Security
Strengthening Threat Intelligence Operations: Criminal IP and Securonix ThreatQ Join Forces

Enhancing Threat Intelligence Integration with Criminal IP and ThreatQ
Partnering with Securonix, Criminal IP brings its Threat Intelligence into ThreatQ, enabling organizations to seamlessly integrate external IP intelligence into their existing workflows. This integration aids security teams in expediting analysis and response by providing more actionable context.
Unlike conventional intelligence feeds, Criminal IP offers visibility into the exposure of assets and infrastructure across the internet. By seamlessly embedding this data into ThreatQ, organizations can infuse real-world context into their investigations without disrupting current processes.
ThreatQ serves as a centralized platform for consolidating and prioritizing threat data from various sources. With the integration of Criminal IP, organizations can enrich this data with continuously updated exposure-based intelligence, enhancing investigation and response workflows without introducing additional complexity.
Scalable Automated Intelligence Enrichment
Operating within the integrated environment, Criminal IP’s threat intelligence APIs automatically enrich incoming IP indicators in ThreatQ with contextual information such as maliciousness scoring, VPN and proxy detection, remote access exposure, open ports, and known vulnerabilities.
Empowered by ThreatQ’s data-driven orchestration engine, organizations can configure automated workflows that consistently assess incoming indicators against Criminal IP’s threat database.
This automated process ensures that threat context remains up-to-date without necessitating manual analyst intervention, facilitating quicker triage and more uniform prioritization.
Integrate Criminal IP’s exposure-based threat intelligence into ThreatQ to enrich IP indicators with real-time context.
Automate analysis with maliciousness scoring, VPN/proxy detection, and infrastructure insights to expedite investigation and response within a unified workflow. Explore Criminal IP Integration
Real-Time Investigation Within a Unified Workspace
enabling unified visibility into enriched indicators and risk context
This integration empowers analysts to access Criminal IP intelligence directly within the ThreatQ interface, facilitating real-time validation of suspicious IP activity without the need to switch between tools. By amalgamating exposure data with infrastructure-level insights, teams can more effectively assess risks within their existing workflows.
Analysts can also conduct on-demand Criminal IP lookups directly from indicator detail views or investigation boards, granting immediate access to additional context during active investigations.
Criminal IP further enhances ThreatQ’s investigation graph by unveiling relationships between IP addresses, associated infrastructure, and attack activity, aiding analysts in comprehending connections and patterns across threats.
Intelligence-Driven Prioritization and Response
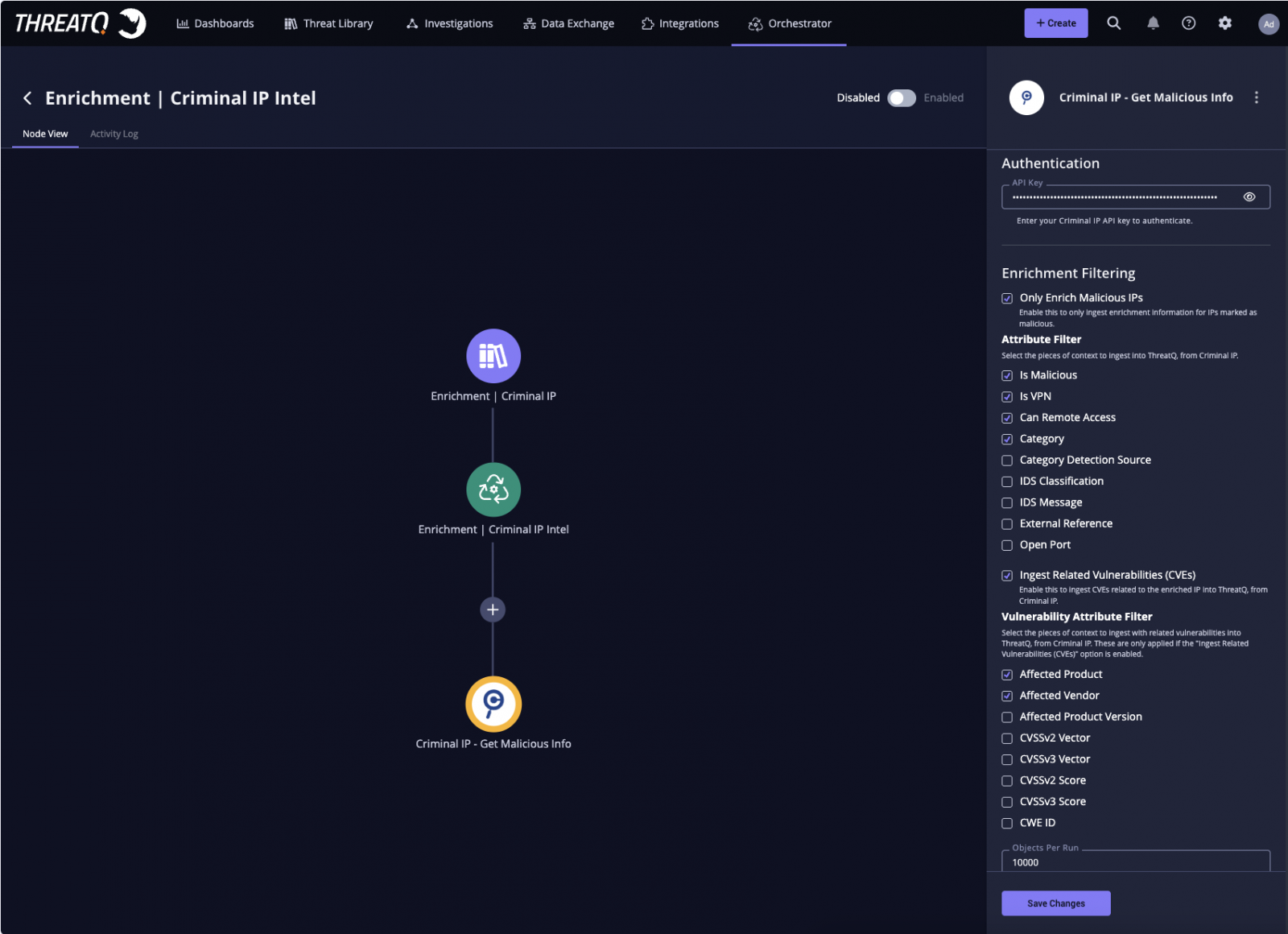
enabling automated ingestion and filtering of exposure-based IP intelligence directly into analysis workflows
By integrating Criminal IP’s intelligence into ThreatQ’s scoring framework, organizations can align risk assessment with their specific operational environment. This alignment allows for more precise prioritization and supports more effective decision-making during investigations.
Enriched data can also be visualized through dashboards, offering clearer insights into maliciousness trends, VPN usage, and risk distribution across indicators.
Expanding Visibility with Exposure Intelligence
The collaboration underscores the increasing significance of exposure-based intelligence in contemporary threat analysis. Through continuous monitoring and analysis of internet-facing assets and IP infrastructure, Criminal IP delivers differentiated visibility that surpasses traditional indicator-based approaches.
“This integration enables organizations to seamlessly incorporate IP reputation and exposure intelligence into the ThreatQ platform, enhancing analysis speed and response effectiveness throughout the investigation lifecycle,” stated Byungtak Kang, CEO of Criminal IP. “By integrating our intelligence into existing workflows, security teams can enhance visibility and make well-informed decisions without introducing operational complexities.”
“This partnership enhances the role of IP intelligence in pivotal investigation and decision-making stages,” remarked Scott Sampson, Chief Revenue Officer at Securonix. “By merging ThreatQ’s orchestration and prioritization capabilities with Criminal IP’s real-time threat data, organizations can accelerate enrichment processes, reduce manual workloads, and concentrate on the most pertinent threats within their environment.”
Through this collaboration, Criminal IP and Securonix enable security teams to effectively operationalize threat intelligence by integrating automated enrichment, workflow orchestration, and precise prioritization within the ThreatQ platform.
About Criminal IP
Criminal IP, a cyber threat intelligence solution operated by AI SPERA, furnishes decision-ready IP address and domain reputation data to security teams globally.
By continuously scanning the global internet, Criminal IP aggregates and contextualizes threat signals across IPs, domains, URLs, and attack infrastructure, encompassing malicious indicators, known vulnerabilities, exposed assets, and attacker behavior.
Criminal IP’s mission is to provide organizations with genuine visibility into their cyber landscape and accelerate threat detection and response by furnishing the intelligence necessary to outmaneuver attackers. For more details, visit www.criminalip.io.
About Securonix
Securonix is revolutionizing security operations with the industry’s pioneering Unified Defense SIEM with Agentic AI, designed to decide and act across the threat lifecycle with a human-in-the-loop approach. Its cloud-native platform consolidates detection, investigation, and response while enabling Sam, the AI SOC Analyst, and a productivity-based AI operating model for the SOC, allowing organizations to gauge and govern AI by the analyst work it delivers.
Assisting enterprises in becoming Breach Ready and Board Ready, Securonix delivers accountable, outcome-driven security operations at scale. Acknowledged as a Leader in the Gartner® Magic Quadrant™ for SIEM and a Customers’ Choice by Gartner Peer Insights™, Securonix offers trusted security operations for global enterprises. Learn more at www.securonix.com.
Sponsored and authored by Criminal IP.
-

 Facebook6 months ago
Facebook6 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple6 months ago
Apple6 months agoMeta discontinues Messenger apps for Windows and macOS