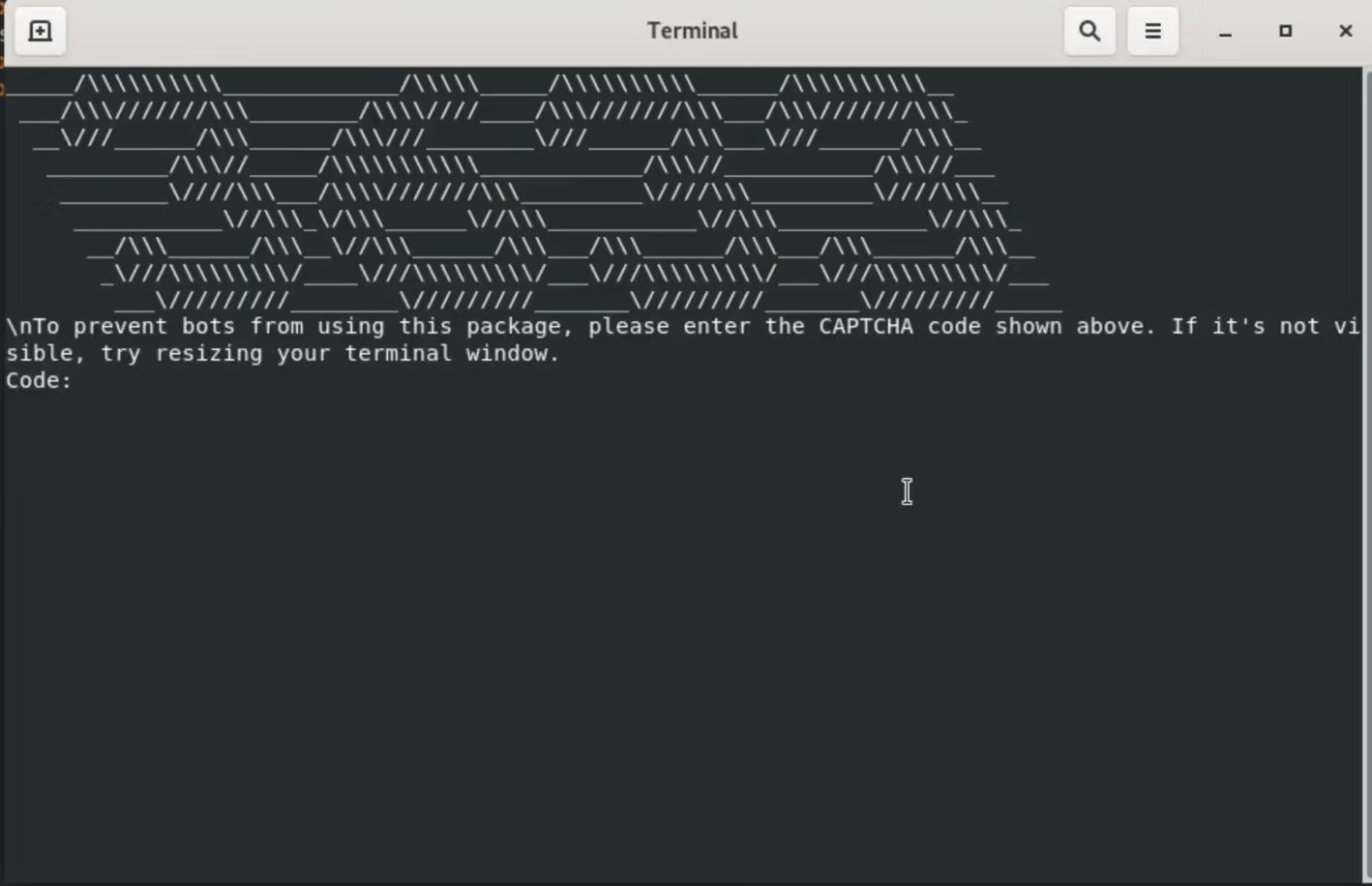
Source: Socket
Subsequently, the malware sends the victim’s geolocation and system fingerprint data to the attacker’s command and control server, facilitating the automatic download and execution of a platform-specific binary from an external source, packaged as a 24MB PyInstaller executable.
This information-stealing malware specifically targets system keyrings like Windows Credential Manager, macOS Keychain, Linux SecretService, libsecret, and KWallet, as well as data stored in Chromium-based and Firefox browsers, including profiles, passwords, and session cookies.
Furthermore, the malware searches for SSH keys in common directories and attempts to extract OAuth, JWT, and other API tokens for illicit purposes.
The stolen data is compressed and sent to the attacker’s server at 195[.]133[.]79[.]43, with a temporary staging step in /var/tmp or /usr/tmp.
Developers who inadvertently downloaded any of the aforementioned packages are advised to cleanse their systems of the infection and reset all access tokens and passwords, as there is a high likelihood of compromise.
When sourcing packages from npm or other open-source repositories, it is crucial to double-check for typos and ensure the authenticity of the publisher and repository to mitigate the risk of falling victim to such malicious schemes.

46% of environments had passwords cracked, nearly doubling from 25% last year.
Explore the Picus Blue Report 2025 for a detailed analysis of prevention, detection, and data exfiltration trends.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS






























