


Cisco has identified two new security vulnerabilities in Catalyst SD-WAN Manager that are actively being exploited, prompting administrators to update vulnerable devices for enhanced protection. Catalyst...

Uncovering a New Threat: Fake IT Support Used to Deliver Havoc Command-and-Control Framework A recent campaign has caught the attention of threat hunters, revealing a disturbing...
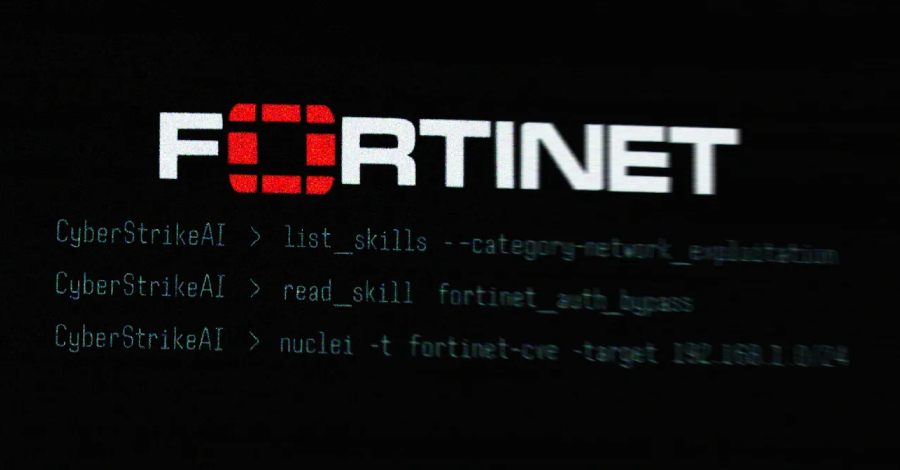

An AI-assisted cyberattack campaign targeting Fortinet FortiGate appliances was recently uncovered, with the threat actor utilizing an open-source, AI-native security testing platform called CyberStrikeAI to carry...



The Rise of AI-Powered Cybersecurity Tools in 2026 In the realm of cybersecurity, researchers have uncovered a concerning development involving a newly discovered open-source AI security...



The Rise of Female Social Engineers in Cybercrime An infamous cybercrime group, known as Scattered LAPSUS$ Hunters (SLH), is now seeking to recruit women to conduct...



Ransomware Threats Outpacing Defenses: The Growing Preparedness Gap The gap between ransomware threats and the defenses meant to stop them is widening, according to Ivanti’s 2026...



There has been a recent surge in physical letter phishing attacks targeting users of Trezor and Ledger, two renowned cryptocurrency hardware wallet manufacturers. These threat actors...



One Threat Actor Responsible for 83% of Recent Ivanti RCE Attacks Recent threat intelligence indicates that a single threat actor is behind the majority of active...



Reports indicate that state-sponsored hackers have been utilizing Google’s Gemini AI model at various stages of cyber attacks, ranging from initial reconnaissance to post-compromise activities. Hackers...



The Abuse of Employee Monitoring Software for Ransomware Deployment Recent incidents have revealed a concerning trend where threat actors, specifically a member of the Crazy ransomware...
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.