Security
Undercover Discovery: Uncovering the BlueHammer Windows Zero-Day Breach
Disgruntled Researcher Leaks “BlueHammer” Windows Zero-Day Exploit
An unpatched Windows privilege escalation flaw has had exploit code released after being privately reported to Microsoft. This flaw allows attackers to gain SYSTEM or elevated administrator permissions.
Known as BlueHammer, this vulnerability was made public by a security researcher who was dissatisfied with how Microsoft’s Security Response Center (MSRC) handled the disclosure process.
As there is no official patch or update to address the security issue, Microsoft classifies it as a zero-day vulnerability.

The reason behind the public release of the exploit code remains unclear. In a brief post under the pseudonym Chaotic Eclipse, the researcher stated, “I was not bluffing Microsoft, and I’m doing it again.”
“Unlike previous times, I’m not explaining how this works; y’all geniuses can figure it out. Also, huge thanks to MSRC leadership for making this possible,” the researcher added.
On April 3rd, Chaotic Eclipse published a GitHub repository for the BlueHammer vulnerability exploit under the alias Nightmare-Eclipse, expressing disbelief and frustration with Microsoft’s handling of the security issue.
“I’m just really wondering what was the math behind their decision, like you knew this was going to happen and you still did whatever you did? Are they serious?”
The researcher also mentioned that the proof-of-concept (PoC) code may contain bugs that could hinder its reliable operation.
Will Dormann, principal vulnerability analyst at Tharros (formerly Analygence), confirmed that the BlueHammer exploit works. He explained that the flaw is a local privilege escalation (LPE) that combines a TOCTOU (time-of-check to time-of-use) and a path confusion.
According to Dormann, the issue is challenging to exploit and provides a local attacker access to the Security Account Manager (SAM) database, which contains password hashes for local accounts.
With this access, attackers can escalate to SYSTEM privileges and potentially compromise the entire machine.
“At that point, [the attackers] basically own the system, and can do things like spawn a SYSTEM-privileged shell,” Dormann told BleepingComputer.
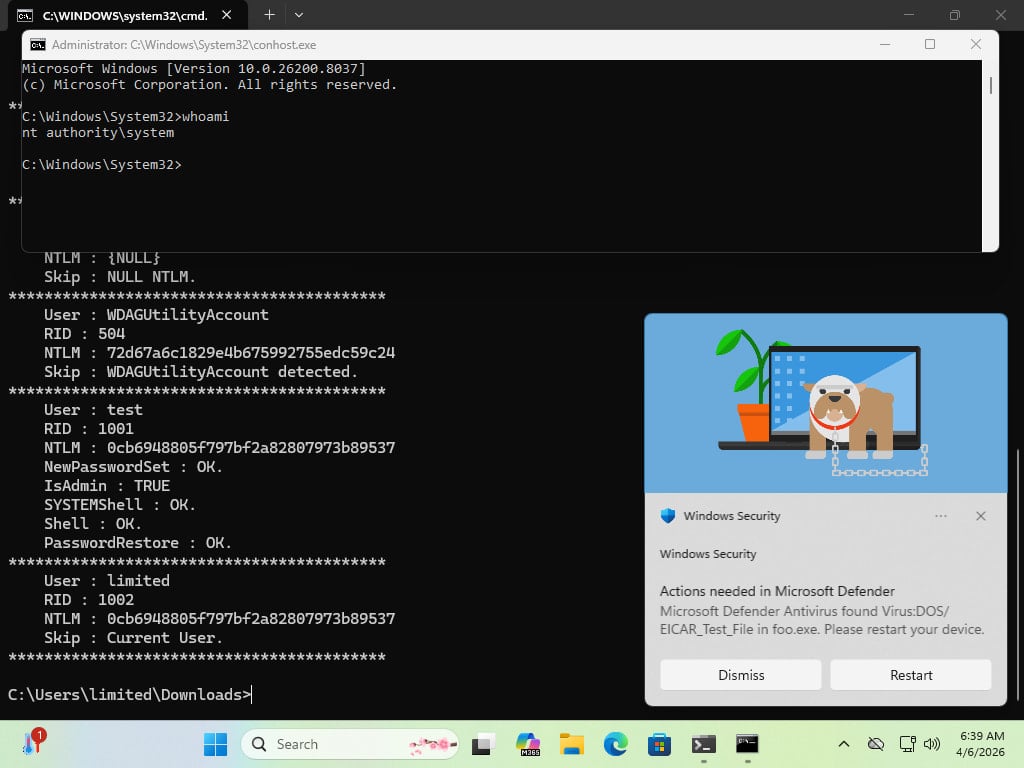
Source: Will Dormann
Some researchers testing the exploit confirmed that the code was not successful on Windows Server, supporting Chaotic Eclipse’s statement about potential bugs affecting its functionality.
Dormann added that on the Server platform, the BlueHammer exploit elevates permissions from non-admin to elevated administrator, a protection mechanism that requires user authorization for operations needing full system access.
While the motivation behind Chaotic Eclipse/Nightmare-Eclipse’s disclosure remains uncertain, Dormann highlighted that MSRC requires a video of the exploit when submitting a vulnerability report.
Although this requirement may aid Microsoft in managing reported vulnerabilities more efficiently, it adds complexity to submitting a valid report.
Despite BlueHammer requiring a local attacker for exploitation, the risk it poses is considerable as hackers can gain local access through various vectors, including social engineering, leveraging other software vulnerabilities, or credential-based attacks.
BleepingComputer reached out to Microsoft for a comment on the BlueHammer flaw but did not receive a response by publication time.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS