Security
Security Threat: Chrome Extensions Exploiting Enterprise HR Platforms for Credential Theft
Malicious Chrome Extensions Targeting Enterprise Platforms Discovered
Recently, cybersecurity firm Socket uncovered a campaign involving five Chrome extensions on the Chrome Web Store that posed as productivity and security tools for enterprise HR and ERP platforms. These extensions, targeting Workday, NetSuite, and SAP SuccessFactors, were installed over 2,300 times collectively.
According to Socket, the campaign utilized three attack methods: cookie exfiltration to remote servers, DOM manipulation to block security administration pages, and bidirectional cookie injection for direct session hijacking.
The extensions, despite being published under different names, shared identical infrastructure, code patterns, and targeting. Four of them were attributed to the developer name databycloud1104, while the fifth operated under the name Software Access.
While the extensions affected only a limited number of users, the theft of enterprise credentials could potentially lead to large-scale ransomware and data theft attacks.
Deceptive Marketing to Enterprise Users
Socket revealed that these extensions were marketed to users of enterprise HR and ERP platforms, portraying themselves as tools designed to enhance productivity, streamline workflows, and bolster security controls.
Some extensions claimed to provide simplified access to premium tools for platforms like Workday and NetSuite. For instance, Data By Cloud 2, a popular extension installed 1,000 times, offered bulk management tools and faster access for users handling multiple enterprise accounts.
Another extension, Tool Access 11, positioned itself as a security-focused add-on that restricted access to sensitive administrative features to prevent account compromise.
Despite their claims, the extensions failed to disclose their true intentions of extracting cookies, exfiltrating credentials, and blocking security administration pages. Their privacy policies also lacked transparency regarding data collection.
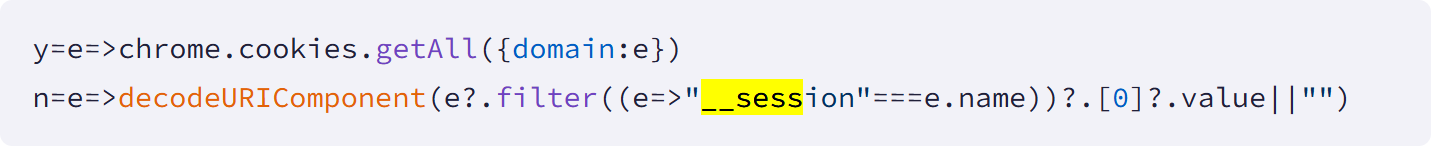
Socket’s analysis of the extensions uncovered malicious behaviors such as authentication cookie exfiltration, administrative page blocking, and session hijacking through cookie injection.
The extensions continuously extracted authentication cookies named “__session” every 60 seconds for targeted domains, allowing attackers to maintain access even after users logged out.
Source: Socket
Two extensions, Tool Access 11 and Data By Cloud 2, blocked access to security and incident response pages within Workday by erasing content or redirecting administrators from management pages.
Software Access, the most malicious extension, incorporated bidirectional cookie manipulation, enabling direct session hijacking by injecting stolen cookies into a browser.
Socket reported these extensions to Google, resulting in their removal. Users who had installed these extensions were advised to inform their security administrators, initiate incident response procedures, and update their passwords on affected platforms.

Whether you’re cleaning up old keys or setting guardrails for AI-generated code, this guide helps your team build securely from the start.
Get the cheat sheet and take the guesswork out of secrets management.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS































