Security
Beware: ClickFix Attack Hijacks Devices with Fake Windows BSOD Screens
New ClickFix Social Engineering Campaign Targets Hospitality Sector in Europe
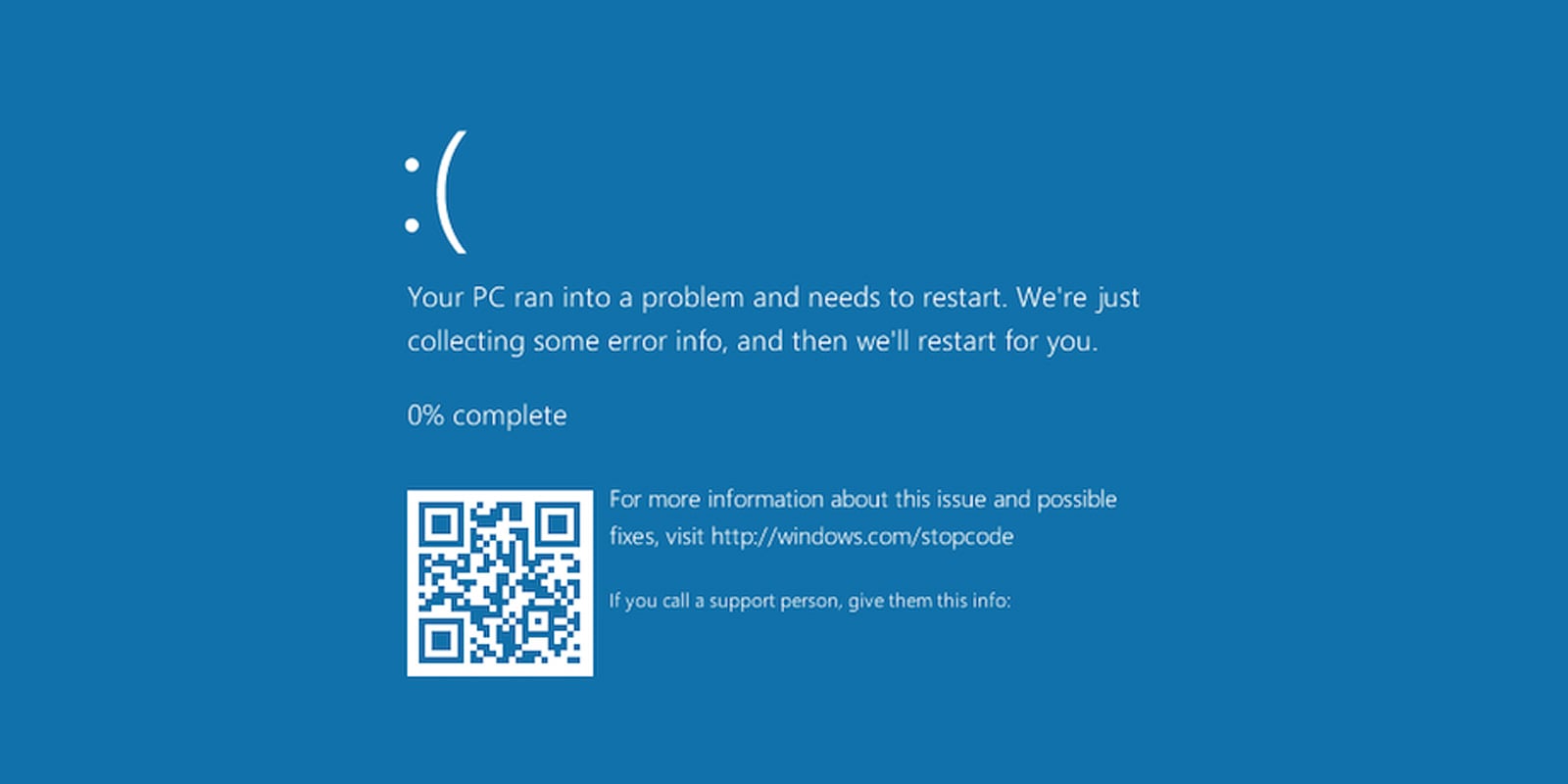
A recent social engineering campaign known as ClickFix is currently targeting the hospitality sector in Europe. This campaign utilizes fake Windows Blue Screen of Death (BSOD) screens to deceive users into manually compiling and running malware on their systems.
The BSOD is a screen that appears on Windows operating systems when a fatal error occurs, causing the system to crash and become unrecoverable.
Researchers at Securonix identified this campaign, dubbed “PHALT#BLYX,” in December. The attackers behind this campaign use phishing emails that impersonate Booking.com to initiate the ClickFix attack and distribute malware.
ClickFix Attack Impersonates BSOD Crashes
ClickFix attacks involve creating webpages that simulate errors or issues and then offering false solutions to resolve them. These deceptive tactics can include displaying fake error messages, security alerts, CAPTCHA challenges, or update notifications that trick visitors into running malicious commands on their computers.
Victims unknowingly infect their machines by executing malicious PowerShell or shell commands provided by the attackers.
In the recent ClickFix campaign, hackers send phishing emails posing as a hotel guest canceling a reservation on Booking.com, particularly targeting hospitality firms. The emails claim a substantial refund amount, creating a sense of urgency for the recipient.
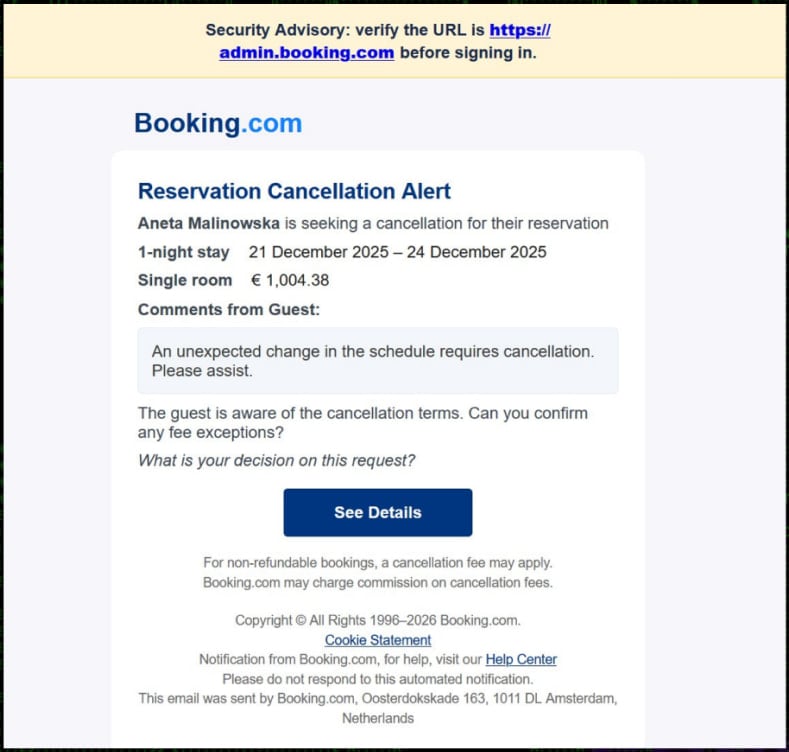
Source: Securonix
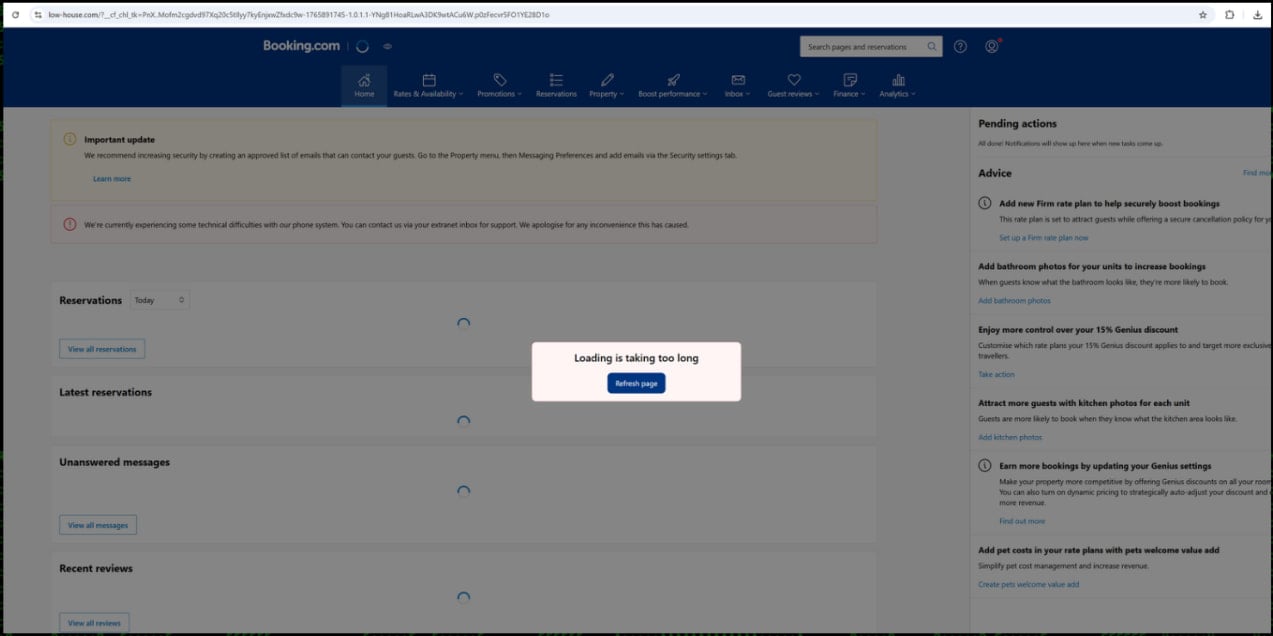
Clicking on the link in the email redirects the victim to a counterfeit Booking.com website hosted on ‘low-house[.]com,’ which closely resembles the authentic Booking.com site. The fake site mirrors Booking.com’s branding, making it challenging to distinguish from the legitimate platform.
The fraudulent webpage contains malicious JavaScript that displays a phony “Loading is taking too long” error, prompting users to click a button to refresh the page.
Source: Securonix
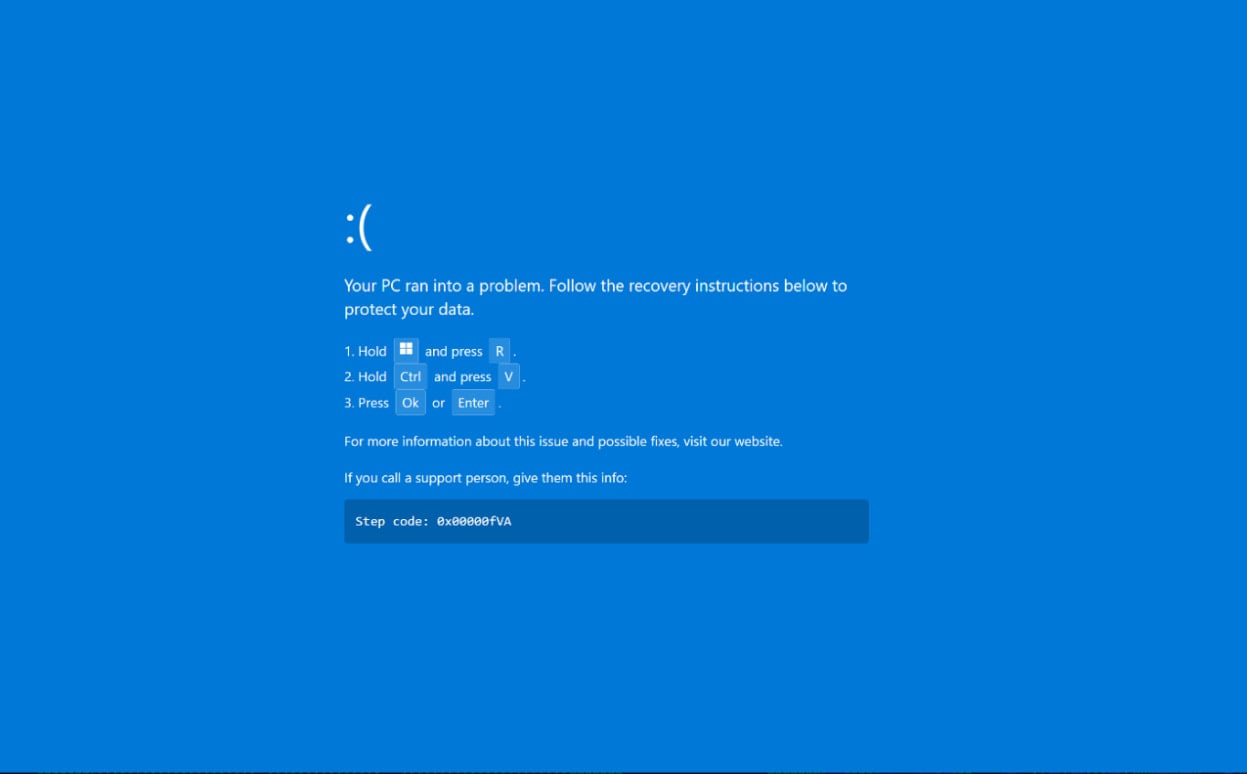
However, clicking the button triggers the browser to enter full-screen mode, displaying a counterfeit Windows BSOD crash screen to initiate the ClickFix social engineering attack.
Source: Securonix
The fake BSOD screen instructs users to open the Windows Run dialog box and press CTRL+V to paste a malicious command copied to the clipboard. By pressing OK or Enter, the command is executed.
Unlike genuine BSOD messages that only show an error code and a reboot notice, this deceptive tactic provides recovery instructions that lead users to inadvertently run malicious commands.
Pasting the provided command triggers a PowerShell script that opens a decoy Booking.com admin page while simultaneously downloading and compiling a malicious .NET project (v.proj) using the legitimate Windows MSBuild.exe compiler.
Once executed, the payload establishes Windows Defender exclusions, initiates UAC prompts for admin rights, downloads the primary loader through the Background Intelligent Transfer Service (BITS), and achieves persistence by placing a .url file in the Startup folder.
The malware, known as DCRAT, is a remote access Trojan commonly utilized by threat actors for gaining remote access to compromised devices.
DCRAT is injected into the authentic ‘aspnet_compiler.exe’ process through process hollowing and executed directly in memory. Upon connecting to the command-and-control (C2) server, the malware sends its complete system fingerprint and awaits further instructions.
It supports various malicious functionalities such as remote desktop control, keylogging, reverse shell, and in-memory execution of additional payloads. In the observed case, the attackers deployed a cryptocurrency miner.
By establishing remote access, threat actors can infiltrate the target’s network, propagate to other devices, exfiltrate sensitive data, and potentially compromise additional systems.

As it’s budget season, over 300 CISOs and security leaders have shared their plans, spending strategies, and priorities for the upcoming year. This report consolidates their insights, enabling readers to benchmark strategies, spot emerging trends, and compare priorities for 2026.
Discover how top leaders are translating investments into tangible outcomes.
Transform the following sentence:
Original: The cat chased the mouse.
Transformation: The mouse was chased by the cat.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS