Security
Uncovering Russian Intelligence: The FBI’s Investigation into Signal Phishing Attacks

Russian Intelligence-Linked Threat Actors Targeting Encrypted Messaging Apps
In a recent public service announcement, the FBI has cautioned users of encrypted messaging apps like Signal and WhatsApp about ongoing phishing campaigns orchestrated by Russian intelligence-linked threat actors. These campaigns have already compromised a significant number of accounts, prompting concerns about data security.
This announcement marks the first direct attribution of such attacks to Russian intelligence services, highlighting the specific targeting of users of commercial messaging apps to bypass end-to-end encryption through account hijacks.
While the attacks can potentially affect multiple commercial messaging apps, Signal users are predominantly targeted. The attackers aim to gain unauthorized access to accounts to read private messages, access contact lists, impersonate victims, and launch further phishing campaigns.
According to the FBI, the victims of these attacks are primarily individuals with access to sensitive information, including current and former U.S. government officials, military personnel, political figures, and journalists.
International Warnings and Advisories
Prior to the FBI’s announcement, Dutch and French cybersecurity authorities had issued advisories about similar account-hijacking operations targeting Signal and WhatsApp users. These operations primarily rely on tricking users into granting access to their accounts or linking them to attacker-controlled devices.
France’s Cyber Crisis Coordination Center (C4) also raised concerns about widespread phishing tactics targeting instant messaging platforms, indicating ongoing threats across various countries.
Phishing Techniques and Implications
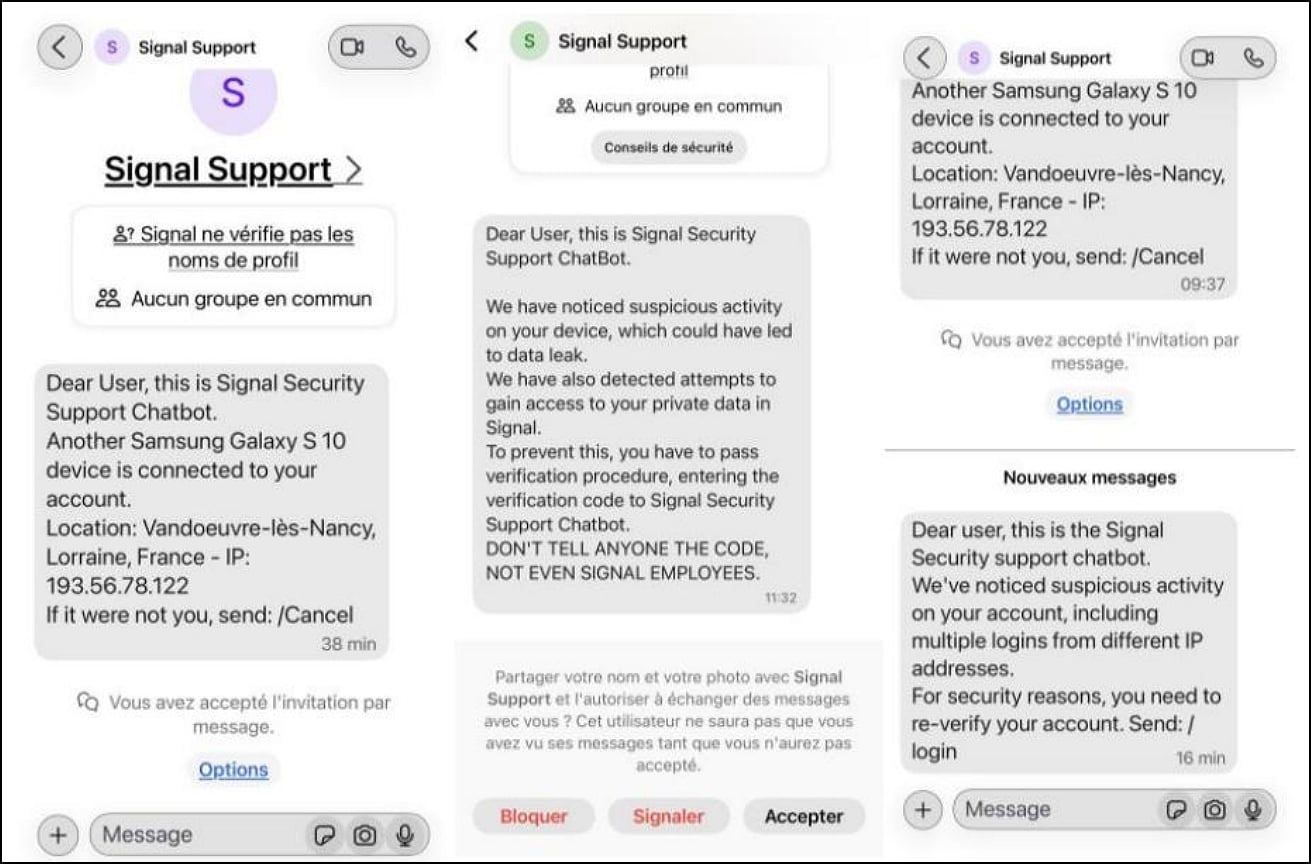
All three advisories emphasize that phishing attacks are used to bypass encryption by hijacking accounts or linking devices to existing accounts. The tactics typically involve impersonating support accounts to deceive targets into sharing verification codes or scanning malicious QR codes.
Once threat actors gain access to accounts, they can monitor communications, join group chats, and send messages on behalf of compromised users, making detection challenging and enabling further phishing attempts.
It is important to note that the encryption in platforms like Signal and WhatsApp remains intact, and the vulnerabilities exploited in these attacks are related to human interaction rather than a technical flaw in the encryption protocols.
Protecting Against Phishing Attacks
Users are advised to exercise caution when receiving unexpected messages, avoid scanning QR codes or linking devices to their accounts without verification, and never share verification codes with anyone, especially individuals claiming to be platform support representatives.
Remaining vigilant and skeptical of unsolicited requests can help mitigate the risk of falling victim to phishing attacks and unauthorized access to messaging accounts.
Source: FBI
Source: France’s Cyber Crisis Coordination Center (C4)
-

 Facebook6 months ago
Facebook6 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS
































