Security
German Authorities Uncover REvil and GandCrab Ransomware Kingpins

German Authorities Uncover Leaders of REvil and GangCrab Ransomware Operations
The Federal Police in Germany, known as the BKA, has made a breakthrough in identifying the masterminds behind the notorious GandCrab and REvil ransomware attacks. The culprits, identified as 31-year-old Daniil Maksimovich Shchukin and 43-year-old Anatoly Sergeevitsch Kravchuk, were revealed to have orchestrated these cyber operations between 2019 and 2021.
According to the BKA, Shchukin and Kravchuk assumed leadership roles within the ransomware groups from the beginning of 2019 until at least July 2021. Shchukin, under the aliases UNKN/UNKNOWN, actively engaged in cybercrime forums, representing the ransomware syndicate.

The German authorities disclosed that Shchukin and Kravchuk were involved in over 130 instances of extortion targeting companies in Germany specifically. These nefarious activities resulted in 25 victims paying a total of $2.2 million in ransom to the perpetrators, leading to an estimated financial loss exceeding $40 million.
The GandCrab ransomware operation, initiated in early 2018, was spearheaded by a leader who retired in June 2019 after claiming $2 billion in ransom payments. Despite the massive earnings, the leader cashed out with $150 million, purportedly investing in legitimate businesses.
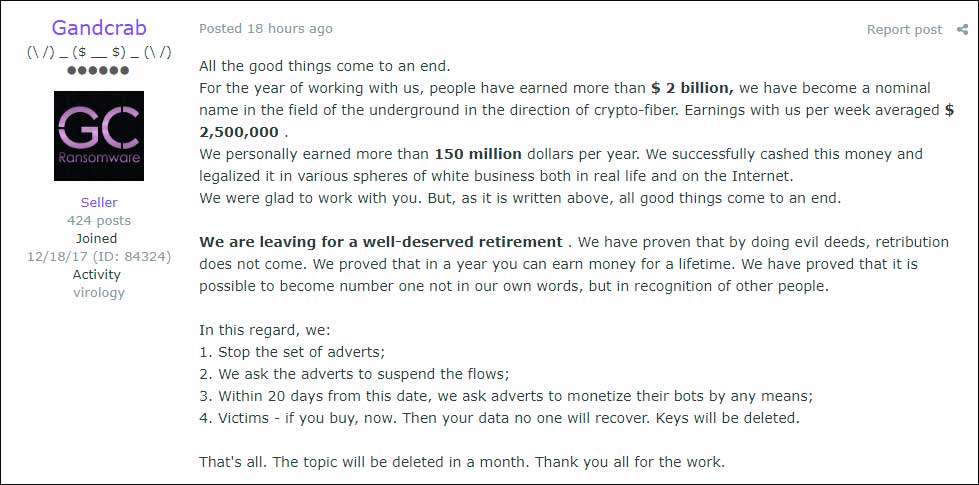
source: BleepingComputer
Subsequently, the emergence of REvil, also known as Sodinokibi, followed the affiliate model established by GandCrab. This new operation recruited cybercriminal affiliates and operators familiar with successful tactics, leading to the adoption of similar strategies in their operations.
REvil introduced public leak sites and conducted data auctions to coerce victims, targeting prominent entities such as multiple Texas local governments, tech giant Acer, and orchestrating the Kaseya supply-chain attack affecting around 1,500 downstream victims.
After the significant Kaseya breach, REvil temporarily halted operations for two months, during which law enforcement accessed their servers for monitoring purposes. This intervention led to the arrest of numerous REvil gang members by Russian authorities, with their subsequent release in 2025 after serving time on carding charges.
The status of Shchukin and Kravchuk’s involvement in other ransomware activities post-REvil’s downfall in 2021 remains uncertain. The BKA suspects that the duo is currently in Russia and urges the public to provide any information leading to their whereabouts. Entries have been listed on the EU’s Most Wanted portal, including tattoo images, to aid in their apprehension.

Automated pentesting demonstrates existing vulnerabilities, while BAS assesses control effectiveness. Many teams overlook one in favor of the other.
Explore this whitepaper that outlines six validation surfaces, identifies coverage gaps, and equips professionals with three pivotal questions for evaluating cybersecurity tools.
Law enforcement disruptions to REvil’s infrastructure were observed during this period. In mid-January 2022, Russia arrested over a dozen REvil members, subsequently released in 2025 after serving time for carding offenses.
It remains to be seen whether Shchukin and Kravchuk have transitioned into other ransomware ventures since the demise of REvil in 2021. The BKA’s pursuit continues, urging the public to aid in locating the two individuals and ensuring they face justice for their actions.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS