A recent report by Check Point has uncovered that The Gentlemen ransomware-as-a-service (RaaS) group is utilizing a proxy malware known as SystemBC to infiltrate systems. This discovery has led to the identification of a botnet comprising over 1,570 victims, all linked to the SystemBC command-and-control (C2) server.
SystemBC operates by creating SOCKS5 network tunnels within the victim’s environment and establishes a connection with its C2 server using a custom RC4-encrypted protocol. It also has the capability to download and execute additional malware, either by writing payloads to disk or injecting them directly into memory.
Since its emergence in July 2025, The Gentlemen has become a prominent ransomware group, targeting a wide range of systems including Windows, Linux, NAS, and BSD. The group employs sophisticated techniques such as a double-extortion model and utilizes legitimate drivers and custom malicious tools to evade detection.
While the initial access method used by the threat actors remains unclear, evidence suggests that they exploit internet-facing services or compromised credentials to gain a foothold. The attacks involve various stages including discovery, lateral movement, payload staging, defense evasion, and ransomware deployment, with the notable use of Group Policy Objects (GPOs) to compromise entire domains.
Security vendor Trend Micro highlighted The Gentlemen’s advanced tactics, noting their ability to tailor attacks against specific security vendors and engage in thorough reconnaissance and tool modification throughout their operations.
In a recent development, Check Point discovered that an affiliate of The Gentlemen RaaS deployed SystemBC on a compromised host, resulting in hundreds of victims worldwide, including in the U.S., the U.K., Germany, Australia, and Romania.
While SystemBC has been previously used in ransomware operations, the exact relationship between the malware and The Gentlemen group is still unclear. It remains uncertain whether SystemBC is a standard component of the group’s attack playbook or if it’s deployed by specific affiliates for data exfiltration and remote access.
The ransomware deployed by The Gentlemen attempts to disable Windows Defender on remote hosts by executing a PowerShell script that disables real-time monitoring, adds exclusions, shuts down the firewall, and more before initiating the ransomware binary. Additionally, an ESXi variant of the ransomware is capable of shutting down virtual machines and maintaining persistence through crontab.
Eli Smadja from Check Point Research emphasized the scale of The Gentlemen operation, revealing that over 1,570 corporate networks had been compromised by the group. This indicates that the true extent of the operation is larger than publicly known and continues to grow.

In a separate development, Rapid7 shed light on a new ransomware family called Kyber, which emerged in September 2025. Kyber targets Windows and VMware ESXi infrastructures using encryptors developed in Rust and C++, respectively. The ESXi variant is tailored for VMware environments, while the Windows variant includes features for targeting Hyper-V.
While Kyber ransomware may not be complex in its code, it is highly effective at causing damage. This reflects a trend towards specialized, destructive ransomware rather than sophisticated attacks.
Data compiled by ZeroFox reveals a significant increase in ransomware and digital extortion incidents, with over 2,000 incidents observed in Q1 2026, including a surge in March alone. The most active groups during this period were Qilin, Akira, The Gentlemen, INC Ransom, and Cl0p.
Interestingly, The Gentlemen’s attacks targeted a substantial number of North America-based victims, defying regional targeting trends observed in other ransomware collectives. This highlights the group’s global reach and impact.
Ransomware Attacks: Trends and Evolution
The cybersecurity landscape continues to evolve, with ransomware operations becoming more organized and business-driven criminal enterprises. Ransomware attacks targeting the automotive industry have doubled in 2025, comprising 44% of cyber incidents in the sector.
Noteworthy trends include attempts to bypass security tools, the use of BYOVD attack techniques, blurred lines between nation-state and criminal campaigns, and a focus on small and mid-sized organizations and operational technology environments.
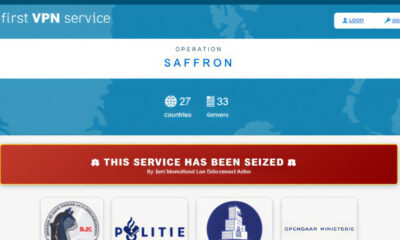
Ransomware has transformed into an industrialized ecosystem built on specialization and shared infrastructure. Law enforcement actions have disrupted major operations, leading to fragmentation, rebranding, and increased competition in the ransomware landscape.
Ransomware attacks are becoming faster and more targeted, with attackers staging attacks during off-hours to outpace defenders. For example, Akira ransomware attacks demonstrate rapid escalation, encrypting systems within an hour in some cases without detection.
Halcyon warns that Akira ransomware poses a significant threat due to its speed, operational discipline, and investment in decryption infrastructure. Defenders must treat Akira as a persistent adversary capable of exploiting vulnerabilities to achieve its goals.