Uncovering a New Threat: Fake IT Support Used to Deliver Havoc Command-and-Control Framework
A recent campaign has caught the attention of threat hunters, revealing a disturbing tactic where cybercriminals posed as fake IT support to deploy the Havoc command-and-control (C2) framework. This deceptive strategy served as a precursor to potential data exfiltration or ransomware attacks, showcasing the evolving sophistication of cyber threats.
Identified by Huntress across five partner organizations, these intrusions involved a multi-layered approach that began with email spam lures and progressed to phone calls from fraudulent IT desks. The attackers swiftly moved from initial access to compromising additional endpoints, utilizing a mix of custom Havoc Demon payloads and legitimate remote monitoring and management (RMM) tools for persistence.
The speed and efficiency with which the threat actors operated strongly indicate their intent to carry out data exfiltration, ransomware attacks, or both. This modus operandi shares similarities with previous tactics employed by threat actors linked to the Black Basta ransomware operation, underscoring the ongoing threat posed by cybercriminal groups.
A Familiar Playbook: Email Bombing, Phishing, and Social Engineering
The attack chain initiated with a spam campaign designed to inundate targets with junk emails, followed by personalized phone calls from the fake IT support team. By convincing victims to grant remote access to their machines, the threat actors were able to execute their malicious payload seamlessly.
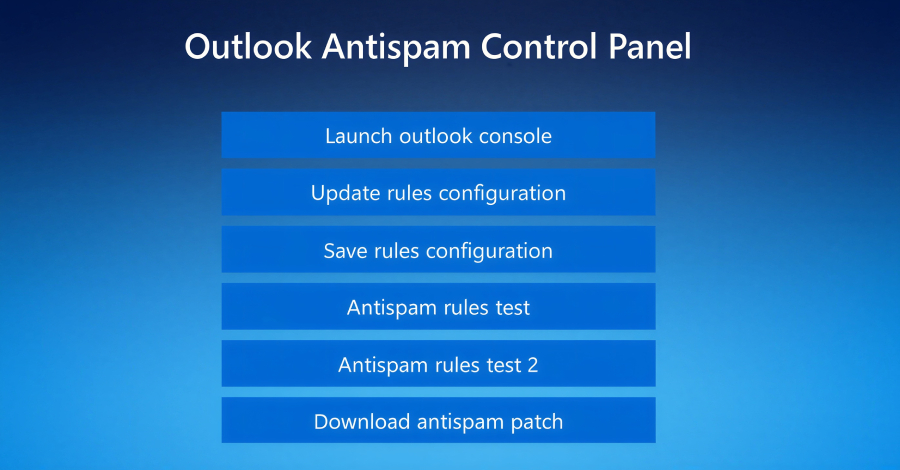
One notable aspect of this campaign is the utilization of a fake landing page hosted on Amazon Web Services (AWS) that mimics Microsoft’s interface. This page prompts users to enter their email address to access an alleged anti-spam rules update system, leading them to unknowingly disclose their credentials.
Upon clicking the “Update rules configuration” button, a script is triggered, prompting users to enter their password. This deceptive tactic not only harvests credentials but also adds a layer of authenticity to the interaction, enhancing the illusion of legitimacy.
Sophisticated Malware Delivery and Defense Evasion Techniques
The attack further progresses with the download of a supposed anti-spam patch, which triggers the execution of a legitimate binary that sideloads a malicious DLL. This DLL payload implements defense evasion mechanisms and executes the Havoc shellcode payload, allowing the threat actors to establish a foothold in the victim’s environment.
Additionally, the attackers employ advanced techniques such as control flow obfuscation, timing-based delay loops, and hooking ntdll.dll functions to bypass security software and endpoint detection and response (EDR) solutions. This intricate approach enables the threat actors to maintain persistence and facilitate lateral movement within the compromised network.
Key Takeaways and Insights
These attacks highlight several important trends in cyber threats, including the willingness of threat actors to impersonate IT personnel to enhance their success rate. Furthermore, the customization of commodity malware to evade detection and the rapid progression of attacks from initial compromise to full network infiltration underscore the evolving nature of cybersecurity threats.
It is crucial for organizations to remain vigilant and implement robust security measures to mitigate the risks posed by such sophisticated attacks. By understanding the tactics employed by cybercriminals and staying informed about emerging threats, businesses can better protect their assets and data from malicious actors.
Ultimately, the evolving landscape of cyber threats necessitates a proactive and adaptive approach to cybersecurity, as demonstrated by the intricate layers of sophistication observed in this recent campaign. By staying ahead of emerging threats and implementing comprehensive security protocols, organizations can safeguard their digital assets and mitigate the impact of cyber attacks.