Security
Data Breach Alert: Infinite Campus Investigates Potential Security Breach After Claims of Data Theft

Infinite Campus Faces Data Breach After Extortion Attempt
In a recent development, Infinite Campus, a prominent K-12 student information system provider, is alerting its customers about a data breach that occurred following an extortion attempt by a threat actor.
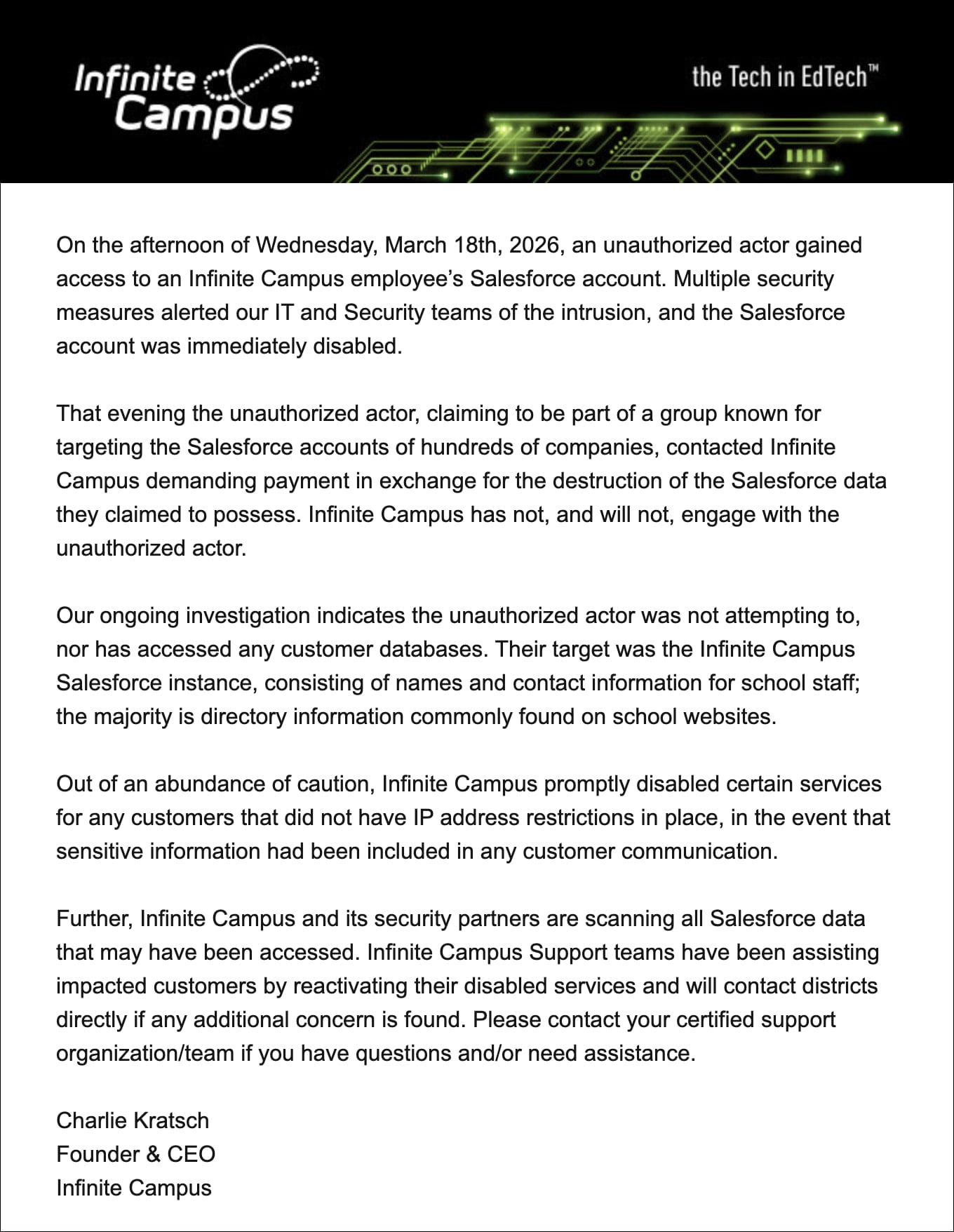
The breach notification sent to customers disclosed that hackers gained unauthorized access to an employee’s Salesforce account, resulting in the exposure of primarily publicly available information.
While the company has not issued an official statement, reports of the incident surfaced on various public platforms through concerned customers.
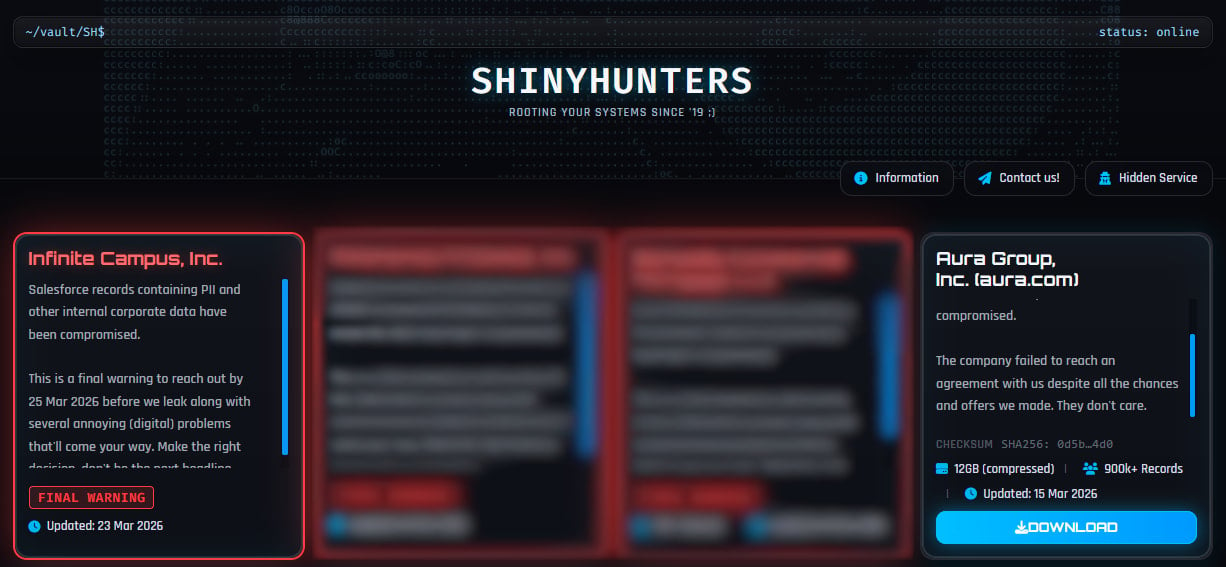
This notification comes in the wake of a claim by the data extortion group ShinyHunters, who asserted responsibility for the attack and issued a “final warning” on their dark web platform, threatening to release all data allegedly obtained from Infinite Campus.
The hackers set a deadline of March 25 for the company to engage in negotiations for a ransom to prevent the data leak. However, Infinite Campus made it clear that they would not comply with the attacker’s demands.
According to ShinyHunters, they have retrieved Salesforce records containing personally identifiable information (PII) and various internal corporate data.
Source: BleepingComputer
Infinite Campus, a U.S.-based education technology (EdTech) company known for providing a student information system (SIS) to over 3,200 school districts across the United States, currently manages data for 11 million students in 46 states.
While not explicitly naming ShinyHunters as the threat actor, Infinite Campus described the intruder as “part of a group known for targeting the Salesforce accounts of hundreds of companies.”
The data extortion group has been actively targeting Salesforce customers for the past year, infiltrating numerous companies and claiming to have stolen over 1.5 billion records in previous hacks like the Salesloft Drift and Salesforce Aura campaigns.
Following their investigation, Infinite Campus confirmed that no customer databases were compromised. The exposed data mainly includes names and contact details of school staff, information that is typically available in the public domain.
“Their target was the Infinite Campus Salesforce instance, consisting of names and contact information for school staff; the majority is directory information commonly found on school websites,” the company explained.
Source: Reddit
As a response to the incident, Infinite Campus has temporarily disabled certain customer-facing services for users without IP address restrictions to minimize the risk of exposing sensitive data.
Additionally, the company is conducting a thorough scan of all potentially compromised Salesforce data and reaching out to districts that may have been affected to provide necessary guidance.
While BleepingComputer sought clarification from Infinite Campus regarding the impact on school districts, they are yet to receive a response.
This incident bears resemblance to the December 2024 PowerSchool hack in terms of the targeted platform. However, the scale of impact differs significantly, with the PowerSchool breach exposing sensitive information of 62 million students.
The perpetrator behind the PowerSchool attack, a 19-year-old college student from Massachusetts, received a four-year prison sentence after pleading guilty in May 2025.

Stay informed about evolving malware threats. Explore the Red Report 2026 for insights on how new threats utilize advanced techniques to evade detection.
Access our comprehensive analysis of 1.1 million malicious samples to uncover top strategies and evaluate the effectiveness of your security measures.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS






























