Security
Uncovering the Vulnerabilities: How Cloud Attacks Expose Security Flaws Beyond Weak Credentials

Cloud Attacks Exploit Vulnerabilities More Than Weak Credentials
Recent reports from Google indicate a shift in cyber threats targeting cloud environments, with hackers increasingly exploiting newly disclosed vulnerabilities in third-party software to gain initial access. This trend has led to a significant decrease in the use of weak credentials or misconfigurations as primary access points.
According to Google’s findings, incident responders have identified bug exploits as the primary access vector in 44.5% of investigated intrusions, compared to credentials being responsible for 27% of breaches.
Source: Google
One of the most common vulnerability types exploited in these attacks is remote code execution (RCE), with notable instances such as React2Shell (CVE-2025-55182) and the XWiki flaw tracked as CVE-2025-24893, which were leveraged in RondoDox botnet attacks.
Google attributes this shift in focus to increased security measures for accounts and credentials, leading to a decrease in traditional, easily exploitable paths utilized by threat actors.
The exploitation window has now shrunk from weeks to just a few days, as observed by Google, with cryptominers being deployed within 48 hours of vulnerability disclosure. This indicates that hackers are swift in weaponizing new flaws and incorporating them into their attack strategies.
Both state-sponsored actors and financially-motivated hackers have predominantly leveraged compromised identities, often through phishing and vishing techniques impersonating IT help desk staff, to gain access to a target organization’s cloud platform.
In many investigated attacks, the primary objective of the actors was silent data exfiltration without immediate extortion, focusing on obtaining high volumes of data for long-term exploitation.
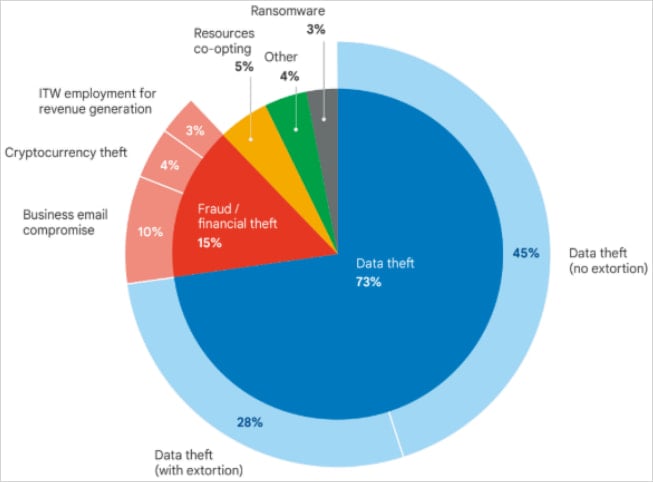
Source: Google
Noteworthy espionage campaigns from actors linked to Iran and China have been highlighted by Google, with instances of maintaining access to victim environments for extended periods.
For instance, Iran-linked threat actor UNC1549 had access to a target environment for over two years using stolen VPN credentials and the MiniBike malware, allowing them to steal nearly one terabyte of proprietary data.
In another case, China-sponsored actor UNC5221 utilized the BrickStorm malware to retain access to a victim’s VMware vCenter servers for at least 18 months, enabling the theft of source code.
North Korean Hackers Engage in Financially-Motivated Attacks
Google’s analysis attributes 3% of intrusions in the latter half of 2025 to North Korean IT workers (UNC5267) leveraging fraudulent identities to generate revenue for the government.
Another North Korean threat actor identified as UNC4899 targeted cloud environments specifically for stealing digital assets, including a case where they stole millions of U.S. dollars in cryptocurrency by tricking a developer into downloading a malicious archive.
The developer unwittingly transferred the malicious file to their corporate workstation, leading to UNC4899 gaining access and eventually compromising user accounts to steal cryptocurrency.
“The binary beaconed out to UNC4899-controlled domains and served as the backdoor that gave the threat actors access to the victim’s workstation, effectively granting them a foothold into the corporate network” – Google
Google further highlights incidents of OpenID Connect Abuse and malicious insiders utilizing cloud services for data exfiltration, emphasizing the need for robust data protection mechanisms against both internal and external threats.
Conclusion
Google underscores the importance of automated incident response in the face of rapidly evolving cloud attacks, where threat actors deploy payloads within hours of vulnerability disclosure. The tech giant anticipates increased threat activity in the coming year, driven by geopolitical conflicts and major events like the FIFA World Cup and U.S. midterm elections.
-

 Facebook8 months ago
Facebook8 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS