Security
Ransomware Revolution: The Rise of Multi-Extortion Attacks

Ransomware’s Impact on Various Sectors
During February 2026, the University of Mississippi Medical Center (UMMC) encountered a ransomware attack that disrupted its Epic electronic health record system, affecting multiple clinics and telehealth sites. This led to the cancellation of crucial medical appointments and surgeries, emphasizing the severe consequences of cyber threats on patient care.
UMMC’s incident is not an anomaly. Recent data reveals that 93% of healthcare organizations in the U.S. experienced cyberattacks in 2025, with 72% reporting disruptions to patient care as a result.
Other industries, such as manufacturing and finance, are also vulnerable. In the same month, BridgePay, a payment processing network, faced a ransomware attack that completely halted its payment processing services. The prevalence of ransomware attacks increased by 49% in 2025, with 1,174 confirmed incidents across various sectors.
With hospitals unable to provide treatments, financial institutions unable to process transactions, and manufacturing facilities forced to shut down, ransomware has proven to be a significant business risk with tangible operational impacts.
The Emergence of Double Extortion Ransomware
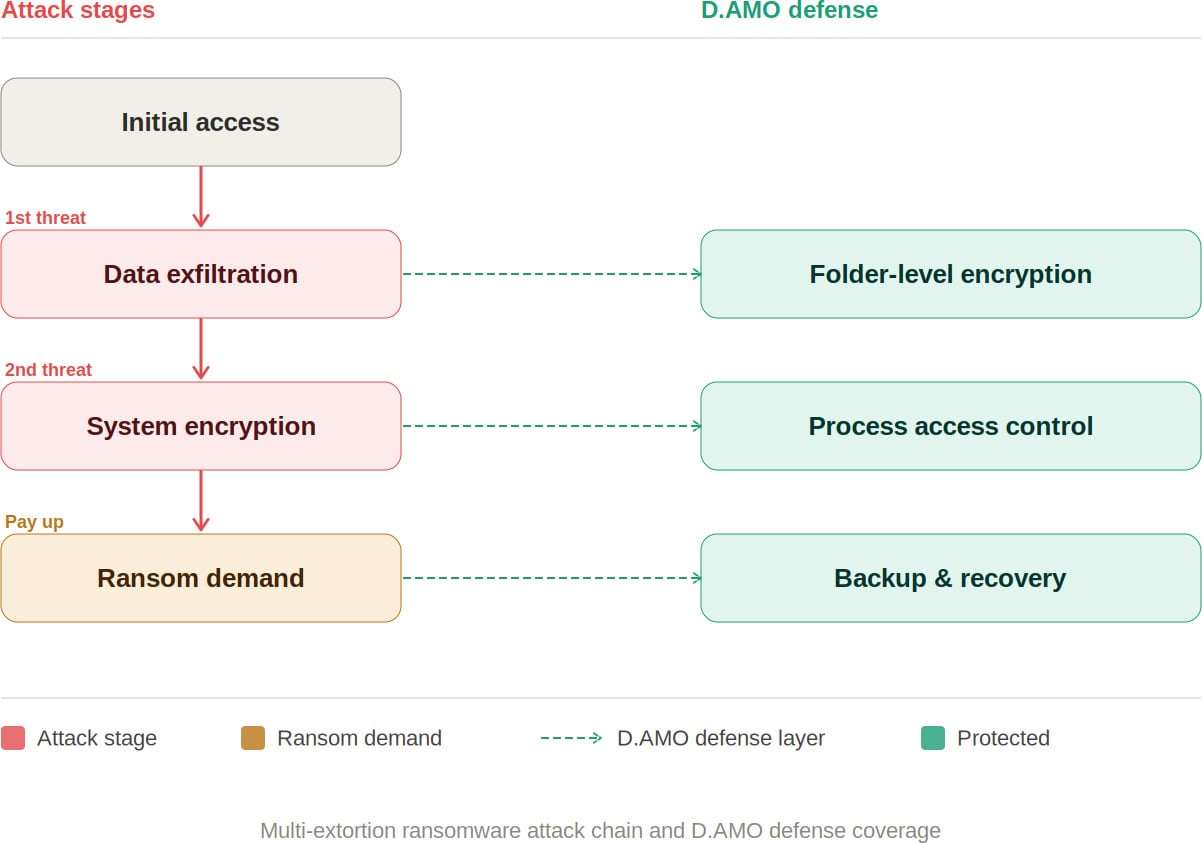
Initially, ransomware focused on encrypting files and demanding payment for decryption. However, organizations began countering this by restoring from backups rather than paying the ransom, prompting threat actors to adopt a more lucrative strategy known as double extortion.
In a double extortion attack, cybercriminals first steal sensitive data before encrypting the system. This places victims in a dilemma: pay the ransom for decryption or risk having the stolen data publicly exposed.
Traditional backups are ineffective against this approach since attackers already have the data. Refusing to pay the ransom may result in the public release of sensitive information, leading to significant financial losses and regulatory penalties for organizations.
The threat landscape has evolved further, with the introduction of triple extortion, where attackers directly contact an organization’s customers or partners to exert additional pressure.
As of 2025, there are 124 active ransomware groups, 73 of which are newly identified.
The advancement of AI-driven tools has democratized cybercrime, making ransomware capabilities more accessible to less sophisticated actors.
D.AMO ensures stolen data remains unintelligible.
Discover how D.AMO safeguards against every facet of a ransomware attack.
Learn More
Building a Defense Strategy Against Multi-Extortion Threats
The prevalence of multi-extortion ransomware necessitates a shift in traditional defense strategies. Relying solely on perimeter-based prevention is no longer sufficient.
Organizations require a robust security posture that can prevent data exploitation post-breach, making exfiltrated data unreadable, blocking ransomware from accessing files, and enabling swift recovery in the event of an attack.
D.AMO: Safeguarding Against Ransomware Attacks
D.AMO, developed by Penta Security, is a data protection platform based on encryption that addresses every stage of a multi-extortion ransomware attack. It offers comprehensive encryption, access control, and backup recovery for on-premises and cloud environments.
By leveraging file encryption and access control mechanisms, D.AMO secures critical data stored on servers and PCs, protecting sensitive information from malicious threats through robust access restrictions. The key features of D.AMO include:
Folder-Level File Encryption
D.AMO KE encrypts all files within designated folders at the OS level. With kernel-level encryption technology, it can quickly and securely encrypt existing systems without disrupting user operations.
Encryption policies are enforced at the folder level, ensuring consistent data protection with minimal overhead. Importantly, even if data is stolen, the encryption keeps it secure, mitigating the data exposure risk associated with double extortion.
Access Control
D.AMO KE enforces strict access controls for processes and OS users, permitting only authorized access. This prevents ransomware and other malicious software from tampering with encrypted folders, thwarting unauthorized file access.
All blocked activities are logged in an audit trail and can be centrally reviewed through the D.AMO Control Center.
Backup and Recovery
In the event of a successful attack, organizations can swiftly resume operations using an independent recovery system. With D.AMO, the ability to restore from backups reduces reliance on negotiating decryption keys with threat actors.
Given the prevalence of multi-extortion tactics, securing targeted data has become a critical objective. Organizations must render exfiltrated data unreadable, prevent ransomware from accessing files, and recover promptly from incidents.
D.AMO offers a comprehensive defense against ransomware attacks, integrating encryption, access control, and backup recovery into a unified security platform.
Keen to delve deeper? Download the D.AMO Data Sheet.
Presented and sponsored by Penta Security.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS