The Open Group’s Quiet Revolution In Security Roles
If you have been around this industry long enough to remember the Unix wars, you already know that most “new” ideas in cybersecurity are just old ideas with better branding.
The Open Group is the exception that proves the rule.
“I am John Linford,” the man across from me says, spelling out his name like he has done this a thousand times. He has. “I’m with The Open Group. I am our security portfolio director, so I’m responsible for our security forum, which is more of the cyber security side of things, our open trusted technology Forum, which is the supply chain security side of things, as well as our assured dependability work group, which gets more into combining enterprise architecture with some extra practices for the dependability of that architecture, and now mixing in security practices as part of those processes.”
If that sounds like a lot, that is because it is. But beneath the forums and work groups is a simple idea: security needs standardization that people can actually use in the real world, not just in PowerPoint decks.
And that is where The Open Group quietly does some of the most foundational work in the industry.
From Unix Wars To Zero Trust Reality
“The Open Group” has the sort of generic name that sounds like it was generated by a committee, which is fitting, because in a sense it was.
“The open group [is] a global standards organization,” Linford explains. “We are open as the name implies, coming originally out of the Unix wars. So still maintain all of the UNIX Specification.”
Long before Zero Trust became the buzzword that launched a thousand vendor booths, The Open Group was in the business of taming chaos. Back then, the chaos was competing Unix variants. Today, it is the explosion of security roles, responsibilities and expectations inside every modern organization.
The organization itself predates its own name.

The current brand “came out of the X open Foundation, and if I remember correctly, the open software foundation, it was well before I joined the open group,” Linford recalls. “I’ve only ever known The Open Group as The Open Group, and I’ve been in the industry for 22 years now, so that’s all I have ever known it by,” he adds, noting the naming “came at some point in the mid 90s.”
What has not changed is the focus: bring order to fragmented ecosystems through open, consensus driven standards.
“We’ve got some of our publications going back into the early 90s,” Linford notes, “and really looking at providing a consistent way for organizations across private and public sectors to have consistent security processes, rather than needing to do everything unique or specific to their context, but being able to tailor to their own needs.”
That last bit is key for CISOs. Every environment is unique, but no one has time to reinvent the wheel for every role, responsibility or process. The tension is between consistency and flexibility. The Open Group lives in that tension.
Security Is Everyone’s Job. Now What?
There is a cliché you have probably heard in every board meeting since about 2015: “Security is everyone’s responsibility.”
The problem is that very few organizations have done the hard work of turning that slogan into specific, accountable tasks at the individual role level.
Linford’s team has been trying to fix exactly that.
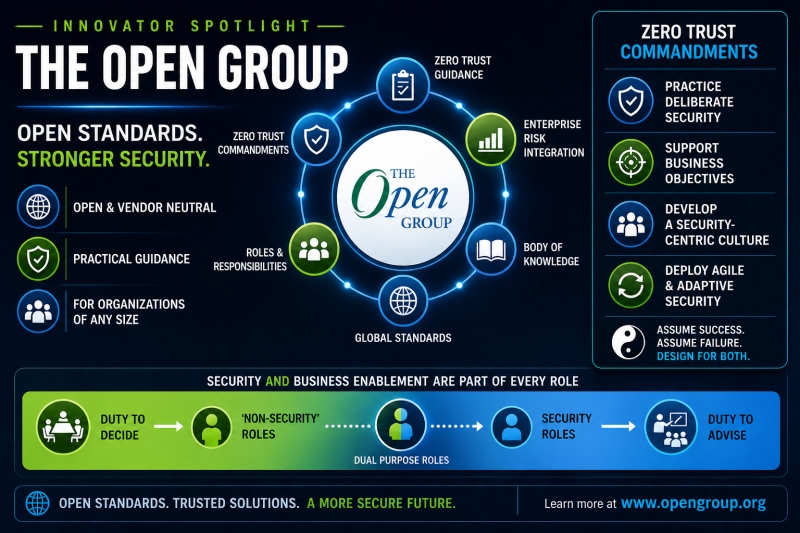
“The most recent, or one of the most recent publications from the security forum is our security roles and glossary standard series,” he explains. “We’ve noticed that security is part of everyone’s job. We’ve known this for a while. Zero Trust has really solidified that fact and is gaining more adoption.”
Then he gets to the point that every CISO will recognize.
“But it’s not just the security specific roles that have a security task. So what this series does is look at defining, what are your security specific roles? What are roles that have really little or anything to do with security, and then what are kind of those hybrid roles that do a little bit of both sides and outlining responsibilities and accountabilities for each of those roles in that security context, and that goes down as well to what happens if you don’t do your security tasks.”
In other words, this is not a fluffy “culture of security” poster for the hallway. It is a structured way to map who does what, where security shows up in their job description and what the implications are when it does not.
If you have ever been on a post incident call where legal, HR, engineering and security argue about who “owned” multi factor configuration or vendor review, you already know why this matters.
Designing For the Very Small and the Very Large
One of the more quietly impressive aspects of The Open Group’s work is that it is designed to scale both down and up. That is not something you can say about many frameworks that were clearly written by and for large enterprises.
“Making a little bit easier for organizations of any number of sizes to figure out what kind of employees do we need? What do we need them doing?” Linford says of the security roles and glossary work.
He does not stop there. He explicitly calls out both ends of the spectrum:
- “If you’re a small organization, what are the different types of tasks that the one person is going to be doing to consolidate some of these roles?”
- “Or if you’re a really big organization, how do you sort of divvy those up as efficiently as possible?”
This is the reality of security leadership in 2026. One CISO is trying to keep a three-person team from burning out while also meeting customer demands for SOC 2 and ISO alignment. Another individual is attempting to rationalize a hundred-person security organization that has grown through acquisitions and appears to be a patchwork quilt.
Both individuals require the same thing: a clear vocabulary for roles and responsibilities, and a method to map tasks to job functions without becoming overwhelmed by complexity.
At this stage in the discussion, the obvious question arises: Is The Open Group essentially creating something akin to ITIL for security roles?
The interviewer poses the question, wondering if this is an effort to replicate the ITIL format for tasking, assignments, and ownership labels. Linford responds diplomatically, stating that while there is some similarity and crossover, it is not a direct recreation. He also acknowledges that this work is not done in isolation, noting the overlap with what NIST and CC are doing with the NICE framework. The aim of The Open Group’s work is to help individual employees understand their tasks and accountabilities.
The distinction lies in the focus on the individual employee knowing their security tasks and accountabilities, rather than just organizational charts and HR plans. The series is about practical application rather than theoretical frameworks.
The benefit for CISOs is clear: less time spent resolving definitional disagreements and more time devoted to enhancing controls and results.
The Open Group’s security roles and glossary standard series is worthy of attention from security leaders for several practical reasons, including its specificity in defining security responsibilities for various roles, its applicability to organizations of all sizes, and its alignment with existing frameworks like NIST guidance.
A shared, standards-based model for roles and responsibilities provides credibility when explaining to executives why certain tasks belong to specific departments. It shifts the conversation from being solely the responsibility of the security team to aligning with an established external model.
For security leaders, it is recommended to evaluate how The Open Group’s work can support existing efforts by examining the mapping of security responsibilities, ensuring new hires understand their security tasks, and establishing a clear reference for ownership in case of incidents.
In practical terms, this may involve collaborating with HR and security operations leaders to align job descriptions with the glossary and roles guidance, using the organizational leadership and governance sub-documents as a reference for decision-making, and evaluating the alignment of SOC team responsibilities with the standard roles.
Ultimately, the goal is to move beyond the vague notion that security is everyone’s job and establish a structured, scalable framework that supports the organization’s security efforts. The Open Group’s experience in standardization can be a valuable resource in achieving this goal.
The Open Group: Leading the Way in Security Roles and Language
At the forefront of the mission to reduce chaos, increase interoperability, and provide practical tools for security practitioners is The Open Group. Their work on security roles and language represents a modern approach to addressing these critical issues.
In a time where every vendor claims to be revolutionizing something, The Open Group stands out by consistently releasing standards that assist professionals in their day-to-day tasks without fanfare. Their focus is on enabling organizations to progress smoothly in their security efforts.
If your goal is to enhance your security program in a manner that is clear to your team, sustainable for your organization, and justifiable to your stakeholders, look no further than The Open Group’s work on security roles and glossary. Incorporating their insights into your strategies can streamline operations and improve overall effectiveness.
With so many aspects of security to manage, there is no need to reinvent the wheel when it comes to defining roles and responsibilities. The Open Group provides a solid model that can guide your organization towards clarity and efficiency in security practices.
Author’s Insight
Having engaged in a discussion with John Linford, Security Portfolio Director at The Open Group, following the 2026 RSAC Conference in San Francisco, the author delved into the organization’s approach to navigating the complexities of security duties within modern enterprises. From governance to operational tasks, The Open Group’s work sheds light on the evolving landscape of security responsibilities.
For further details, please visit www.opengroup.org.
Pete Green: A Seasoned Cybersecurity Expert
Meet Pete Green, the CISO/CTO of Anvil Works, a ProCloud SaaS company, and co-author of “The vCISO Playbook: How Virtual CISOs Deliver Enterprise-Grade Cybersecurity to Small and Medium Businesses (SMBs)”. With over 25 years of experience in IT and cybersecurity, Pete brings a wealth of knowledge and expertise to the field.
Throughout his extensive career, Pete has held various technical and leadership positions, including LAN/WLAN Engineer, Threat Analyst, Security Project Manager, Security Architect, Cloud Security Architect, Principal Security Consultant, Director of IT, CTO, CEO, Virtual CISO, and CISO.