


Hackers Exploit Critical Bug in Weaver E-cology Software Since mid-March, hackers have been taking advantage of a critical vulnerability (CVE-2026-22679) in the Weaver E-cology office automation...
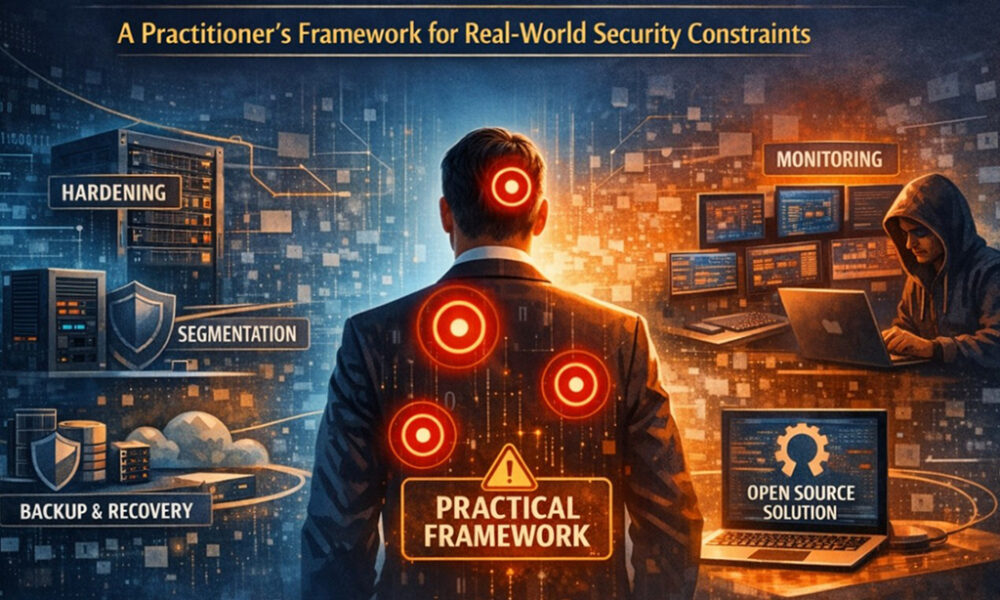

Implementing cybersecurity frameworks like NIST CSF, ISO/IEC 27001, and the CIS Critical Security Controls has played a crucial role in standardizing security practices across various industries....



Backdoored PyTorch Lightning Package Drops Credential Stealer The PyTorch Lightning package, a popular deep learning framework, was recently found to contain a malicious version on the...



The Changing Landscape of Cybersecurity: A Look into Hybrid Warfare and Cloud Resilience As of the end of 2024, Amazon revealed a staggering increase in cyberthreats,...



Educational Giant Instructure Confirms Data Breach Recently, Instructure, a prominent U.S.-based education technology company renowned for its Canvas learning management system, fell victim to a cyberattack....
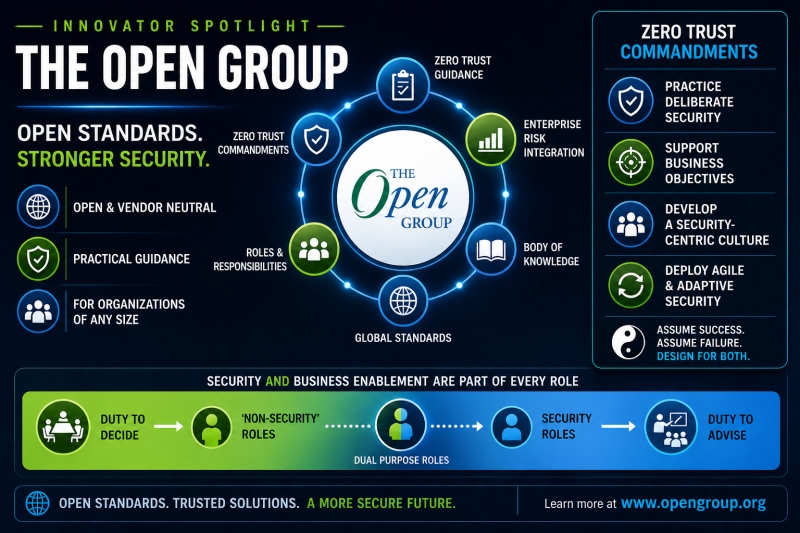


The Open Group’s Quiet Revolution In Security Roles If you have been around this industry long enough to remember the Unix wars, you already know that...



Microsoft Defender has recently identified legitimate DigiCert root certificates as Trojan:Win32/Cerdigent.A!dha, causing a surge in false-positive alerts and, in some instances, the deletion of certificates from...


Microsoft Fixes Windows Security Warning Issue in Remote Desktop Files Microsoft has successfully addressed a known issue that was causing Windows security warnings to display incorrectly...



Enhancing Threat Intelligence Integration with Criminal IP and ThreatQ Partnering with Securonix, Criminal IP brings its Threat Intelligence into ThreatQ, enabling organizations to seamlessly integrate external...



A critical vulnerability in cPanel, identified as CVE-2026-41940, is currently being exploited by cybercriminals to infiltrate websites and carry out ransomware attacks using the “Sorry” ransomware....
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.