Security
Unveiling the Untapped Potential of Google API Keys: The Gemini AI Data Breach

Google API Keys Expose Gemini AI Data: A Security Concern
Google API keys designed for services like Maps have inadvertently exposed private data to potential attackers through the Gemini AI assistant. This revelation comes as a result of nearly 3,000 vulnerable keys discovered by researchers across various sectors, including Google itself.
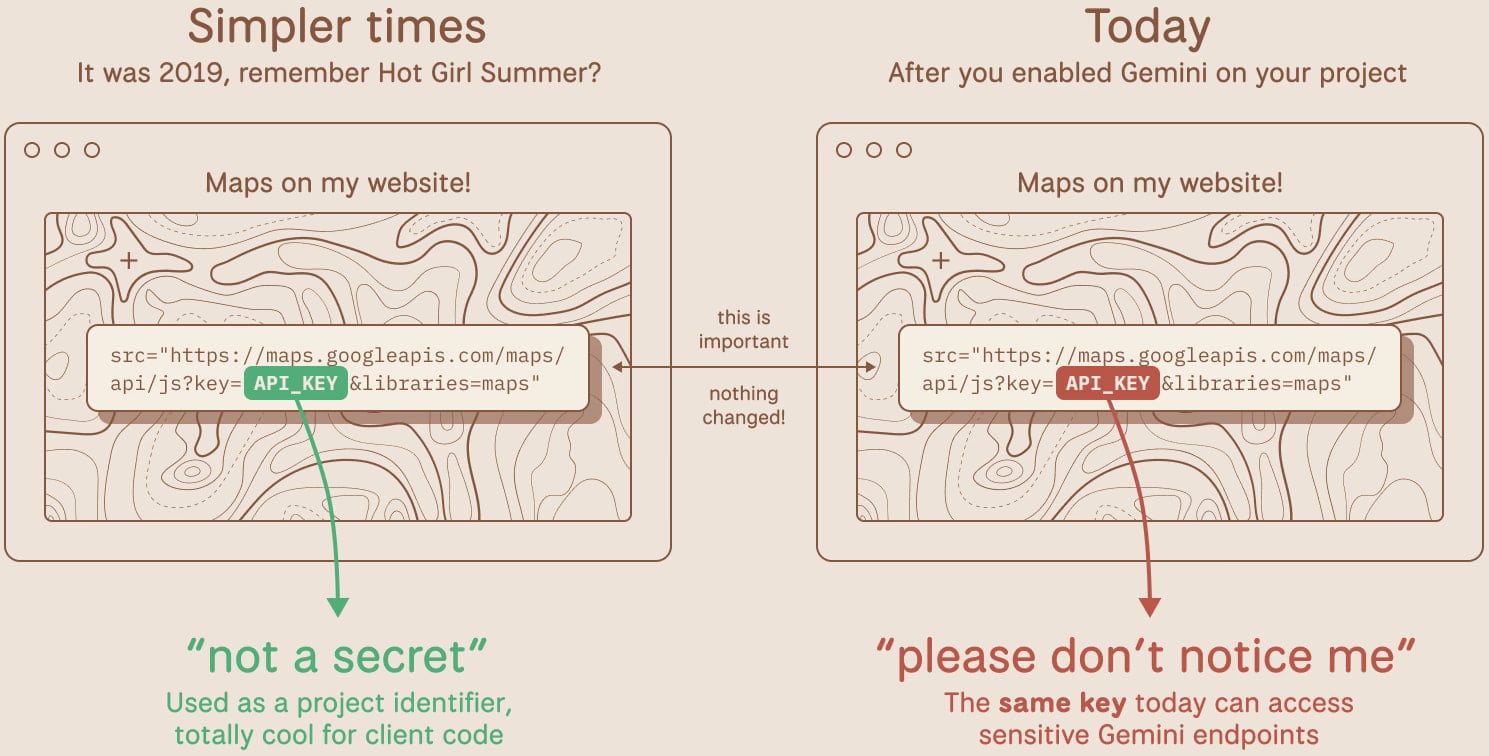
The issue arose with the introduction of Google’s Gemini assistant, which caused developers to enable the LLM API in their projects. Prior to this, Google Cloud API keys were not considered sensitive and could be freely exposed online without consequences.
API keys play a crucial role in extending functionality within projects, such as embedding Maps, YouTube videos, usage tracking, and Firebase services. However, the integration of Gemini transformed Google Cloud API keys into authentication credentials for the AI assistant.
TruffleSecurity researchers identified the vulnerability, warning that malicious actors could exploit exposed API keys to access private data accessible through the Gemini API service. This unauthorized access could lead to significant financial losses, with attackers potentially incurring substantial charges through malicious API calls.
According to TruffleSecurity, these exposed API keys have remained unnoticed in public JavaScript code for years, increasing their risk profile significantly without adequate mitigation measures.
TruffleSecurity’s analysis of the November 2025 Common Crawl dataset revealed over 2,800 live Google API keys publicly exposed in code snippets. These keys were utilized by major financial institutions, security firms, and recruiting agencies. Upon identifying the issue, TruffleSecurity promptly reported it to Google, providing samples from the affected infrastructure.
One notable case involved an API key acting as an identifier since February 2023, embedded within the page source of a public-facing Google product website.
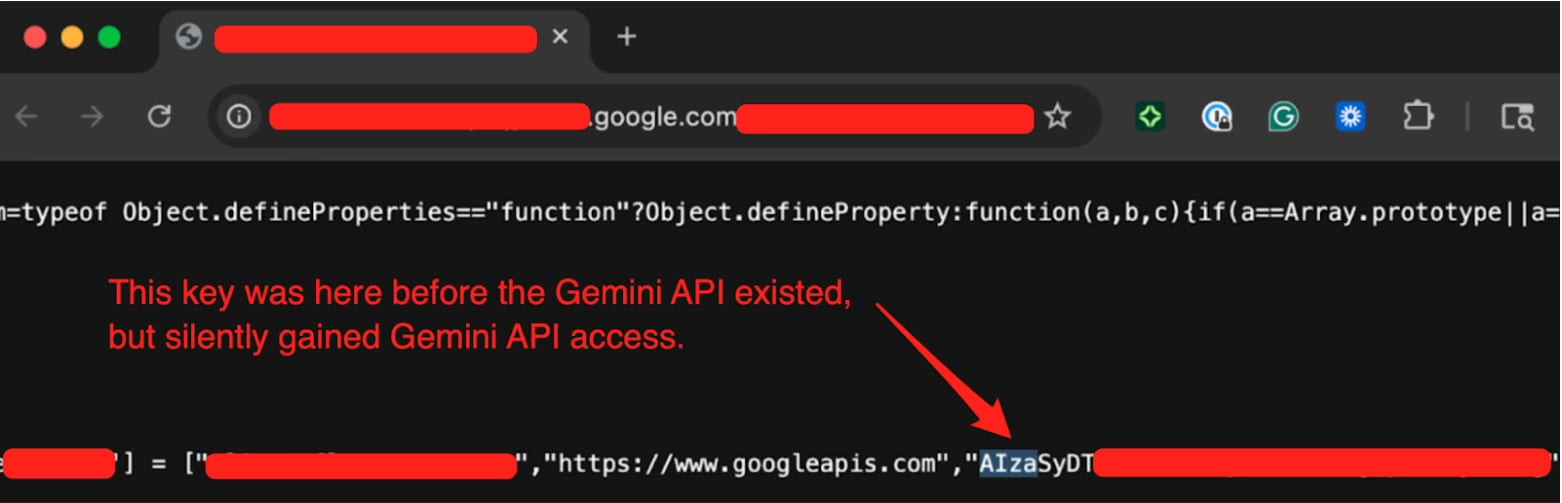
Source: TruffleSecurity
TruffleSecurity validated the vulnerability by accessing the Gemini API’s /models endpoint through the exposed key. Despite reporting the issue to Google on November 21, 2025, Google only acknowledged the flaw as “single-service privilege escalation” on January 13, 2026.
In response to the findings, Google assured BleepingComputer of proactive measures to detect and block leaked API keys attempting to access the Gemini API. This includes defaulting new AI Studio keys to Gemini-only scope, blocking leaked keys, and issuing notifications for potential leaks.
Developers are advised to review their projects for Gemini enablement, audit all API keys for exposure, and promptly rotate any compromised keys. Additionally, leveraging tools like TruffleHog can aid in detecting live, exposed keys within code repositories.

Modern IT infrastructure outpaces manual workflows, causing hidden delays and reliability issues. Discover how automated responses and intelligent workflows can optimize your operations in the new Tines guide.
-

 Facebook8 months ago
Facebook8 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS