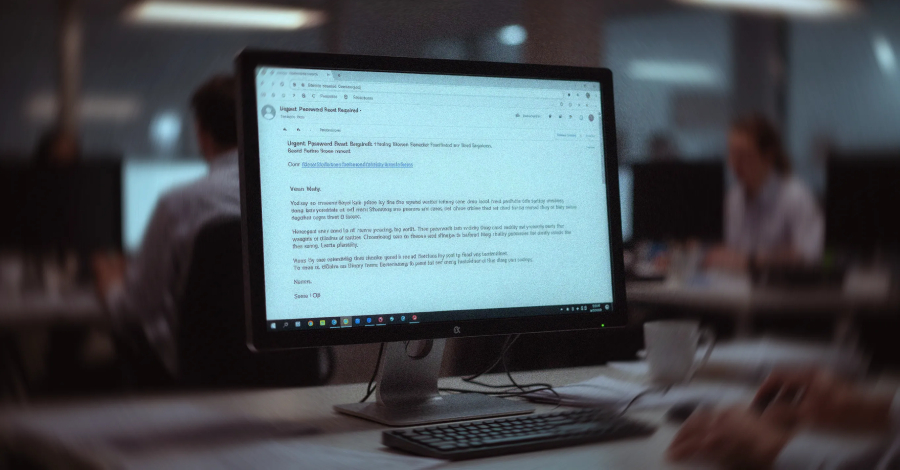

An Overview of the VENOMOUS#HELPER Phishing Campaign A sophisticated phishing campaign, known as VENOMOUS#HELPER, has been actively targeting various organizations since April 2025. This campaign utilizes...
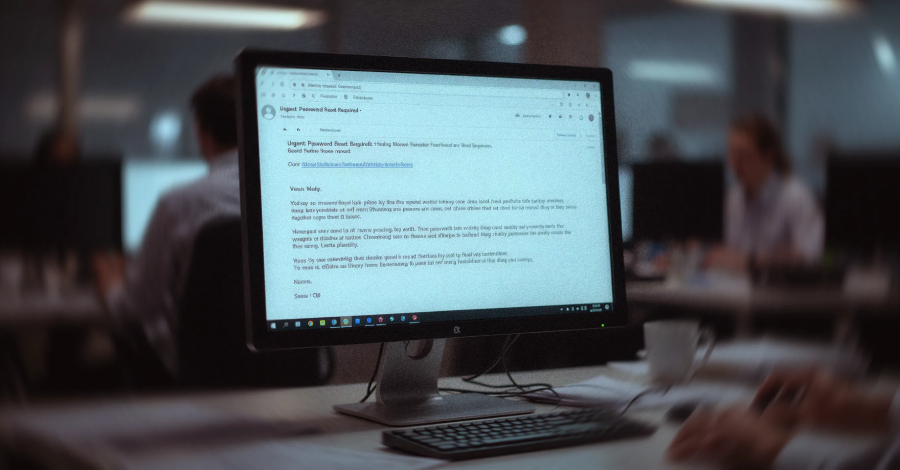

An ongoing phishing scheme has been identified targeting various organizations since April 2025, utilizing legitimate Remote Monitoring and Management (RMM) software to establish continuous remote access...



An Iran-focused threat actor is believed to be responsible for a password-spraying campaign targeting Microsoft 365 environments in Israel and the United Arab Emirates amidst ongoing...
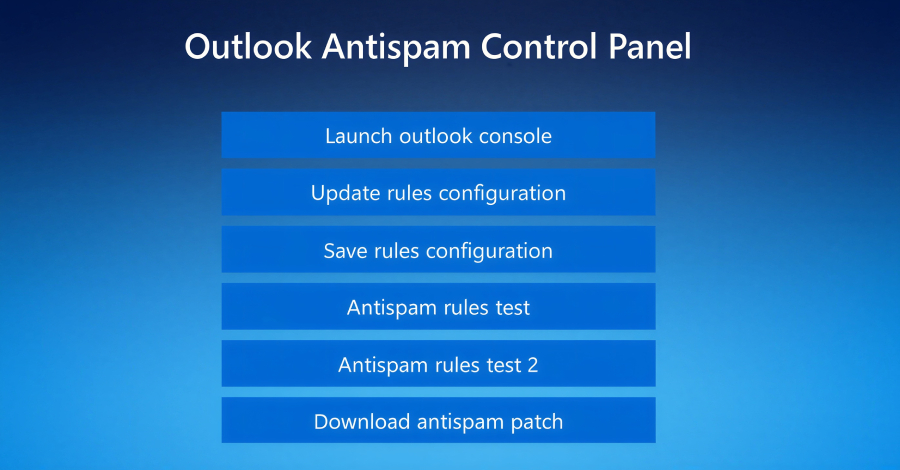

Uncovering a New Threat: Fake IT Support Used to Deliver Havoc Command-and-Control Framework A recent campaign has caught the attention of threat hunters, revealing a disturbing...



In the digital age, customer experience (CX) platforms play a crucial role in processing vast amounts of unstructured data. This includes survey responses, online reviews, social...

React2Shell Vulnerability Exposes Over 77,000 IP Addresses to Attacks With the recent disclosure of the critical React2Shell remote code execution flaw (CVE-2025-55182), over 77,000 Internet-exposed IP...



A state-sponsored Iranian hacker group known as MuddyWater has conducted cyberattacks on more than 100 government entities using the Phoenix backdoor version 4. Referred to by...



Chinese Hackers Exploit ToolShell Vulnerability in Microsoft SharePoint Recent cyber attacks targeting government agencies, universities, telecommunication service providers, and finance organizations have been linked to hackers...



Oracle E-Business Suite Under Attack: A Zero-Day Exploitation A recent report by Google Threat Intelligence Group (GTIG) and Mandiant reveals that numerous organizations have fallen victim...
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.