Security
Uncovering Invisible Threats: Bridging the Security Gap in Your Toolkit

Following a comprehensive security test conducted by your IT team, your network is now secure. Multi-factor authentication is enforced across your organization’s tech stack, and employees have completed anti-phishing training.
However, a seemingly harmless action by Bob from Finance, who shared Q3 revenue projections via a Google Sheets link set to “anyone with the link can edit”, has the potential to become a major security vulnerability for your entire system.
While insider threats often involve disgruntled employees stealing data, the more common scenario involves well-meaning individuals like Bob resorting to using spreadsheets due to limitations in approved tools.
Although robust ERP software may address 90% of users’ needs, the remaining 10% – such as customizing charts or exporting reports to PDF – often leads individuals to export data to spreadsheets, creating what is known as a ‘shadow spreadsheet’.
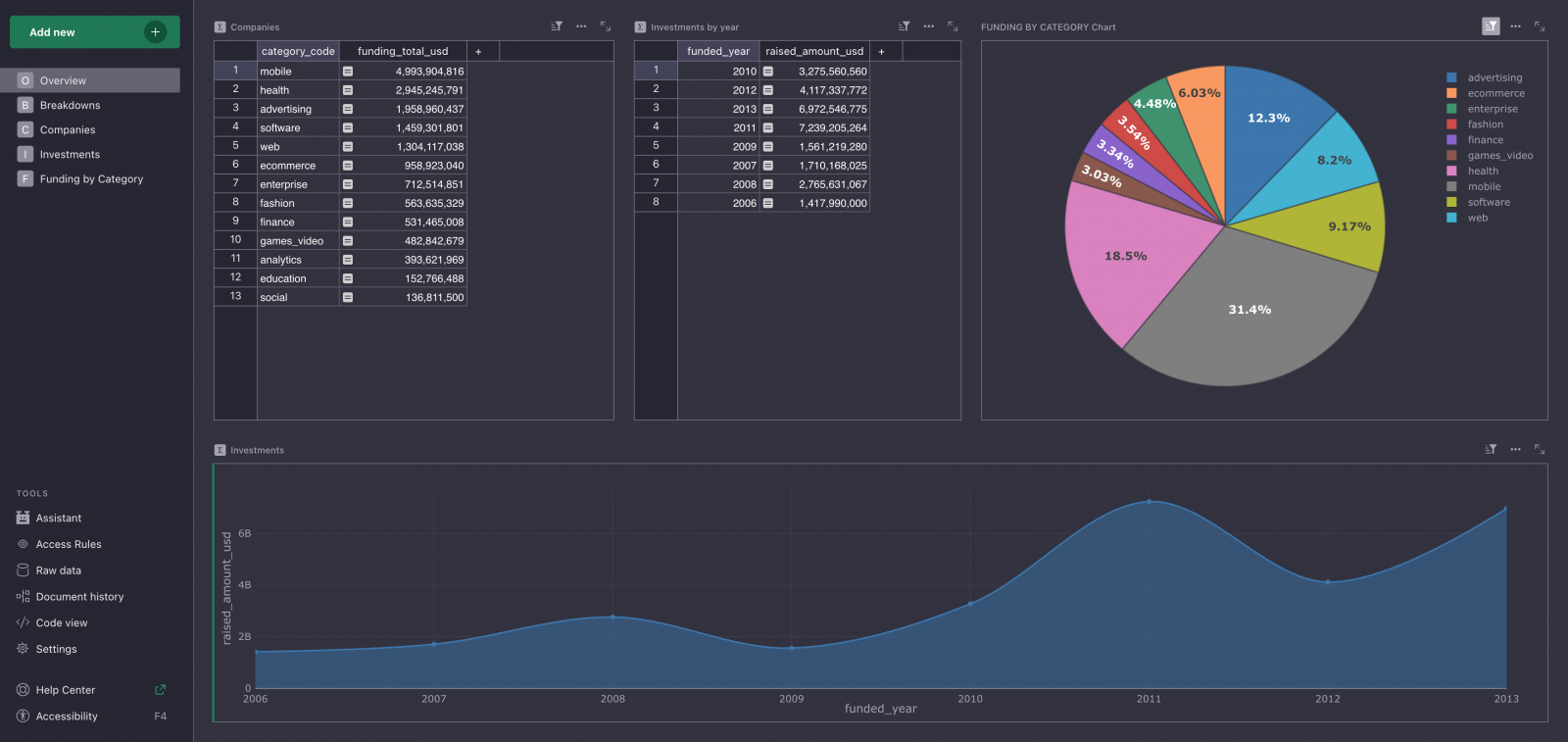
Dealing with shadow spreadsheets is a daily challenge for IT teams, which is why Grist Labs has developed an open-source spreadsheet-database solution to eliminate these risks.
How a shadow spreadsheet poses a security risk
When critical data is moved to spreadsheets, two common scenarios arise, both of which are less than ideal.
Oversharing by default
A master spreadsheet created for collaboration with sharing set to “anyone in the organization with this link” can lead to unintended exposure of sensitive information to the entire company.
Additionally, using spreadsheets beyond their intended capacities can lead to errors and inefficiencies, further complicating data management.
Spreadsheet sprawl
To avoid oversharing, individuals often create multiple copies of the same spreadsheet for different purposes, leading to confusion over version control and access permissions.
This decentralized approach not only compromises data integrity but also hampers the ability to track changes and maintain an accurate audit trail.
What concerns CISOs
The inadvertent sharing of sensitive information, as exemplified by Bob forwarding a spreadsheet with confidential data to an external consultant, highlights the risks associated with shadow spreadsheets.
This uncontrolled dissemination of data creates an attack surface that is difficult to monitor and poses a challenge in terms of data governance and compliance.
Fragmented data resulting from shadow spreadsheets also complicates the identification of security breaches and limits the ability to trace unauthorized access and modifications.
Addressing the root cause of shadow spreadsheets requires a balance between security measures and providing users with the tools they need to effectively perform their tasks.
Grist offers teams the flexibility of spreadsheets with the security controls mandated by IT.
With granular permissions, comprehensive audit logs, and open-source deployment options, Grist eliminates the risks associated with shadow spreadsheets without locking users into a specific vendor.
Get Started Free
Why traditional solutions fall short
While training and policies may address certain aspects of data security, the fundamental issue lies in the mismatch between user requirements and the capabilities of existing tools.
Implementing stringent controls or developing custom applications may lead users to resort to less secure methods, exacerbating the problem of shadow spreadsheets.
Recognizing that spreadsheets are a widely used and versatile tool, Grist aims to enhance their security and functionality without compromising user experience.
By securing spreadsheets through granular access controls and relational database integration, Grist provides a solution that meets both user needs and IT security requirements.
Grist: empowering spreadsheets
Grist Labs’ software combines the familiarity of spreadsheets with the security of databases, offering a structured and secure platform for collaborative work.
Founded by a former Google Sheets engineer, Grist is designed to resemble a spreadsheet while leveraging the capabilities of a relational database to ensure data security and integrity.
By enabling role-based access control at a granular level and offering self-hosting options, Grist ensures that sensitive data remains within your organization’s environment.
With features such as single source of truth, audit logging, and integration with existing security systems, Grist provides a comprehensive solution to the challenges posed by shadow spreadsheets.

By embracing the familiar interface of spreadsheets and enhancing their security, Grist offers a practical and efficient solution to the risks associated with shadow spreadsheets.
Experience the evolution of spreadsheets with Grist today.
Sponsored and written by Grist.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS