Security
Alert: FBI Seeks Victims of Malware Spread Through Steam Games

The Federal Bureau of Investigation (FBI) is reaching out to gamers who unknowingly downloaded Steam games containing malware as part of an ongoing investigation into eight malicious games that were uploaded to the popular gaming platform.
In a statement released by the FBI’s Seattle Division, the agency is seeking to identify individuals who may have been impacted by installing one of these malicious games on Steam between May 2024 and January 2026.
The FBI’s notice states, “The FBI’s Seattle Division is seeking to identify potential victims who installed Steam games embedded with malware. The FBI suspects that the threat actor targeted users specifically between May 2024 and January 2026.”
The identified malicious games include BlockBlasters, Chemia, Dashverse/DashFPS, Lampy, Lunara, PirateFi, and Tokenova.
If you or your dependent(s) were affected by installing one of these games or have any information relevant to the investigation, you are urged to fill out a short form provided by the FBI.
The FBI is particularly interested in instances of cryptocurrency theft and account hijacking following the installation of the malware. The questionnaire includes inquiries about cryptocurrency transactions, compromised accounts, and stolen funds.
Furthermore, the form requests any screenshots of communications with individuals who promoted the malicious games, as this information could aid investigators in tracking the stolen cryptocurrency and identifying those responsible for distributing the malware.
The FBI emphasized the confidentiality of victim identities, stating that victims may be eligible for certain services, restitution, and rights under federal and/or state law.
Additionally, the FBI has requested anyone who knows individuals affected by these events to encourage them to contact Steam_Malware@fbi.gov for further assistance.
BleepingComputer reached out to Valve for comments on the investigation but did not receive a response.
Malware Concealed in Steam Games
Over the past two years, multiple malicious games discovered on Steam have been found to distribute information-stealing malware designed to extract credentials, cryptocurrency wallets, and other sensitive data from players’ devices.
One notable case involved BlockBlasters, a free-to-play 2D platformer available on Steam from July to September 2024. Initially uploaded as a clean program, the game was later infected with cryptodrainer malware.
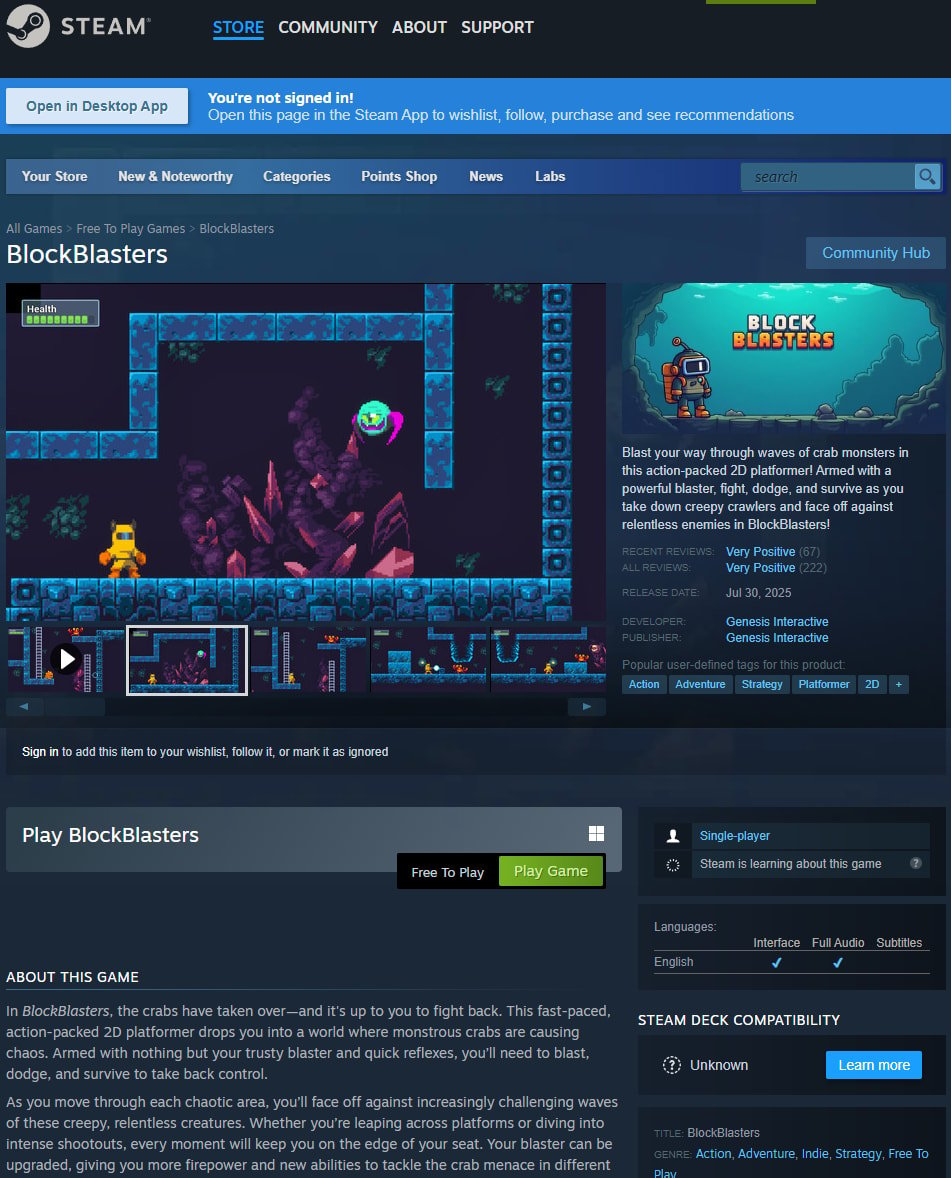
The discovery that the Steam game was malicious came to light during a livestream by video game streamer Raivo Plavnieks (RastalandTV), who was raising funds for cancer treatment.
After downloading the game from Steam, the streamer reported a loss of over $32,000 from his cryptocurrency wallet.
Subsequent investigations revealed that attackers had stolen approximately $150,000 from 261 Steam accounts. Cybersecurity researcher VX-Underground reported an even higher count of 478 victims.
In another case, the game Chemia, a survival crafting game, was found to contain the HijackLoader malware, which downloaded the Vidar information stealer. It was later discovered that the game also installed EncryptHub’s custom Fickle Stealer malware, which targeted credentials, browser data, cookies, and cryptocurrency wallets.
Similarly, the game PirateFi distributed the Vidar infostealer and was available on Steam for about a week in February 2025, with up to 1,500 users potentially downloading the game before its removal from the platform.
Steam advised players who launched the game to run antivirus scans, review installed software, and consider reinstalling their operating systems due to the potential execution of malicious files on their computers.

Malware tactics are evolving. The Red Report 2026 details how new threats leverage mathematics to evade detection and operate covertly.
Access our analysis of 1.1 million malicious samples to uncover the top 10 techniques and assess the effectiveness of your security measures.
-

 Facebook6 months ago
Facebook6 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple6 months ago
Apple6 months agoMeta discontinues Messenger apps for Windows and macOS