At the Autonomous Validation Summit (May 12 & 14), witness how autonomous, context-rich validation identifies exploitable loopholes, validates control efficacy, and completes the remediation process.
Secure Your Spot Now

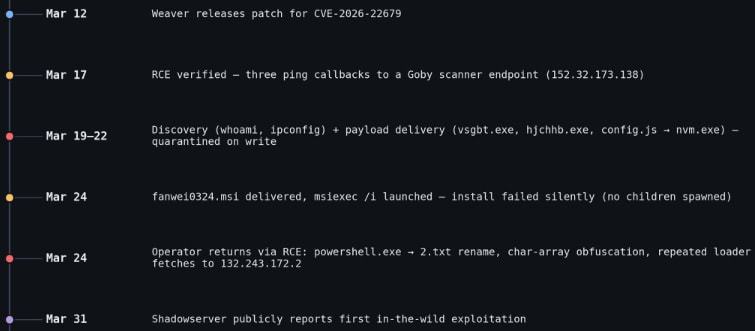
Since mid-March, hackers have been taking advantage of a critical vulnerability (CVE-2026-22679) in the Weaver E-cology office automation system to carry out discovery commands.
The attacks commenced just five days after the software vendor released a security update to fix the issue, and a mere two weeks before making it public.
Vega, a threat intelligence company, documented the malicious activities and noted that the attacks spanned about a week, each with distinct phases.
Weaver E-cology is a platform primarily utilized by Chinese organizations for enterprise office automation, collaboration, workflows, document management, HR, and internal business processes.
The critical unauthenticated remote code execution flaw, CVE-2026-22679, affects E-cology 10.0 builds released before March 12. The vulnerability stems from an exposed debug API endpoint that allows user-supplied parameters to reach backend Remote Procedure Call (RPC) functionality without proper authentication or input validation.
This loophole enables attackers to pass manipulated values that are eventually executed as system commands on the server, effectively transforming the endpoint into a remote command execution interface.
During the attacks, hackers attempted various tactics such as triggering ping commands, PowerShell-based payload downloads, and deploying an MSI installer, but these were thwarted by endpoint defenses.
Despite exploiting CVE-2026-22679 for remote code execution, the attackers did not establish a persistent session on the targeted host, according to Vega.
Users of Weaver E-cology 10.0 are strongly advised to promptly apply the security updates provided by the vendor to safeguard their systems.
Vega emphasized the importance of upgrading to the latest build (20260312) as it removes the debug endpoint entirely, preventing further exploitation.
No alternative mitigation measures or workarounds are mentioned in the official bulletin, making the update the sole recommendation for users.
An AI recently combined four zero-day vulnerabilities into a single exploit, bypassing both renderer and OS sandboxes. This development hints at a wave of new exploits on the horizon.

At the Autonomous Validation Summit (May 12 & 14), witness how autonomous, context-rich validation identifies exploitable loopholes, validates control efficacy, and completes the remediation process.
Secure Your Spot Now


EU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules


Warning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos


Facebook’s New Look: A Blend of Instagram’s Style
Facebook Compliance: ICE-tracking Page Removed After US Government Intervention


Facebook and Instagram to Reduce Personalized Ads for European Users


InstaDub: Meta’s AI Translation Tool for Instagram Videos


Reclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery


Meta discontinues Messenger apps for Windows and macOS
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.