
Recent Security Threats: A Recap Another week, another array of peculiar security incidents that unfolded within a span of seven days. From ingenious tactics to lazy...



Veeam Software, a data protection company, has recently addressed multiple vulnerabilities in its Backup & Replication solution, including four critical remote code execution (RCE) flaws. Backup...



Cloud Attacks Exploit Vulnerabilities More Than Weak Credentials Recent reports from Google indicate a shift in cyber threats targeting cloud environments, with hackers increasingly exploiting newly...


Malicious actors have devised a new tactic known as InstallFix, a variant of the ClickFix social engineering technique, to deceive users into running harmful commands under...



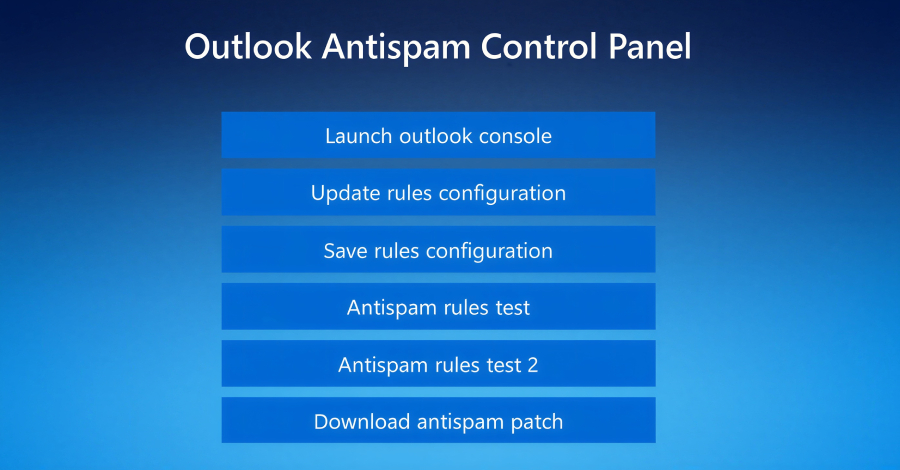
Cisco has identified two new security vulnerabilities in Catalyst SD-WAN Manager that are actively being exploited, prompting administrators to update vulnerable devices for enhanced protection. Catalyst...
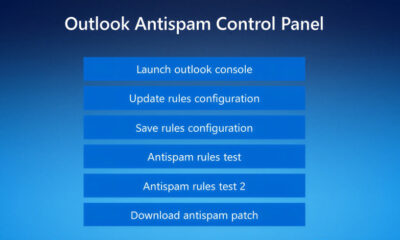

Uncovering a New Threat: Fake IT Support Used to Deliver Havoc Command-and-Control Framework A recent campaign has caught the attention of threat hunters, revealing a disturbing...
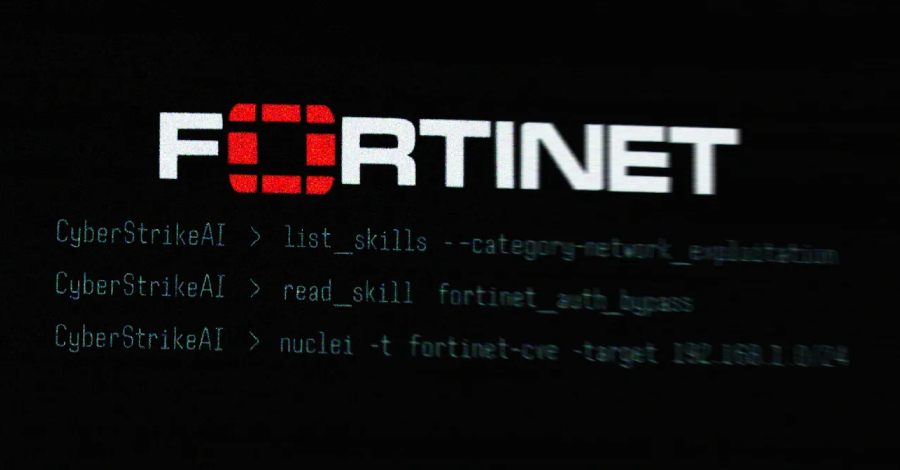

An AI-assisted cyberattack campaign targeting Fortinet FortiGate appliances was recently uncovered, with the threat actor utilizing an open-source, AI-native security testing platform called CyberStrikeAI to carry...



The Rise of AI-Powered Cybersecurity Tools in 2026 In the realm of cybersecurity, researchers have uncovered a concerning development involving a newly discovered open-source AI security...



The Rise of Female Social Engineers in Cybercrime An infamous cybercrime group, known as Scattered LAPSUS$ Hunters (SLH), is now seeking to recruit women to conduct...



Ransomware Threats Outpacing Defenses: The Growing Preparedness Gap The gap between ransomware threats and the defenses meant to stop them is widening, according to Ivanti’s 2026...
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.