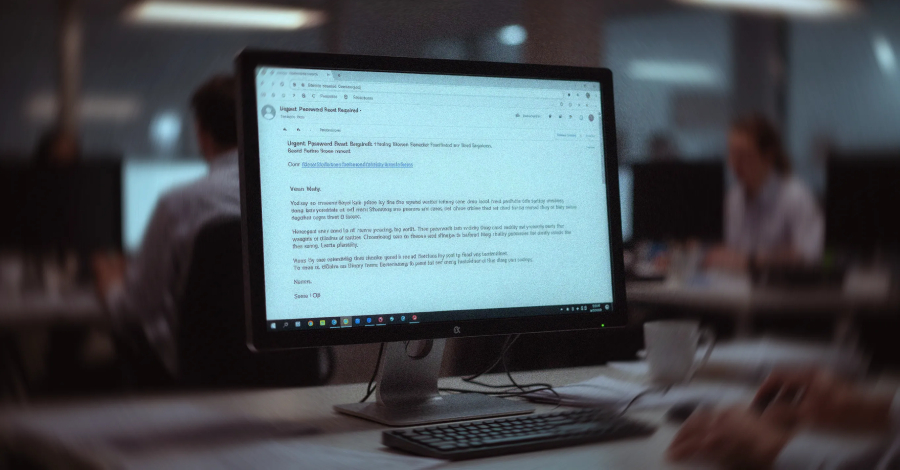

An Overview of the VENOMOUS#HELPER Phishing Campaign A sophisticated phishing campaign, known as VENOMOUS#HELPER, has been actively targeting various organizations since April 2025. This campaign utilizes...
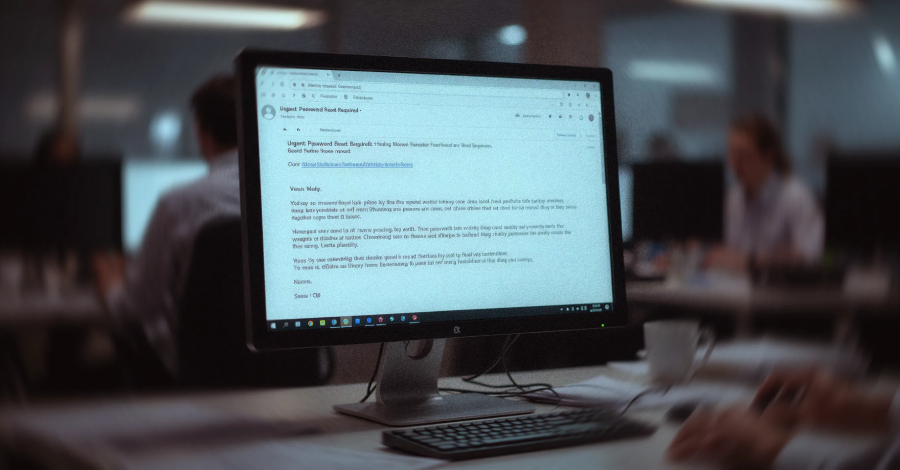

An ongoing phishing scheme has been identified targeting various organizations since April 2025, utilizing legitimate Remote Monitoring and Management (RMM) software to establish continuous remote access...



Adversaries infiltrated over 90 organizations in 2025 by injecting malicious prompts into legitimate AI tools, resulting in the theft of credentials and cryptocurrency. These compromised tools...



Cloud migration can be a challenging process, especially when teams are not only moving workloads but also aiming to make every environment reproducible and deployment-ready through...



Revolutionizing Marketing with AI: The Success Story of Hightouch Traditionally, marketers heavily relied on designers and creative professionals to produce images and videos for personalized online...



Whether you are already running a business or preparing to launch one, building a startup is exciting but scaling it can feel complex and demanding. The...


Qilin and Warlock Ransomware Operations Utilize BYOVD Technique to Evade Security Tools Recent reports from Cisco Talos and Trend Micro have uncovered a new tactic employed...



The Changing Landscape of AI Security CrowdStrike CEO George Kurtz recently emphasized in his keynote at RSA Conference 2026 that the fastest recorded adversary breakout time...



Financial markets have witnessed a significant shift with the rise of artificial intelligence in predictive tools. The accuracy of these tools is now under intense scrutiny...



The Importance of Navigating Conflict in Building a Strong Company Culture In any founding team, conflict is inevitable and can be beneficial if managed effectively. However,...
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.