Security
The ShinyHunters Saga: Uncovering the SSO Account Data Theft Attacks

The Rise of Voice Phishing Attacks Targeting SSO Accounts
In recent times, the ShinyHunters extortion gang has claimed responsibility for a series of voice phishing attacks aimed at single sign-on (SSO) accounts of major companies like Okta, Microsoft, and Google. These attacks have enabled threat actors to infiltrate corporate SaaS platforms and pilfer sensitive company data for extortion purposes.
The modus operandi of these attacks involves threat actors posing as IT support personnel and contacting employees via phone calls. Through social engineering tactics, they deceive employees into divulging their credentials and multi-factor authentication (MFA) codes on fake websites that mimic legitimate company login portals.
Once the attackers gain access to an individual’s SSO account, they can potentially breach other connected enterprise applications and services, posing a significant threat to corporate cybersecurity.
SSO services provided by platforms like Okta, Microsoft Entra, and Google offer companies the convenience of consolidating various third-party applications into a unified authentication process. This streamlined approach allows employees to access cloud services, internal tools, and business platforms with a single set of login credentials.
Typically, SSO dashboards display a comprehensive list of connected services, making a compromised account a gateway to sensitive corporate systems and data.
Popular platforms integrated through SSO include Salesforce, Microsoft 365, Google Workspace, Dropbox, Adobe, SAP, Slack, Zendesk, Atlassian, among others.
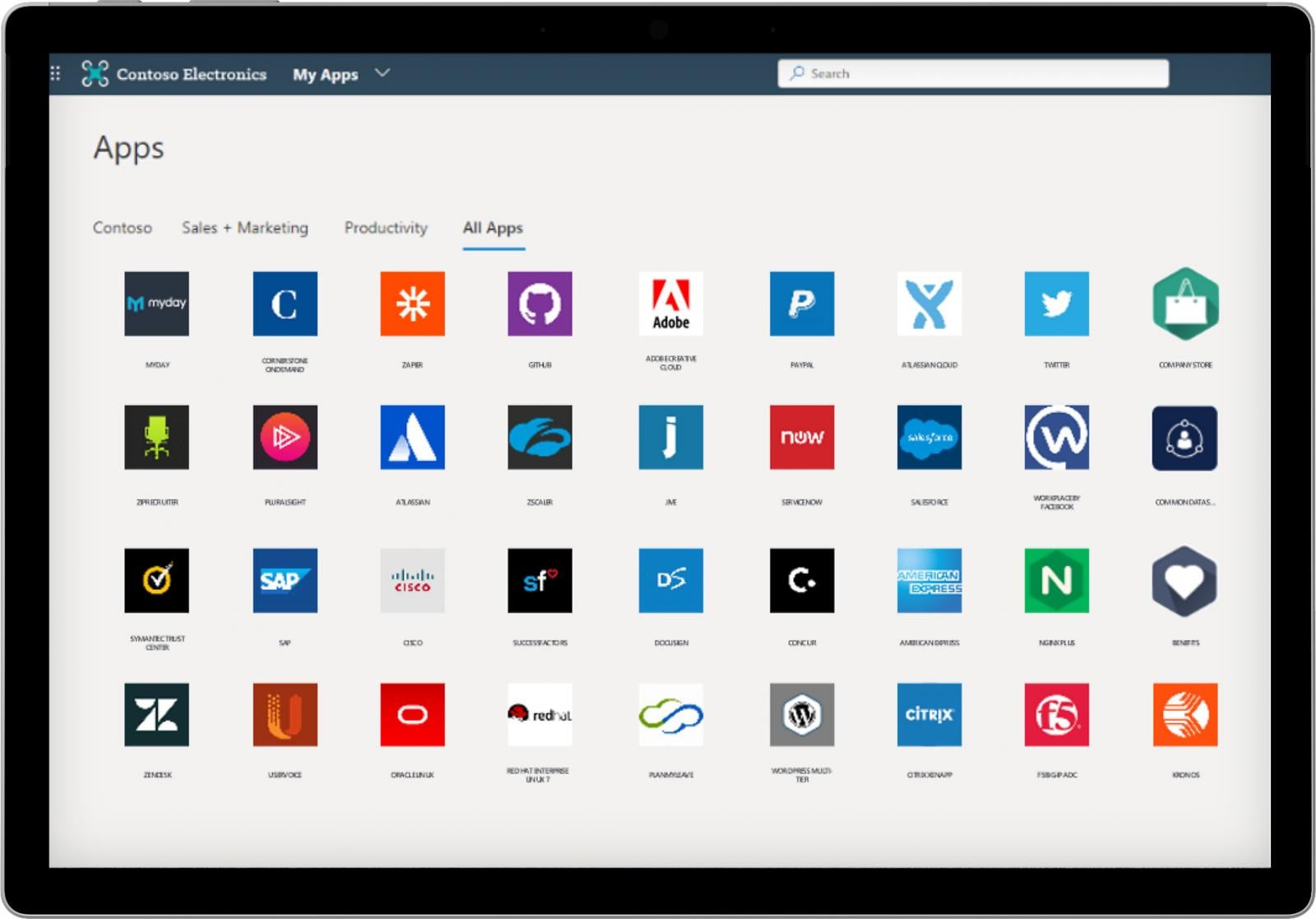
Source: Microsoft
Vishing Attacks: A Gateway to Data Theft
Reports from BleepingComputer have shed light on how threat actors are executing vishing (voice phishing) attacks to steal data. By impersonating IT personnel, attackers engage employees in real-time interactions, coercing them to log into fake websites and complete MFA challenges.
Upon gaining access to a victim’s SSO account, the attackers exploit the connected applications to harvest valuable data, putting organizations at risk of data breaches and extortion attempts.
Several companies targeted in these attacks have received ransom demands attributed to ShinyHunters, underscoring the group’s involvement in these malicious activities.
Okta, a prominent player in the SSO space, recently released a report detailing the phishing kits used in these voice-based attacks, corroborating the information shared by BleepingComputer.
According to Okta’s findings, the phishing kits feature a web-based control panel that allows attackers to manipulate the content displayed on fake websites in real-time while engaging with victims over the phone. This enables threat actors to guide victims through login and MFA processes seamlessly.
In scenarios where stolen credentials trigger MFA prompts on authentic services, attackers can dynamically alter the phishing site to instruct victims on how to bypass additional authentication steps.
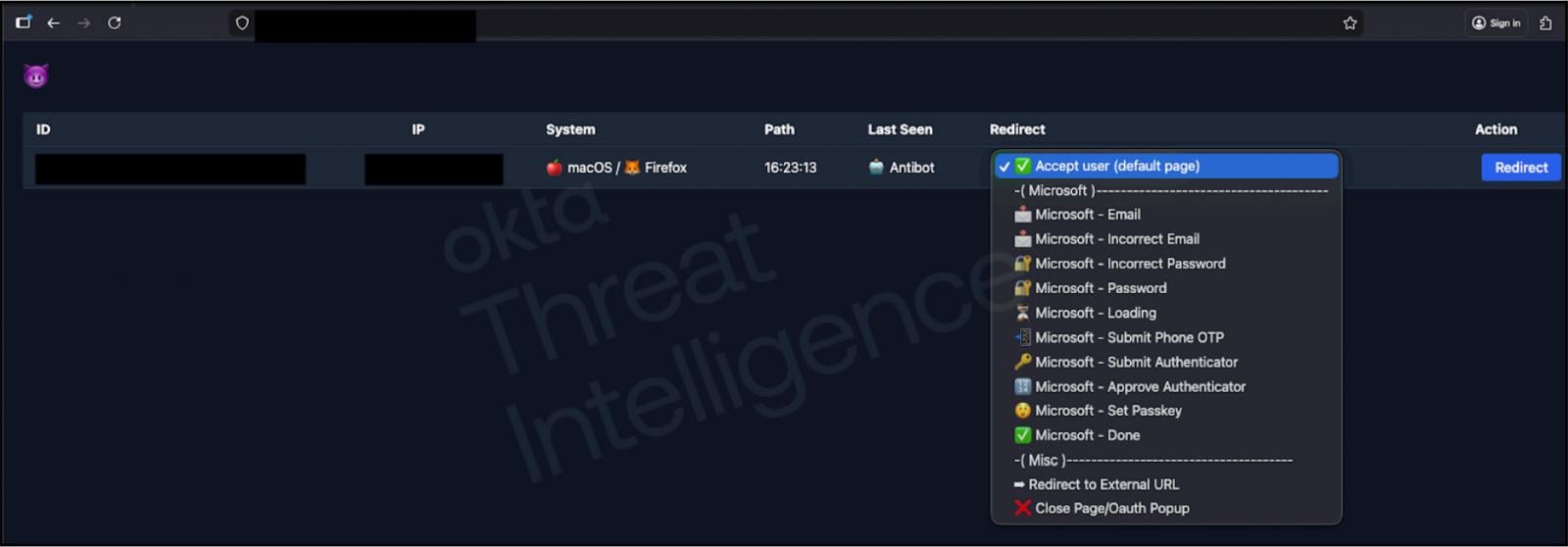
Source: Okta
ShinyHunters: Masters of Social Engineering
Although ShinyHunters initially refrained from commenting on the attacks, the group later acknowledged its involvement in some of the social engineering schemes targeting SSO accounts.
“We confirm we are behind the attacks,” ShinyHunters disclosed to BleepingComputer. “We are unable to share further details at this time, besides the fact that Salesforce remains our primary interest and target, the rest are benefactors.”
While corroborating certain aspects of BleepingComputer’s coverage, ShinyHunters contested the origin of a phishing kit command-and-control server screenshot shared by Okta, asserting that their infrastructure was developed in-house.
The group’s focus extends beyond Okta to encompass Microsoft Entra and Google SSO platforms, highlighting the widespread nature of these threat actors’ activities.
When approached for comments, Microsoft withheld any statement, whereas Google denied any evidence of its products being exploited in the ongoing campaign.
“At this time, we have no indication that Google itself or its products are affected by this campaign,” a Google spokesperson reassured BleepingComputer.
ShinyHunters leverage data obtained from prior breaches, such as the notable Salesforce data theft incidents, to target and engage employees in their social engineering ploys. This data includes personal details like phone numbers, job titles, and names, enhancing the credibility of their deceptive tactics.
Recently, the group revived its Tor data leak site, showcasing breaches at SoundCloud, Betterment, and Crunchbase. Notably, SoundCloud and Betterment had previously acknowledged data breaches, while Crunchbase confirmed a cybersecurity incident involving unauthorized access to certain documents from their corporate network.
“Crunchbase detected a cybersecurity incident where a threat actor exfiltrated certain documents from our corporate network,” a company representative informed BleepingComputer. “No business operations have been disrupted by this incident. We have contained the incident and our systems are secure.”
“Upon detecting the incident we engaged cybersecurity experts and contacted federal law enforcement. We are reviewing the impacted information to determine if any notifications are required consistent with applicable legal requirements.”

With the Model Context Protocol (MCP) gaining traction as the standard for integrating LLMs with tools and data, cybersecurity teams are ramping up efforts to safeguard these new services.
Discover 7 best practices in our free cheat sheet to enhance your security posture.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS
































