Security
Rampant MongoDB Vulnerabilities Exploited in Ongoing Data Extortion Campaigns

Exposed MongoDB Instances Targeted in Data Extortion Attacks
A cyber threat actor has been actively targeting vulnerable MongoDB instances in automated data extortion schemes, demanding small ransom payments from affected owners to restore their data.
The attacker specifically focuses on exploiting insecure databases that can be accessed without any restrictions due to misconfigurations. As a result, approximately 1,400 exposed servers have been compromised, with ransom demands averaging around $500 in Bitcoin.
Recent reports indicate a surge in these attacks, with thousands of databases being deleted and ransom requests made to recover the information. In some cases, databases were deleted without any monetary demands.

A recent penetration testing exercise conducted by cybersecurity experts from Flare revealed a continuation of these attacks, albeit on a smaller scale.
The researchers identified over 208,500 publicly exposed MongoDB servers, out of which 100,000 revealed operational details, and 3,100 were accessible without authentication.
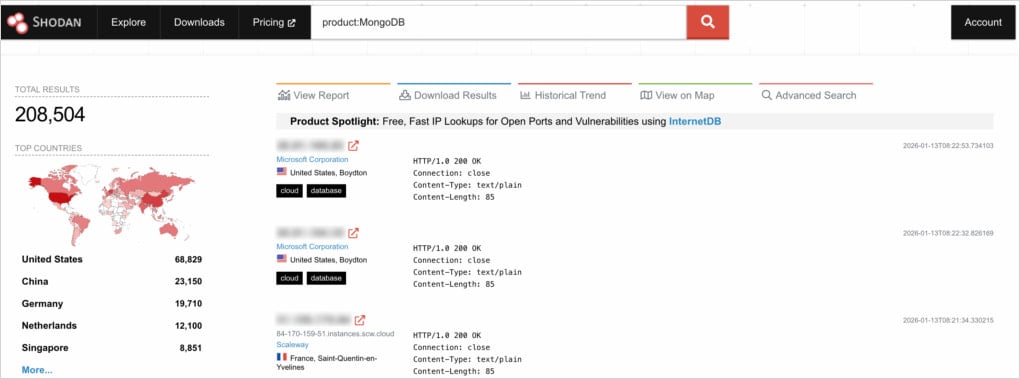
Source: Flare
Alarmingly, almost half of the unprotected servers had already fallen victim to attacks, resulting in data deletion and ransom demands.
Analysis of the ransom notes indicated a common demand of 0.005 BTC within a 48-hour window. However, there is no assurance that paying the ransom will guarantee data recovery or access to decryption keys.
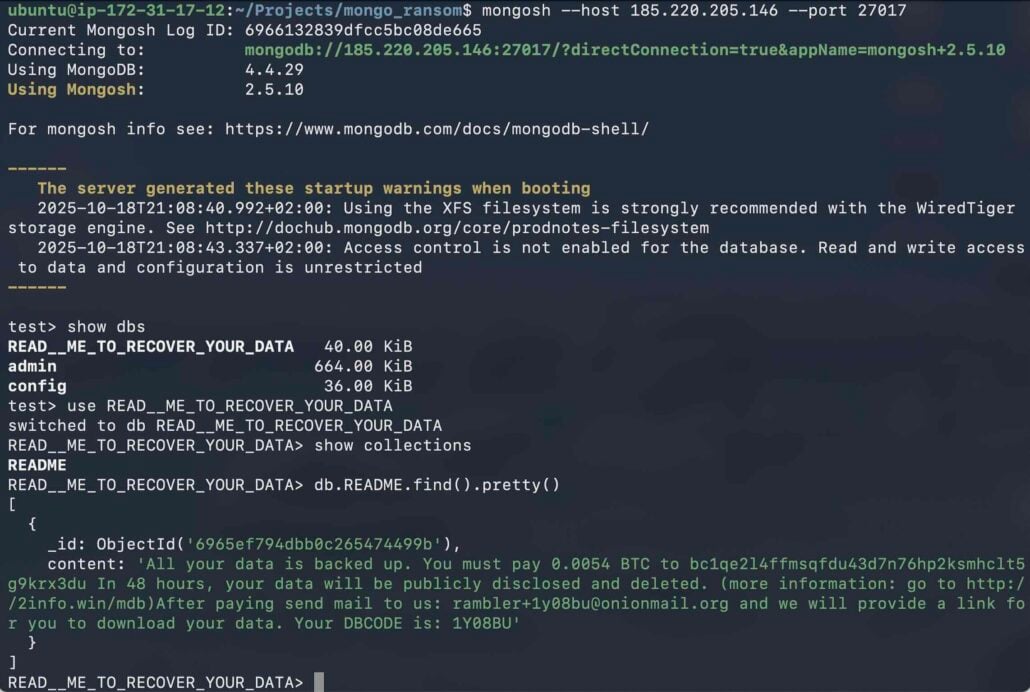
Source: Flare
Further investigation revealed only five unique wallet addresses across the ransom notes, with one address being predominant in nearly 98% of cases, indicating a single threat actor behind these malicious activities.
Flare also speculated that some exposed but untouched instances might have already paid ransoms to avoid being targeted by attackers.
In addition to weak authentication measures, researchers highlighted that almost 95,000 of the exposed MongoDB servers were running outdated versions vulnerable to known exploits. While most vulnerabilities led to denial-of-service risks, remote code execution threats were limited.

Source: Flare
Flare recommends that MongoDB administrators refrain from exposing instances publicly unless absolutely necessary, implement robust authentication protocols, enforce firewall rules, and utilize Kubernetes network policies to restrict access to trusted sources. They also advise against blindly copying configurations from deployment guides.
Regular updates should be applied to MongoDB installations, with continuous monitoring for potential exposure. In case of a breach, credentials must be changed, and logs should be reviewed for unauthorized activities.

Modern IT infrastructure evolves rapidly, outpacing manual workflows. Learn how to streamline operations, enhance reliability, and automate responses with Tines’ comprehensive guide.
-

 Facebook6 months ago
Facebook6 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS