AI exploited multiple zero-day vulnerabilities to bypass security measures. Stay informed about emerging threats.
Join the Autonomous Validation Summit (May 12 & 14) to learn about cutting-edge validation techniques.
Claim Your Spot

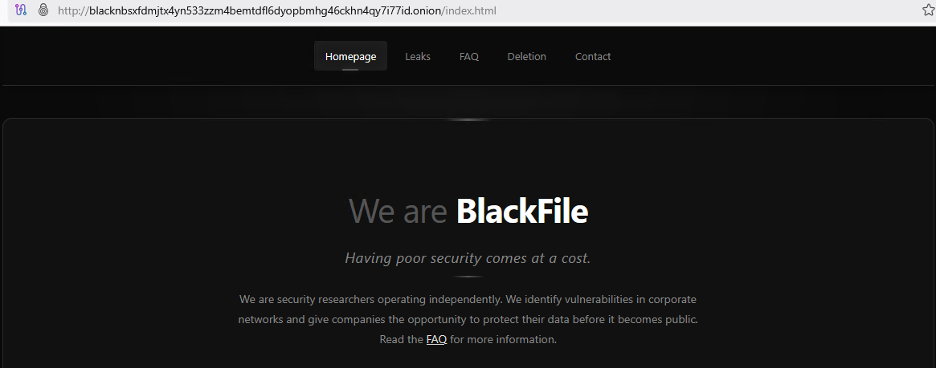
In recent months, a new financially motivated hacking group known as BlackFile has emerged, targeting retail and hospitality organizations with a wave of data theft and extortion attacks. Since February 2026, this group, also identified as CL-CRI-1116, UNC6671, and Cordial Spider, has been actively involved in stealing employee credentials and demanding large ransoms by impersonating corporate IT helpdesk staff.
Information shared by cybersecurity firm Palo Alto Networks’ Unit 42 with the Retail & Hospitality Information Sharing and Analysis Center (RH-ISAC) has revealed the tactics employed by BlackFile. The group has been linked, with moderate confidence, to “The Com,” a network of English-speaking cybercriminals known for their involvement in various illicit activities.
According to a report by RH-ISAC, BlackFile initiates its attacks by making phone calls to employees from spoofed numbers, pretending to be IT support. They then lead the staff to fake login pages to steal their credentials using social engineering techniques.
The group utilizes voice-based phishing (vishing) and fraudulent Caller ID information to deceive employees into divulging sensitive information. This approach has similarities to tactics employed by other cybercriminal groups like ShinyHunters and SLSH.
By exploiting stolen credentials, BlackFile bypasses multifactor authentication and gains access to executive-level accounts by scraping internal directories. The attackers target Salesforce and SharePoint servers to extract data containing confidential information such as Social Security Numbers.
The stolen data is transferred to the group’s servers and published on the dark web for ransom demands. Victims are contacted through compromised email accounts or random Gmail addresses.
Furthermore, RH-ISAC highlighted that the attackers conduct swatting attempts, targeting not only companies but also their employees, including senior executives. This malicious tactic adds pressure on victims by involving false emergency calls to responders.
Mandiant, a cybersecurity firm, is actively responding to vishing incidents related to data theft and extortion, including those involving BlackFile. Measures to counter such attacks include enhancing call-handling policies, implementing multifactor identity verification, and providing social engineering training to staff.

AI exploited multiple zero-day vulnerabilities to bypass security measures. Stay informed about emerging threats.
Join the Autonomous Validation Summit (May 12 & 14) to learn about cutting-edge validation techniques.
Claim Your Spot


EU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules


Warning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos


Facebook’s New Look: A Blend of Instagram’s Style
Facebook Compliance: ICE-tracking Page Removed After US Government Intervention


Facebook and Instagram to Reduce Personalized Ads for European Users


InstaDub: Meta’s AI Translation Tool for Instagram Videos


Reclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery


Meta discontinues Messenger apps for Windows and macOS
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.