Security
GootLoader Malware’s Clever Evasion Tactics: Using Hundreds of ZIP Archives

The Rise of GootLoader: A Deceptive Malware Loader
A malicious JavaScript loader known as GootLoader has recently been identified using a unique tactic to evade detection. This loader utilizes a malformed ZIP archive that concatenates anywhere from 500 to 1,000 archives, making it challenging for traditional unarchiving tools to extract the contents accurately.
Security researcher Aaron Walton from Expel described this technique as an anti-analysis measure, as many tools struggle to handle the malformed archive except for the default Windows unarchiver. This allows the malware to be extracted and executed on victims’ systems, bypassing automated analysis workflows.
GootLoader is commonly spread through search engine optimization (SEO) poisoning and malvertising techniques, targeting unsuspecting users searching for legal templates. Once users visit compromised WordPress sites hosting malicious ZIP archives, they unknowingly expose themselves to GootLoader, which can deliver ransomware and other harmful payloads.
The Evolution of GootLoader Techniques
In late October 2025, new iterations of GootLoader emerged with enhanced evasion tactics. These include using custom WOFF2 fonts for filename obfuscation and exploiting the WordPress comment endpoint to deliver ZIP payloads. The threat actors behind GootLoader continue to evolve their delivery methods to avoid detection.
- Creating malicious ZIP files by concatenating 500-1,000 archives
- Manipulating the archive’s structure to trigger parsing errors
- Randomizing non-critical fields to confuse unarchiving tools
Walton referred to the randomization technique as “hashbusting,” ensuring that each downloaded ZIP file from GootLoader’s infrastructure is unique, making it difficult to detect in different environments. This approach extends to the JScript file contained within the archive, adding layers of defense evasion.
The Attack Chain and Execution Process
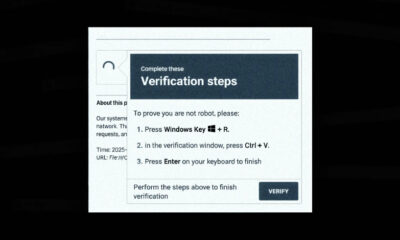
When a victim downloads the ZIP archive and opens it, the default Windows unarchiver extracts the JavaScript payload. Executing the JavaScript file triggers its operation via “wscript.exe,” leading to the creation of a Windows shortcut for persistence. Subsequent actions involve PowerShell commands to advance the infection.
Organizations can mitigate the GootLoader threat by restricting the execution of “wscript.exe” and “cscript.exe” for downloaded content. Additionally, setting a Group Policy Object to open JavaScript files in Notepad by default can prevent unintentional execution via “wscript.exe.”
Conclusion
GootLoader represents a significant cybersecurity threat due to its deceptive tactics and ability to deliver harmful payloads. Understanding its evasion techniques and implementing proactive measures can help organizations safeguard against such malware attacks.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS