Security
Palo Alto Networks Faces Surge in GlobalProtect Portal Login Attacks

Cybersecurity Alert: Targeting of Palo Alto Networks and SonicWall Systems
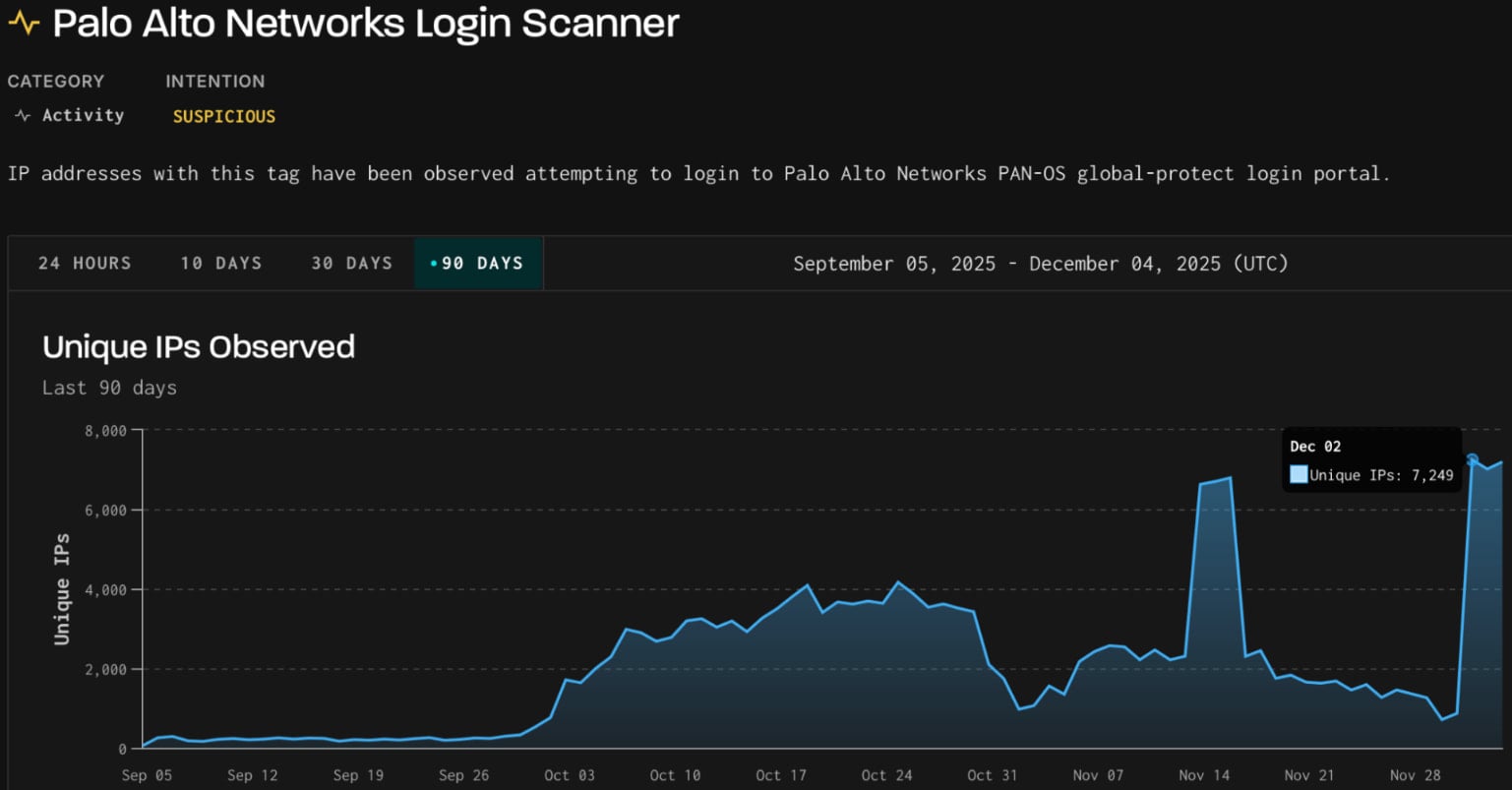
A recent cyber campaign has been identified targeting Palo Alto GlobalProtect portals and SonicWall SonicOS API endpoints. The malicious activity, which started on December 2nd, originated from over 7,000 IP addresses associated with the German IT company 3xK GmbH.
The attackers initially focused on GlobalProtect portals, using bruteforce and login attempts. They later shifted their attention to scanning SonicWall API endpoints, as reported by threat intelligence company GreyNoise.
GlobalProtect, a vital component of Palo Alto Networks’ firewall platform, is widely used by large enterprises, government agencies, and service providers for VPN and remote access.
Source: GreyNoise
According to GreyNoise’s report, the attackers targeted specific profiles within the sensor network to capture scanning and exploitation activities passively.
The surge in activity involved using three client fingerprints previously seen in scanning attempts between late September and mid-October. This past activity, originating from four ASNs with no prior malicious history, generated over 9 million non-spoofable HTTP sessions primarily aimed at GlobalProtect portals.
In mid-November, GreyNoise also observed scanning activity from 3xK Tech GmbH’s infrastructure, with 2.3 million scan sessions targeting GlobalProtect VPN portals, most of which were sourced from IPs in Germany.
Based on the analyzed indicators, GreyNoise confidently attributes both sets of activities to the same threat actor.
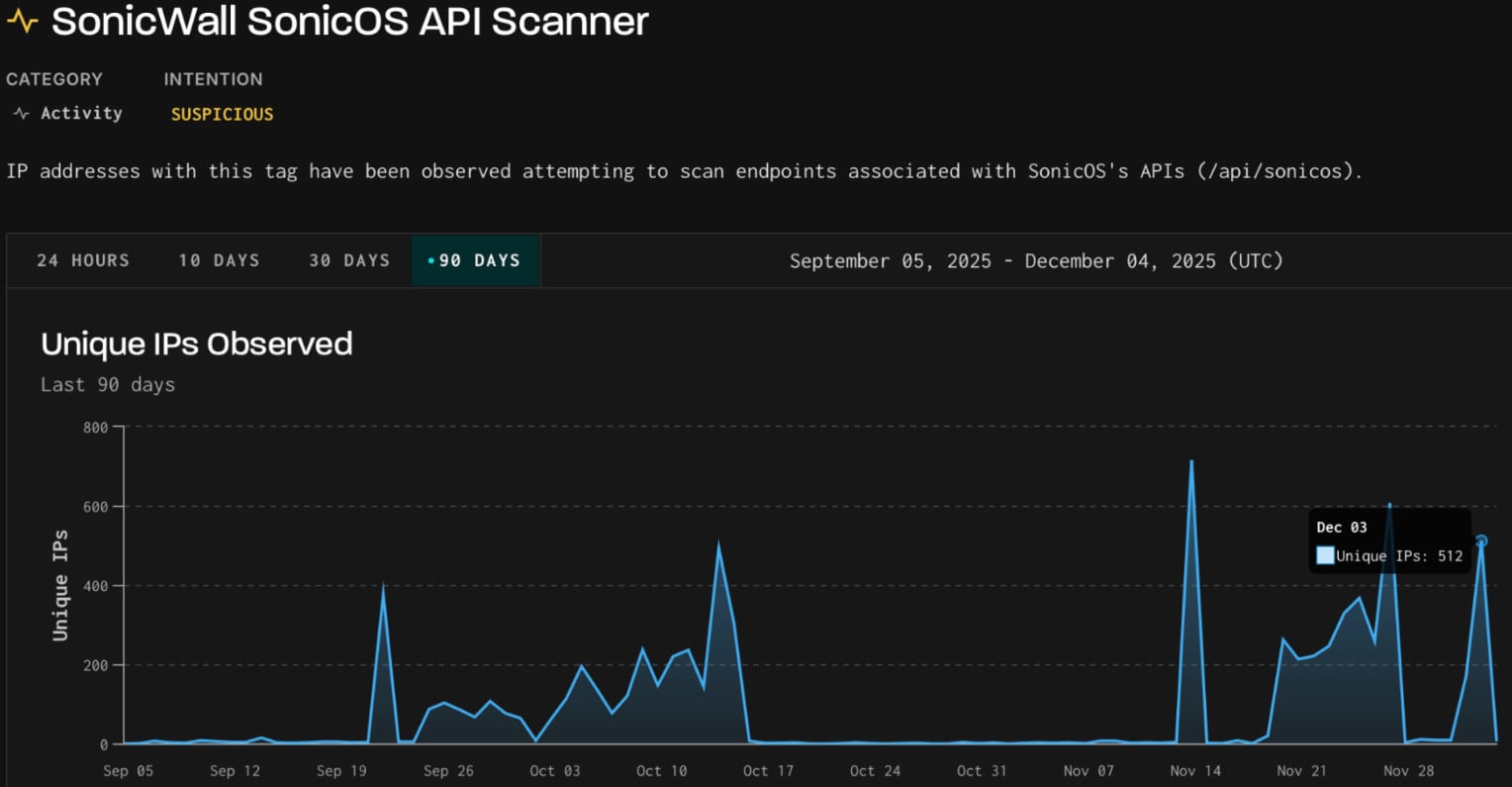
On December 3rd, the same three client fingerprints were detected in scanning activity targeting SonicWall SonicOS API.
Source: GreyNoise
SonicOS, the operating system powering SonicWall firewalls, exposes API endpoints for configuration, remote management, and monitoring. Malicious scanning of these endpoints aims to identify vulnerabilities and misconfigurations, potentially paving the way for exploitation of future flaws.
Defenders are advised to monitor and block IPs associated with this type of scanning activity. Additionally, it is recommended to track authentication surfaces for abnormal velocity or repeated failures, monitor recurring client fingerprints, and implement dynamic, context-aware blocking measures.
Upon reaching out for comment, Palo Alto Networks acknowledged increased scanning directed at GlobalProtect interfaces. The company clarified that the activity constituted credential-based attacks rather than exploiting software vulnerabilities.
Palo Alto Networks recommends the implementation of Multi-Factor Authentication (MFA) as a protective measure against credential abuse.
Protecting Your Systems

Ensuring robust IAM (Identity and Access Management) practices is crucial for safeguarding your business from cyber threats. Learn why traditional IAM methods may fall short in today’s landscape, explore examples of effective IAM strategies, and access a practical guide for building a scalable IAM strategy.
Stay vigilant against cyber threats by monitoring and securing your network infrastructure. By proactively identifying and mitigating potential risks, you can protect your organization from malicious actors seeking to exploit vulnerabilities in your systems.
For any inquiries or assistance regarding cybersecurity measures, feel free to reach out to industry-leading experts such as Palo Alto Networks and SonicWall for guidance and support.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS






























