Security
Uncovering the Cyber Threat: A Year of Exploited Zero-Days

In 2025, Google’s Threat Intelligence Group (GTIG) monitored and recorded 90 instances of zero-day vulnerabilities being actively exploited, with nearly half of them targeting enterprise software and appliances.
This figure represents a 15% increase from the previous year, where 78 zero-day exploits were identified, but is lower than the peak of 100 zero-day vulnerabilities tracked in 2023.
Zero-day vulnerabilities are critical security flaws in software products that attackers leverage before the vendor is aware of them and can release a patch. These vulnerabilities are highly sought after by threat actors as they often facilitate initial access, remote code execution, or privilege escalation.
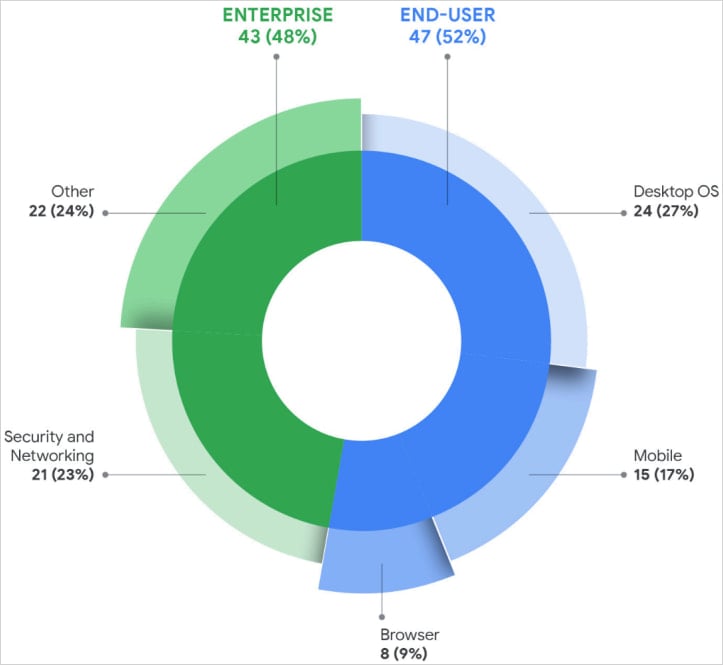
A recent report from GTIG highlighted that out of the 90 zero-day exploits in 2025, 47 targeted end-user platforms, while 43 focused on enterprise products.
The types of vulnerabilities exploited include remote code execution, privilege escalation, injection and deserialization flaws, authorization bypasses, and memory corruption issues such as use-after-free bugs. Google’s data indicates that memory safety concerns constituted 35% of all zero-day exploits in the past year.
Among enterprise systems, security appliances, networking infrastructure, VPNs, and virtualization platforms were the most targeted due to their provision of privileged network access and the lack of EDR monitoring.
Operating systems experienced the highest number of exploits, with 24 zero-day vulnerabilities exploited in desktop OSs and 15 in mobile platforms in 2025.
Interestingly, the number of zero-day exploits in web browsers dropped significantly to eight, possibly attributed to enhanced security measures in this software category or advanced evasion tactics employed by threat actors.
Google’s analysts speculate that this decline could be a result of increased security measures in web browsers or a shift towards more sophisticated evasion techniques by threat actors.
Source: Google
According to GTIG researchers, Microsoft was the most targeted vendor with 25 zero-day exploits in 2025, followed by Google with 11, Apple with eight, and Cisco and Fortinet with four each. Additionally, Ivanti and VMware each experienced three zero-day exploits.
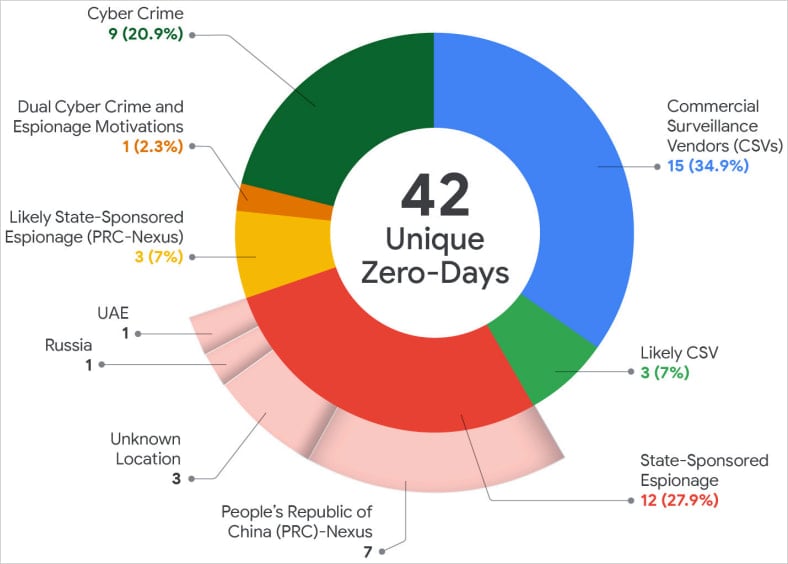
For the first time, commercial spyware vendors surpassed state-sponsored espionage groups in exploiting undocumented vulnerabilities, indicating a shift in the threat landscape towards commercial entities.
GTIG’s report highlighted the trend of increasing zero-day exploitation by commercial spyware vendors and their clients, indicating a significant shift in the threat landscape.
Source: Google
Google’s researchers noted that China-linked espionage groups remained the most active state-sponsored actors, exploiting 10 zero-day vulnerabilities in 2025. These attacks primarily targeted edge devices, security appliances, and networking equipment to establish persistent access.
Another significant trend observed was the rise in zero-day exploitation by financially motivated threat actors, such as ransomware groups, accounting for nine of the vulnerabilities exploited.
GTIG anticipates that the use of AI tools will streamline vulnerability discovery and exploit development, resulting in continued high levels of zero-day exploits in 2026.
The report highlighted the Brickstorm campaign as an example of threat actors shifting focus from source code theft to identifying vulnerabilities in upcoming software products.
To effectively identify and mitigate zero-day exploits, Google recommends reducing attack surfaces, minimizing privilege exposure, implementing continuous system monitoring for anomalies, and maintaining rapid patching and incident response protocols.

Malware tactics are evolving. The Red Report 2026 exposes how new threats leverage mathematics to evade detection and operate stealthily.
Gain insights from analyzing 1.1 million malicious samples to uncover the top 10 techniques and assess the effectiveness of your security measures.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS































