Security
Glassworm Malware Strikes Again with Third Wave of Malicious VS Code Packages
The Glassworm Campaign: A Deep Dive into the Malware Targeting VS Code Developers
Recently, the Glassworm campaign has resurfaced with 24 new packages infiltrating the OpenVSX and Microsoft Visual Studio marketplaces. This malicious software, first detected in October, poses a significant threat to developers utilizing VS Code-compatible editors.
OpenVSX and the Microsoft Visual Studio Marketplace serve as extension repositories for developers, offering a range of language support, frameworks, themes, and productivity add-ons. While the Microsoft marketplace is the official platform for Visual Studio Code, OpenVSX provides an open, vendor-neutral alternative for editors outside of Microsoft’s ecosystem.
Initially uncovered by Koi Security, Glassworm employs stealthy tactics by using “invisible Unicode characters” to conceal its malicious code. Once installed, the malware targets GitHub, npm, and OpenVSX accounts, as well as cryptocurrency wallet data from 49 extensions.
Furthermore, Glassworm deploys a SOCKS proxy to facilitate malicious traffic through the victim’s machine and installs an HVNC client for covert remote access by operators.
Despite initial efforts to remove the infection from the extension repositories, Glassworm resurfaced with new extensions and publisher accounts shortly after. Secure Annex’s researcher, John Tuckner, identified the resurgence, highlighting a broad scope targeting popular tools and developer frameworks such as Flutter, Vim, Yaml, Tailwind, Svelte, React Native, and Vue.
Source: Secure Annex
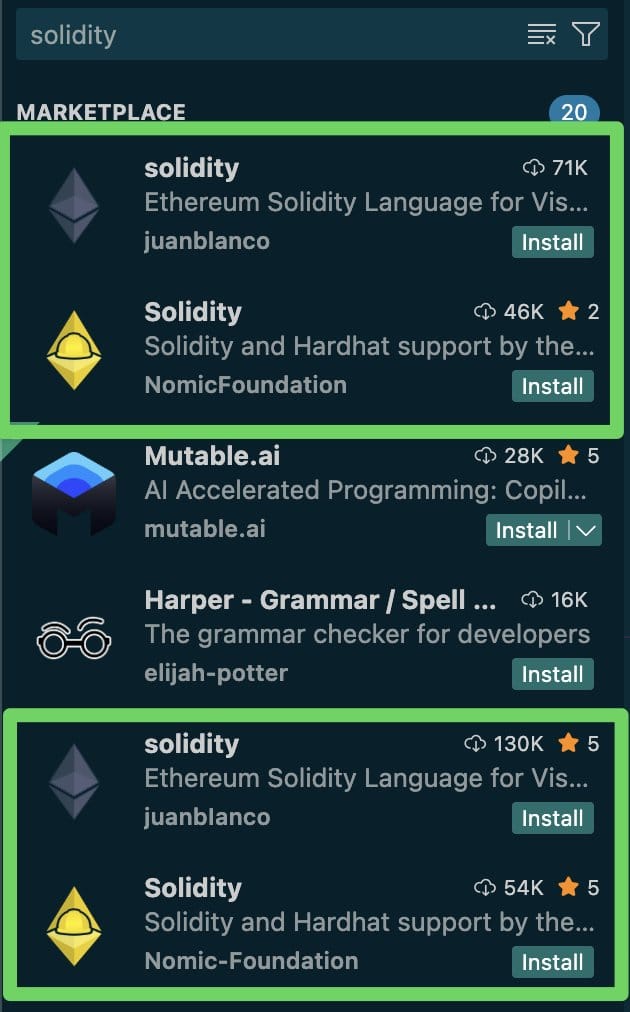
Secure Annex’s latest findings reveal a third wave of Glassworm utilizing specific packages on both the VS Marketplace and Open VSX. These packages are strategically designed to infiltrate the marketplaces, with publishers pushing updates that introduce malicious code while inflating download counts to appear legitimate and trustworthy.
Manipulating download counts not only deceives users but also impacts search results, positioning the malicious extensions closely alongside legitimate projects they impersonate.
Source: Secure Annex
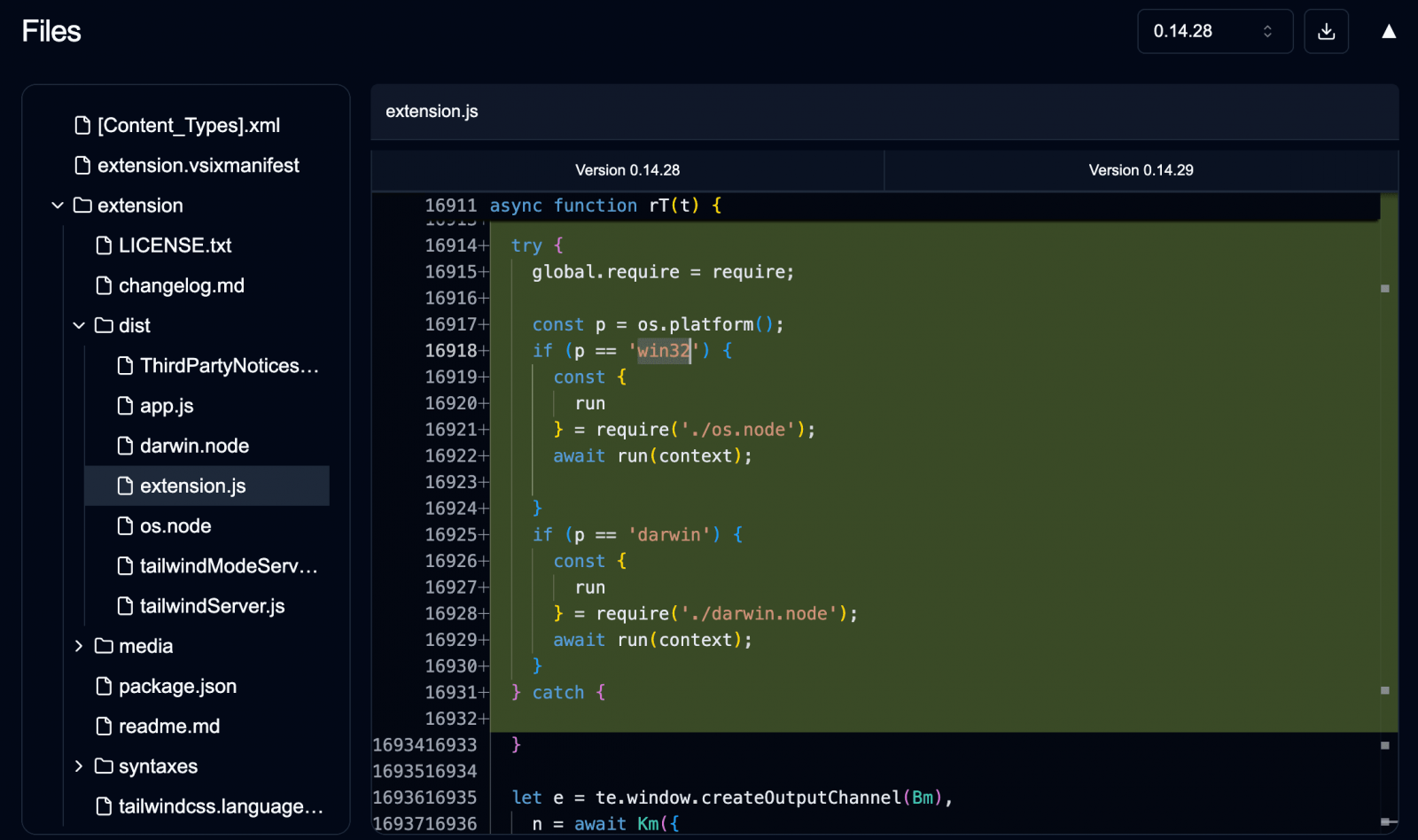
On the technical front, Glassworm has evolved to incorporate Rust-based implants within extensions, alongside the continued use of invisible Unicode characters. This advancement poses a greater challenge to detection and mitigation efforts.
Source: Secure Annex
BleepingComputer has reached out to OpenVSX and Microsoft for comments on Glassworm’s persistence in bypassing their defenses. Updates on their responses will be provided as soon as available.

Broken IAM isn’t just an IT problem – the impact ripples across your whole business.
This practical guide covers why traditional IAM practices fail to keep up with modern demands, examples of what “good” IAM looks like, and a simple checklist for building a scalable strategy.
-

 Facebook6 months ago
Facebook6 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS





























