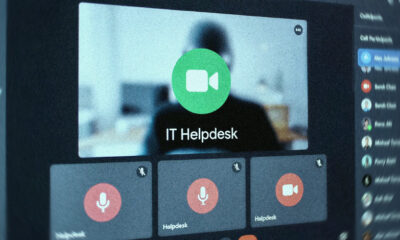
An ongoing phishing scheme has been identified targeting various organizations since April 2025, utilizing legitimate Remote Monitoring and Management (RMM) software to establish continuous remote access to compromised systems.
Known as VENOMOUS#HELPER, this campaign has impacted more than 80 entities, primarily in the United States, as reported by Securonix. It shares similarities with previously monitored groups by Red Canary and Sophos, with the latter referring to it as STAC6405. While the perpetrators remain unidentified, cybersecurity experts suggest it may be linked to a financially motivated Initial Access Broker (IAB) or a precursor to ransomware attacks.
According to researchers Akshay Gaikwad, Shikha Sangwan, and Aaron Beardslee, the attackers deploy customized SimpleHelp and ScreenConnect RMM tools to circumvent security measures, exploiting the unwitting victims who unknowingly install these legitimate tools.
By using both SimpleHelp and ScreenConnect, the attackers create a redundant dual-channel access system, ensuring uninterrupted operations even if one tool is detected and blocked.
The attack typically begins with a phishing email impersonating the U.S. Social Security Administration (SSA), prompting recipients to verify their email addresses and download an alleged SSA statement by clicking a link within the email. The link directs them to a compromised Mexican business website (“gruta.com[.]mx”), strategically chosen to evade email filters.

The fraudulent “SSA statement” is downloaded from another domain controlled by the attackers (“server.cubatiendaalimentos.com[.]mx”), containing an executable that delivers the SimpleHelp RMM tool. It is suspected that the attackers gained access to a single cPanel user account on the legitimate hosting server to host the malicious binary.
Upon opening the JWrapper-packaged Windows executable, the victim unknowingly installs malware that establishes itself as a Windows service with Safe Mode persistence. The malware includes a “self-healing watchdog” to ensure continuous operation, checks security products every 67 seconds, and monitors user activity every 23 seconds.
To enable complete desktop access, the SimpleHelp client obtains SeDebugPrivilege via AdjustTokenPrivileges, while leveraging “elev_win.exe” to gain SYSTEM-level privileges. This allows the attackers to view the screen, input keystrokes, and access user resources.
Subsequently, the elevated access is exploited to download and install ConnectWise ScreenConnect, offering an alternative communication channel if the SimpleHelp connection is disrupted.
“The deployed SimpleHelp version (5.0.1) provides extensive remote administration capabilities, allowing the attacker to execute commands silently, transfer files, and move laterally within the victim’s network undetected by traditional security measures,” note the researchers.