Security
Breach Alert: Massive Leak of Credentials and Auth Keys from Over 10,000 Docker Hub Images

Over 10,000 Docker Hub Images Expose Critical Data
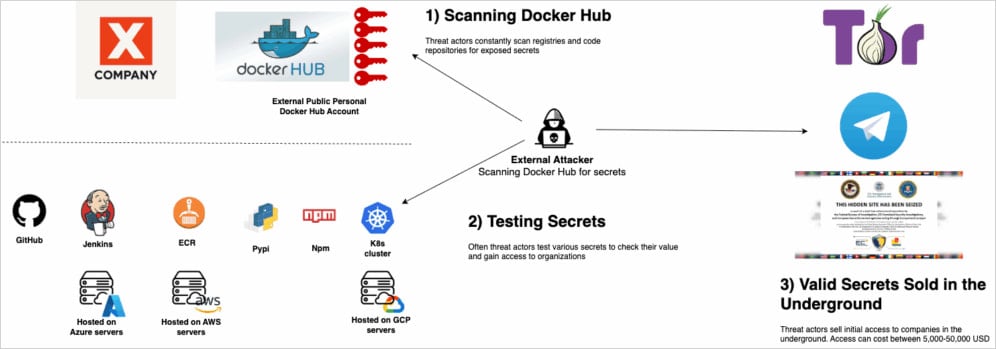
Recently, it was discovered that more than 10,000 Docker Hub container images have been found to expose sensitive data that should be kept secure. This includes live credentials to production systems, CI/CD databases, and LLM model keys.
Among the affected entities are over 100 organizations, including a Fortune 500 company and a major national bank.
Docker Hub serves as the largest container registry where developers can upload, host, share, and distribute Docker images that contain everything needed to run an application.
While developers often use Docker images to streamline the software development and deployment process, carelessness in creating these images can lead to the exposure of secrets that can remain valid for extended periods.
Following a scan of container images uploaded to Docker Hub in November, security researchers at Flare found that a staggering 10,456 of them exposed one or more keys.
Notably, the most common exposed secrets were access tokens for various AI models, with researchers identifying around 4,000 such keys.
Further analysis revealed that 42% of the scanned images exposed at least five sensitive values, posing critical risks as they could potentially grant full access to cloud environments, Git repositories, CI/CD systems, payment integrations, and other essential infrastructure components.
Source: Flare
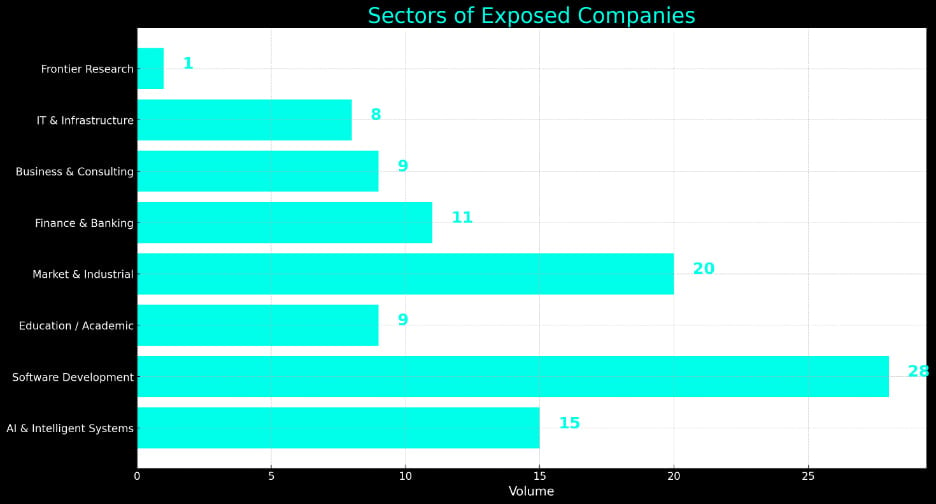
By analyzing 205 namespaces, researchers were able to identify a total of 101 companies, predominantly small and medium-sized businesses, with a few large enterprises also present in the dataset.
The majority of organizations with exposed secrets were found in the software development sector, followed by entities in market and industrial, as well as AI and intelligent systems.
Furthermore, more than 10 finance and banking companies had their sensitive data exposed due to these vulnerabilities.
Source: Flare
One common error observed by researchers was the use of .ENV files to store sensitive information such as database credentials, cloud access keys, and tokens. Additionally, hardcoded API tokens for AI services were found in various application files and configurations.
Some of the exposed data was present in the manifest of Docker images, which provides details about the image.
Many of these leaks were attributed to ‘shadow IT’ accounts on Docker Hub, which operate outside of corporate monitoring mechanisms, such as those used for personal accounts or contractors.
Flare noted that approximately 25% of developers who accidentally exposed secrets on Docker Hub were quick to rectify the issue by removing the leaked secrets within 48 hours. However, in 75% of cases, the exposed keys were not revoked, leaving them vulnerable to potential misuse in future attacks.
Source: Flare
Flare recommends that developers refrain from storing secrets in container images, avoid using static, long-lived credentials, and centralize secrets management using dedicated vaults or secrets managers.
Organizations are advised to implement active scanning throughout the software development lifecycle, promptly revoke exposed secrets, and invalidate old sessions to mitigate risks.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS