


Ghanaian National Pleads Guilty in $100 Million Fraud Ring A Ghanaian individual has admitted to his involvement in a significant fraud scheme that defrauded victims in...
into plain text. “Telegram serves as a mobilization and propaganda amplifier for hacktivists, while state-aligned operations use it as a rapid distribution channel for narratives and...



Fake OpenClaw GitHub Repositories Promote Malware, Targeting Users A recent discovery by researchers at Huntress revealed a troubling trend in the cybersecurity landscape. Fake OpenClaw installers...



In 2025, Google’s Threat Intelligence Group (GTIG) monitored and recorded 90 instances of zero-day vulnerabilities being actively exploited, with nearly half of them targeting enterprise software...



Anthropic CEO Negotiating with Department of Defense to Salvage Relationship Reports indicate that Anthropic CEO Dario Amodei is back at the negotiating table with the Department...



Cisco has identified two new security vulnerabilities in Catalyst SD-WAN Manager that are actively being exploited, prompting administrators to update vulnerable devices for enhanced protection. Catalyst...

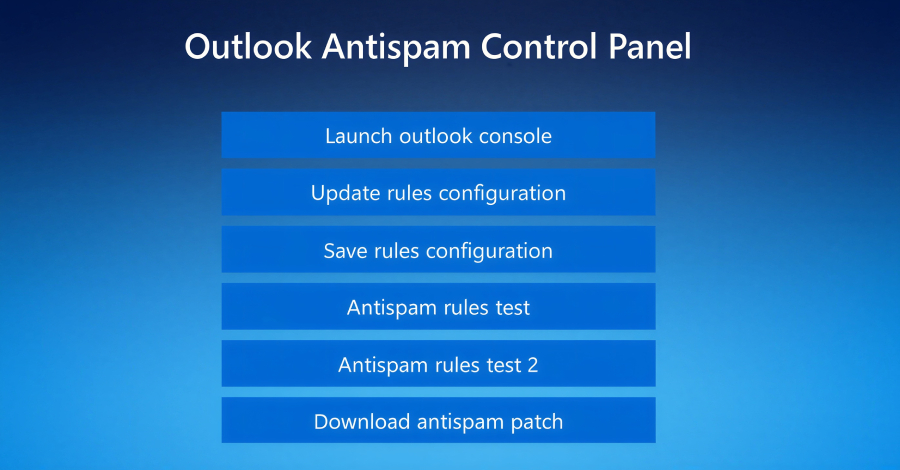
Microsoft has issued a warning regarding sophisticated phishing campaigns that leverage OAuth URL redirection techniques to bypass traditional email and browser security measures. The primary targets...



Bitwarden Introduces Phishing-Resistant Authentication for Windows 11 Devices Bitwarden has recently unveiled a new feature that allows users to log into Windows 11 devices using passkeys...

Uncovering a New Threat: Fake IT Support Used to Deliver Havoc Command-and-Control Framework A recent campaign has caught the attention of threat hunters, revealing a disturbing...



The Cybersecurity and Infrastructure Security Agency (CISA) in the United States recently added a vulnerability in VMware Aria Operations, identified as CVE-2026-22719, to its list of...
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.