Security
Vercel Data Breach: Hackers Offering Stolen Information for Sale

Update 4/19/26: Additional information has been revealed by Vercel post-publishing.
Vercel, a cloud development platform, has recently faced a security breach where threat actors claimed to have infiltrated their systems and are now attempting to sell the stolen data.
Vercel is a popular cloud platform that offers hosting and deployment infrastructure for developers, particularly focusing on JavaScript frameworks.

The company is best known for developing Next.js, a widely-used React framework, and providing services such as serverless functions, edge computing, and CI/CD pipelines to assist developers in building, previewing, and deploying applications.
In a security bulletin released recently, Vercel mentioned that only a limited number of customers were impacted by the security breach.
Vercel stated, “We have discovered a security incident involving unauthorized access to certain internal Vercel systems. We are actively investigating the matter and have enlisted the help of incident response experts to investigate and resolve the issue. Law enforcement has been notified, and updates will be provided as the investigation progresses.”
The company ensured that its services have not been affected and is actively working with the affected customers to address the situation.
Vercel is taking necessary steps to safeguard its customers, advising them to review environment variables, utilize its sensitive environment variable feature, and rotate secrets if necessary.
After the initial publication, Vercel updated its advisory to clarify that the breach originated from a compromise of a third-party AI tool’s Google Workspace OAuth application.
The specific company to which the OAuth application belongs is currently undisclosed. Vercel recommends that Google Workspace administrators and Google account owners check for the following application: OAuth App: 110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com
For any information regarding this incident or other undisclosed attacks, feel free to contact us confidentially via Signal at 646-961-3731 or at tips@bleepingcomputer.com.
Hacker Allegedly Selling Stolen Vercel Data
Following the disclosure, a threat actor claiming to be “ShinyHunters” announced on a hacking forum that they had successfully breached Vercel and were now selling access to company data.
It is important to note that while the hacker associates themselves with the ShinyHunters group, other threat actors linked to recent attacks attributed to the ShinyHunters extortion gang have denied involvement in this specific incident.
In the forum post, the hacker mentioned selling access keys, source code, and database data allegedly obtained from Vercel, along with access to internal deployments and API keys.
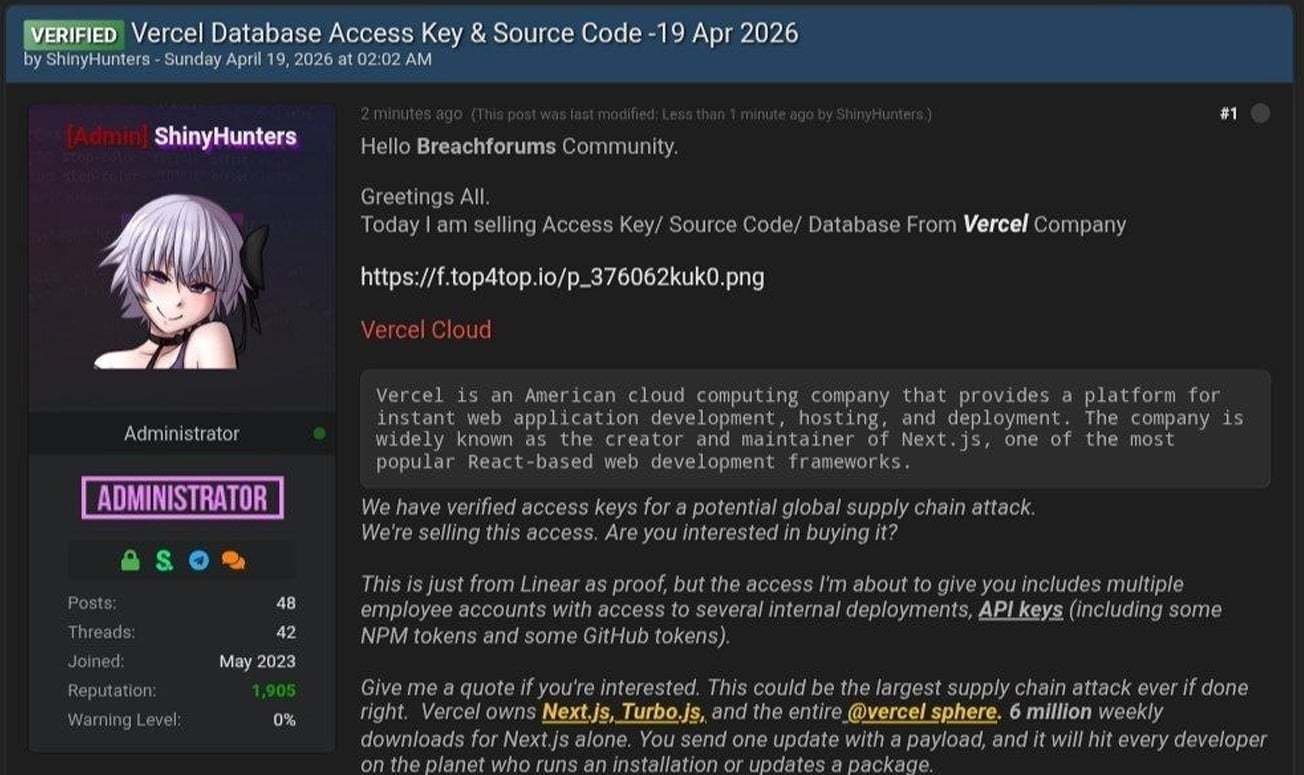
The attacker also shared a text file containing Vercel employee information, consisting of 580 data records including names, Vercel email addresses, account status, and activity timestamps. Additionally, they shared a screenshot of an internal Vercel Enterprise dashboard.
Verification of the authenticity of the data or screenshot shared by the attacker is yet to be confirmed independently by BleepingComputer.
In messages exchanged on Telegram, the threat actor mentioned being in communication with Vercel regarding the breach and discussed an alleged ransom demand of $2 million.
BleepingComputer reached out to Vercel for further details on the breach, including the exposure of any sensitive data or credentials, negotiations with the attackers, and will update accordingly upon receiving a response.
Update 4/19/26 6:14 PM ET: The article has been updated to include additional information disclosed by Vercel.

An AI exploit chaining four zero-days into one exploit was able to bypass both renderer and OS sandboxes, signaling a wave of new exploits. Learn more at the Autonomous Validation Summit (May 12 & 14) on how autonomous, context-rich validation identifies vulnerabilities, confirms control efficacy, and closes the remediation loop.
-

 Facebook8 months ago
Facebook8 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS






























