Security
AI Scanning Reveals Critical Security Vulnerability in Linux Copy Function
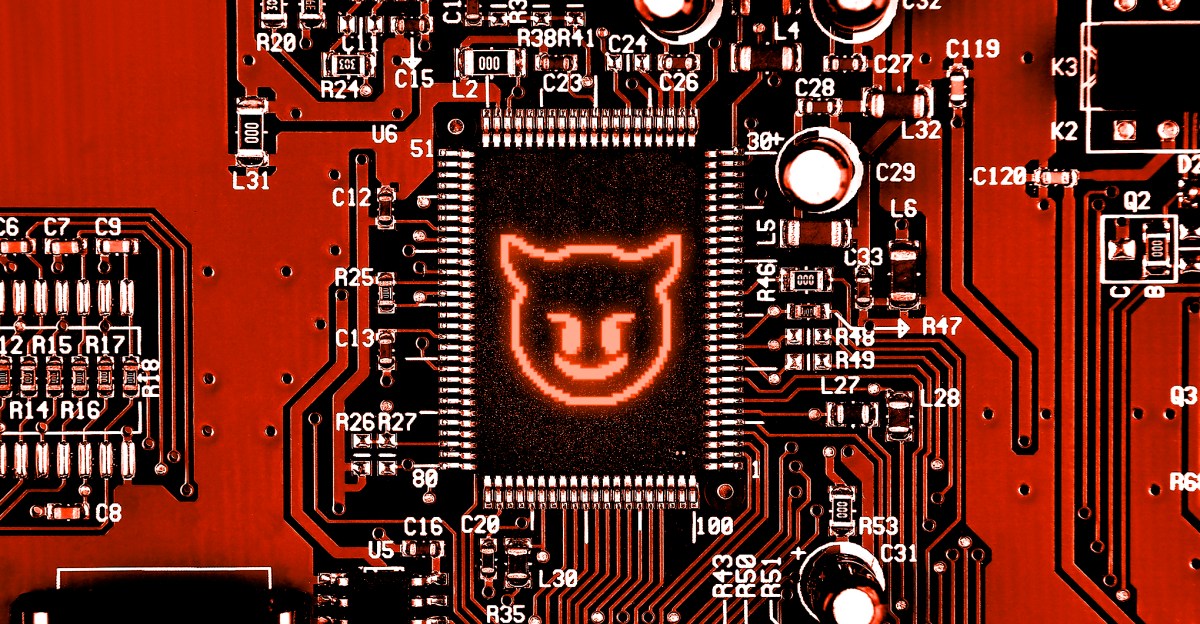
Linux Vulnerability: “Copy Fail” Allows Unauthorized Administrator Privileges
A critical security flaw known as “Copy Fail” has been discovered in nearly every Linux distribution released since 2017. This vulnerability, identified as CVE-2026-31431, enables any user to elevate their privileges to that of an administrator. The exploit, which has been publicly disclosed, utilizes a Python script that is effective across all affected Linux distributions. The security firm Theori, responsible for uncovering this vulnerability, stated that the exploit requires no per-distro offsets, version checks, or recompilation.
Ars Technica highlights a blog post by DevOps engineer Jorijn Schrijvershof, who describes the insidious nature of Copy Fail. This vulnerability is particularly concerning due to its ability to evade detection by monitoring tools. Page-cache corruption caused by Copy Fail does not mark affected pages as dirty, and the kernel’s writeback mechanism fails to flush modified bytes back to disk. Consequently, popular monitoring tools like AIDE, Tripwire, and OSSEC are unable to detect the exploit.
Theori’s researchers, assisted by their Xint Code AI tool, identified Copy Fail by examining the crypto subsystem of Linux. Through an automated scan devised by Taeyang Lee, multiple vulnerabilities, including Copy Fail, were discovered in a short period.
“This is the linux crypto/ subsystem. Please examine all codepaths reachable from userspace syscalls. Note one key observation: splice() can deliver page-cache references of read-only files (including setuid binaries) to crypto TX scatterlists.”
A patch addressing the Copy Fail vulnerability was integrated into the mainline Linux kernel on April 1st. However, the researchers behind the discovery chose to publicly disclose the exploit before all affected distributions could release patches. While some distributions like Arch Linux, RedHat Fedora, and Amazon Linux have issued patches, many others have yet to address the issue.
-

 Facebook6 months ago
Facebook6 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS