Security
Unleashing Hackers: How .arpa DNS and ipv6 are Exploited to Bypass Phishing Defenses

Phishing campaigns are evolving with threat actors exploiting the special-use “.arpa” domain and IPv6 reverse DNS to bypass domain reputation checks and email security gateways.
The .arpa domain is specifically reserved for internet infrastructure, not regular websites, and is utilized for reverse DNS lookups to map IP addresses back to hostnames.
When it comes to reverse lookups, IPv4 uses the in-addr.arpa domain, while IPv6 utilizes ip6.arpa. These lookups involve DNS querying a hostname derived from the IP address, written in reverse order and attached to one of these domains.
For instance, the IP addresses for www.google.com, 192.178.50.36 (IPv4) and 2607:f8b0:4008:802::2004 (IPv6), can be queried using the dig tool to resolve to in-addr.arpa and ip6.arpa hostnames respectively.
Phishing activities have been observed exploiting the ip6.arpa reverse DNS TLD, enabling attackers to manipulate the reverse DNS zone for their IPv6 address space by configuring additional DNS records for phishing purposes.
Abuse of .arpa Domains in Phishing Campaigns
A recent phishing campaign identified by Infoblox showcases attackers misusing the ip6.arpa reverse DNS TLD to set up phishing sites.
By gaining control over the DNS zone for an IPv6 range, threat actors could configure various record types beyond PTR records, which are typically used for reverse DNS domains.
Infoblox highlighted instances where threat actors leveraged reputable DNS providers like Hurricane Electric and Cloudflare to create these records, potentially exploiting gaps in DNS platform configurations.
The attackers’ modus operandi involved obtaining an IPv6 address block through tunneling services, generating reverse DNS hostnames with obscure subdomains, and redirecting these domains to infrastructure housing phishing content.
Instead of setting up expected PTR records, the attackers utilized A records linking reverse DNS domains to servers hosting phishing sites.
Phishing emails in this campaign enticed recipients with promises of rewards or notifications, embedding lures as images linked to reverse IPv6 DNS records to evade suspicion.
Upon clicking these images, victims unknowingly resolved to attacker-controlled DNS name servers via a DNS provider.
Further disguising their activities, attackers routed traffic through a validation system to determine the target’s legitimacy before redirecting them to phishing sites.
Infoblox noted that the phishing links had short lifespans, expiring after a few days to obfuscate analysis efforts by security researchers.
Moreover, the use of the ‘.arpa’ domain, devoid of typical domain data like WHOIS information, complicates detection by email gateways and security tools.
Researchers observed additional tactics in the phishing campaign, such as hijacking CNAME records and subdomain shadowing to deploy phishing content under legitimate organizations’ subdomains.
By exploiting trusted reverse DNS features, attackers can craft phishing URLs that evade traditional detection mechanisms.
As a preventative measure, users are advised to refrain from clicking on unfamiliar email links and instead access services directly through official websites.
Malware tactics are evolving. The Red Report 2026 uncovers new threats utilizing mathematical techniques to evade detection and operate covertly.
Access our analysis of 1.1 million malicious samples to identify the top 10 techniques and evaluate your security posture.
-

 Facebook8 months ago
Facebook8 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
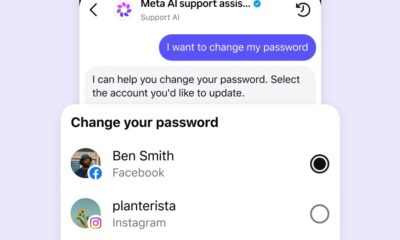
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS