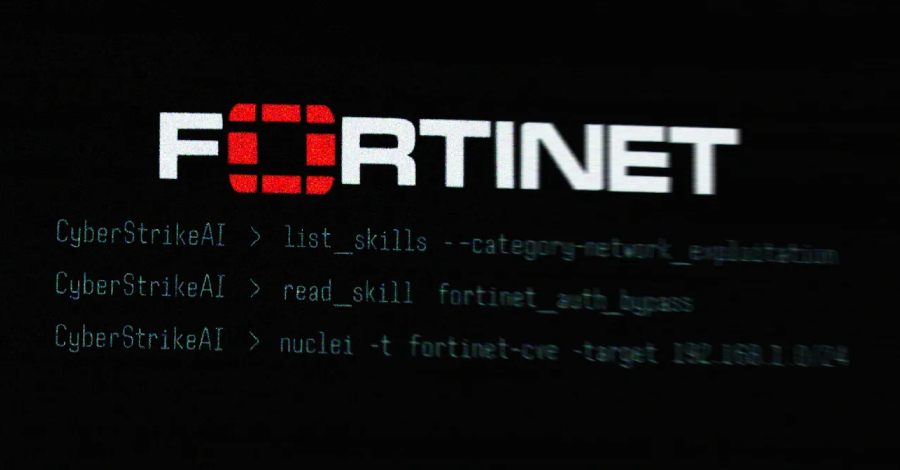
An AI-assisted cyberattack campaign targeting Fortinet FortiGate appliances was recently uncovered, with the threat actor utilizing an open-source, AI-native security testing platform called CyberStrikeAI to carry out the attacks.
Team Cymru identified the use of CyberStrikeAI after analyzing the IP address (“212.11.64[.]250”) used by the suspected Russian-speaking threat actor for automated mass scanning of vulnerable appliances.
CyberStrikeAI is an open-source AI offensive security tool developed by a China-based developer with potential ties to the Chinese government, according to security researcher Will Thomas (aka @BushidoToken).
Last month, Amazon Threat Intelligence reported detecting the attacker targeting FortiGate devices using generative AI services like Anthropic Claude and DeepSeek, compromising over 600 appliances across 55 countries.
Described in its GitHub repository, CyberStrikeAI is built in Go and integrates over 100 security tools for vulnerability discovery, attack-chain analysis, knowledge retrieval, and result visualization. The tool is managed by a Chinese developer known as Ed1s0nZ.
Between January 20 and February 26, 2026, Team Cymru observed 21 unique IP addresses running CyberStrikeAI, primarily hosted in China, Singapore, and Hong Kong, with additional servers detected in the U.S., Japan, and Switzerland.
In addition to CyberStrikeAI, Ed1s0nZ has released various other tools focusing on exploitation and jailbreaking AI models, such as watermark-tool, banana_blackmail, PrivHunterAI, ChatGPTJailbreak, InfiltrateX, and VigilantEye.
Further investigations into Ed1s0nZ’s GitHub activities revealed interactions with organizations supporting Chinese government state-sponsored cyber operations, including Knownsec 404, a Chinese security vendor with ties to the Chinese Ministry of State Security.
Knownsec 404, described as a state-aligned cyber contractor capable of supporting Chinese national security, intelligence, and military objectives, experienced a significant leak of internal documents exposing sensitive information.

Ed1s0nZ’s activities also include modifications to a README.md file in a repository, removing references to awards and affiliations with the China National Vulnerability Database of Information Security (CNNVD) in an attempt to conceal potential state ties.
Research indicates that China maintains two vulnerability databases, CNNVD overseen by the Ministry of State Security and CNVD controlled by CNCERT, with CNNVD taking longer to publish vulnerabilities with higher CVSS scores.
Ed1s0nZ’s efforts to distance themselves from state ties point to a desire to protect CyberStrikeAI’s operational viability as its popularity grows, signaling a concerning trend in the adoption of AI-augmented offensive security tools.