Security
AI-Powered Android Malware: Clicking on Hidden Browser Ads

New Android Malware Utilizes AI to Click on Hidden Browser Ads
A novel type of Android click-fraud trojans is now making waves in the cybersecurity realm. These trojans employ TensorFlow machine learning models to automatically detect and engage with specific advertisement elements.
This innovative approach relies on visual analysis powered by machine learning, straying away from traditional JavaScript click routines. It bypasses script-based DOM-level interaction commonly used by classic click-fraud trojans.
The threat actor behind this scheme is leveraging TensorFlow.js, an open-source library developed by Google. This library enables the training and deployment of machine learning models in JavaScript, allowing for AI models to run in browsers or servers using Node.js.

Research conducted by mobile security company Dr.Web has unveiled that this new family of Android trojans is being distributed through GetApps, the official app store for Xiaomi devices.
It has been discovered that the malware can operate in a mode referred to as ‘phantom’, where it utilizes a hidden WebView-based embedded browser to load a target page for click-fraud. A JavaScript file is also loaded, with the script automating actions on the ads displayed on the loaded site.
Upon fetching the trained model from a remote server, the hidden browser is positioned on a virtual screen, capturing screenshots for TensorFlow.js to scrutinize and identify pertinent elements.
By accurately selecting the UI element, the malware mimics typical user activity. This method proves to be more effective and resilient against modern ad variability, as many ads are dynamic, frequently altering their structure and often incorporating iframes or videos.
Another mode known as ‘signalling’ employs WebRTC to stream a live video feed of the virtual browser screen to the attackers. This real-time feed enables them to execute actions like tapping, scrolling, and inputting text.
The threat actor distributes the malware within games featured on Xiaomi’s GetApps software catalogue. Initially, the apps are innocuous but later receive updates containing malicious components.
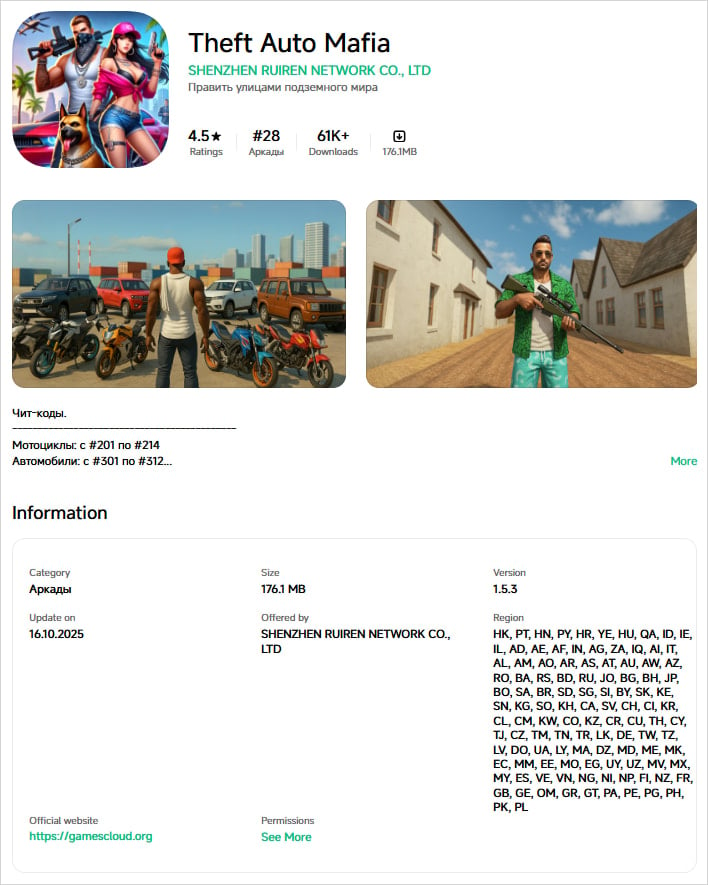
Some of the infected games identified by Doctor Web include:
- Theft Auto Mafia — 61,000 downloads
- Cute Pet House — 34,000 downloads
- Creation Magic World — 32,000 downloads
- Amazing Unicorn Party — 13,000 downloads
- Open World Gangsters — 11,000 downloads
- Sakura Dream Academy — 4,000 downloads
Source: Doctor Web
In addition to the Xiaomi-hosted apps, the trojans are also being disseminated through third-party APK sites, offering altered versions (mods) of popular apps like Spotify, YouTube, Deezer, and Netflix.
Researchers have observed that most apps on Moddroid’s “Editor’s Choice” page are infected.
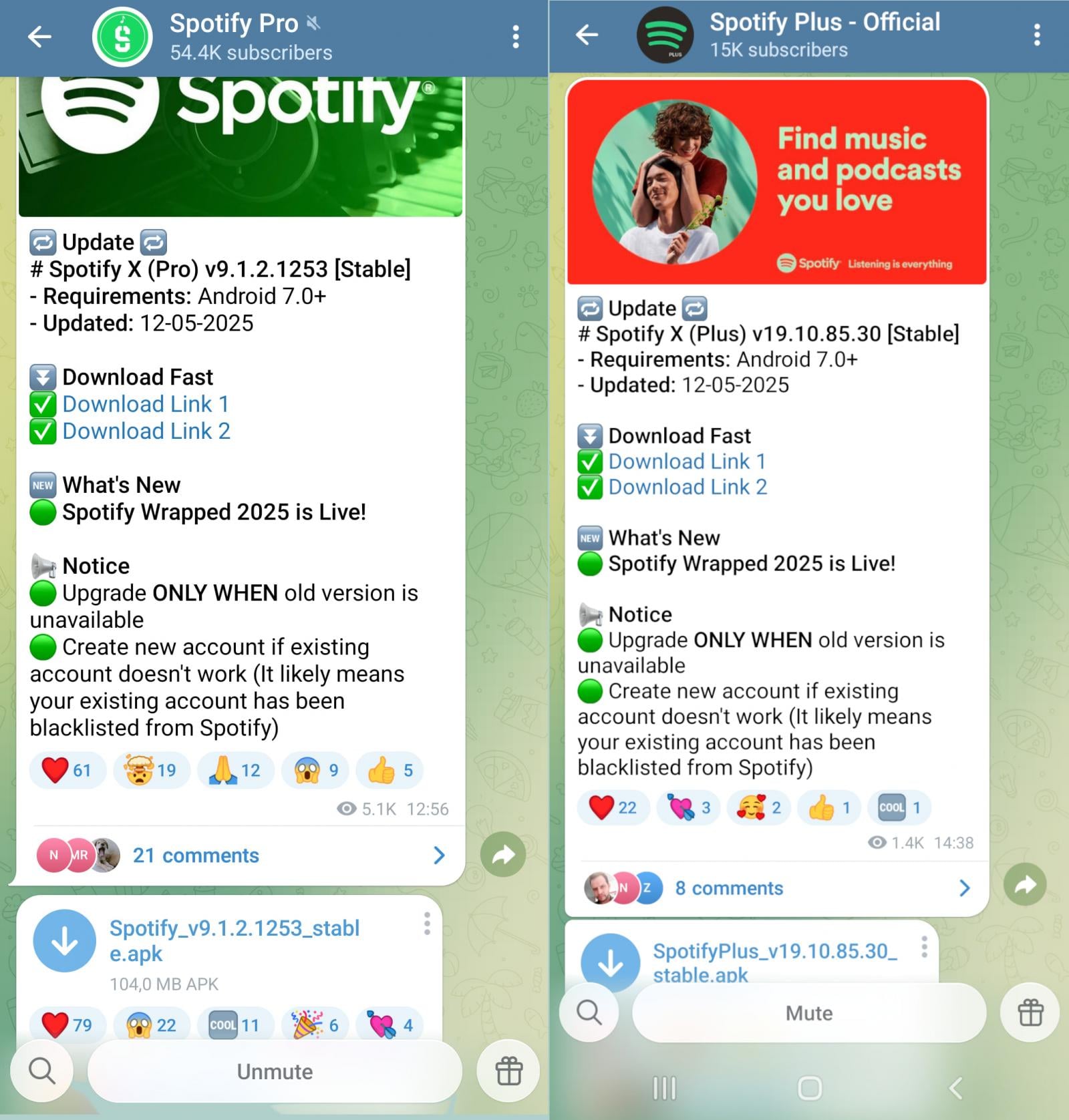
Infected APK files are further shared through Telegram channels, featuring apps such as Spotify Pro, Spotify Plus – Official, Moddroid.com, and Apkmody Chat.
Source: Doctor Web
Dr.Web has also identified a Discord server with 24,000 subscribers promoting an infected app called Spotify X.
While some of the infected apps may appear to function normally, the covert execution of click fraud within a hidden WebView poses a significant threat. Victims are unlikely to detect any malicious activity, leading to adverse effects such as battery drainage, premature device degradation, and increased mobile data charges.
Although clickjacking and ad fraud may not directly compromise user privacy and data, they remain profitable activities for cybercriminals. Users are advised to refrain from installing apps from sources other than Google Play, especially alternative versions promising additional features or free premium subscriptions.

As MCP (Model Context Protocol) gains traction as the standard for connecting LLMs to tools and data, security teams are swiftly enhancing the safety of these new services.
This complimentary cheat sheet outlines 7 best practices that you can implement today.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS




























