Security
Data Breach: Inside the Risks of Corporate Cloud Storage

Zestix Offers Stolen Corporate Data from Cloud File-Sharing Sites
In recent developments, a threat actor known as Zestix has been detected selling corporate data stolen from numerous companies. The breach seems to have originated from ShareFile, Nextcloud, and OwnCloud instances.
According to Hudson Rock, a cybercrime intelligence company, the breach was likely facilitated by info-stealing malware like RedLine, Lumma, and Vidar, which were deployed on employee devices to gather credentials.
These malware types are typically spread through malvertising campaigns or ClickFix attacks, targeting data stored in web browsers, messaging apps, and cryptocurrency wallets.
One crucial vulnerability highlighted is the absence of multi-factor authentication (MFA) protection, which enables threat actors with valid credentials to gain unauthorized access to platforms like file-sharing services.
Hudson Rock’s report further reveals that some stolen credentials have been circulating in criminal databases for years, indicating a failure to rotate or invalidate them even after prolonged periods.
Multiple Breaches Across Various Sectors
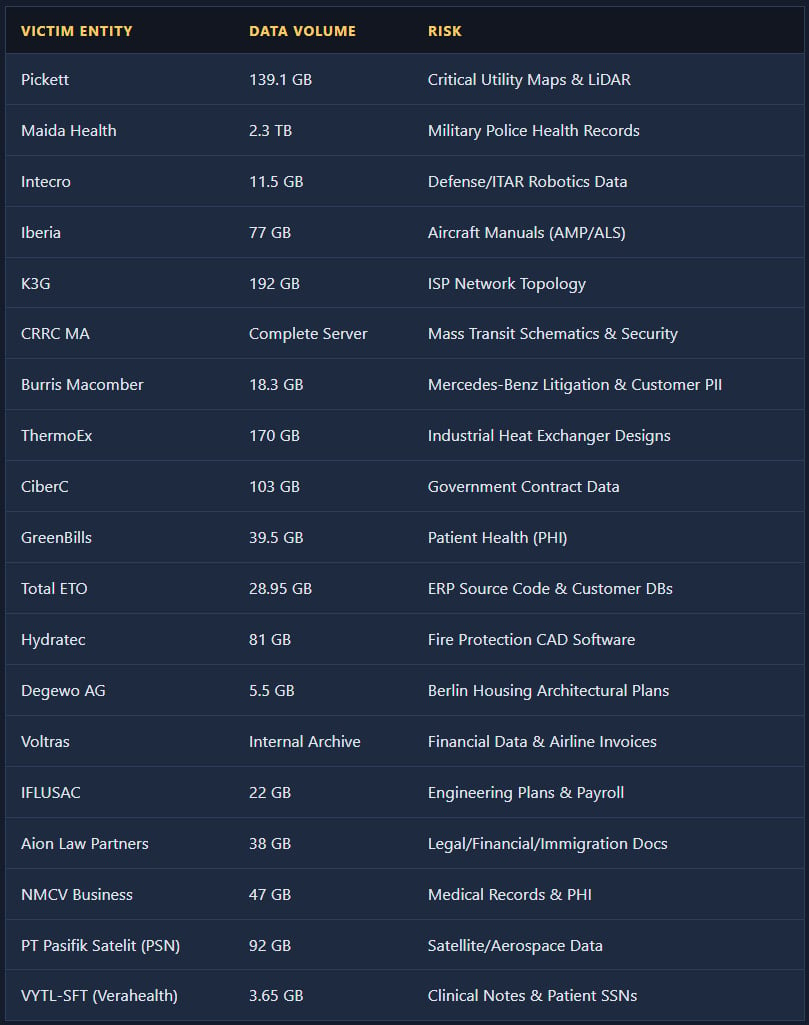
Zestix operates as an initial access broker (IAB) in underground forums, selling access to high-value corporate cloud platforms such as ShareFile, Nextcloud, and OwnCloud. These breaches have affected organizations in sectors like aviation, defense, healthcare, utilities, mass transit, telecommunications, legal, real estate, and government.
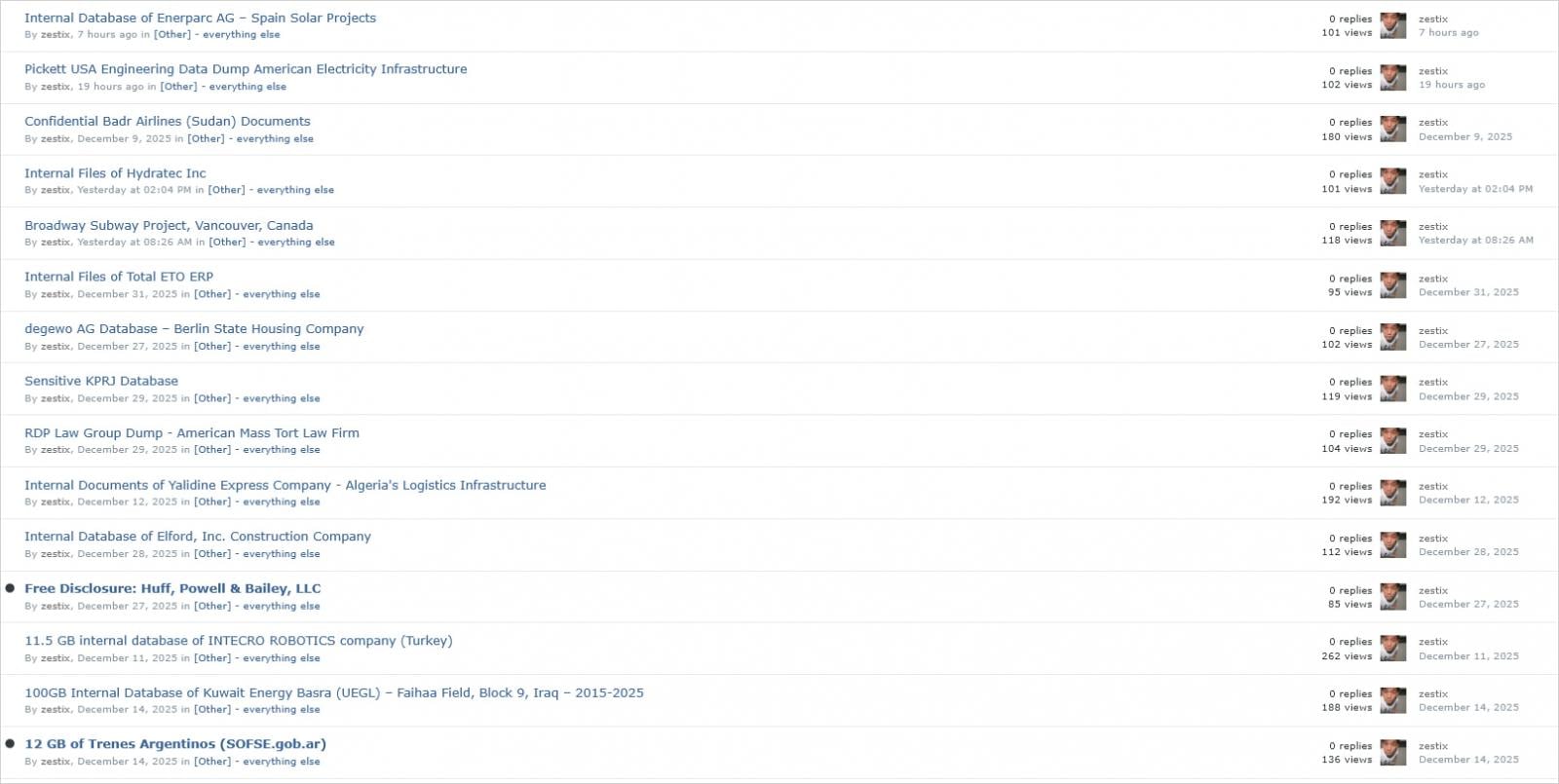
Source: Hudson Rock
By analyzing infostealer logs, Zestix gains access to cloud file-sharing services using valid credentials where MFA is not implemented. Hudson Rock has identified potential breach points by cross-referencing infostealer data with publicly available information.
It’s worth noting that while Hudson Rock has identified stolen employee credentials in several cases, there is no public confirmation of security breaches from the affected companies. One exception may be Iberia, although it’s not directly linked to Hudson Rock’s findings.
Zestix has offered to sell stolen data volumes ranging from gigabytes to terabytes, including aircraft maintenance manuals, defense files, customer databases, health records, mass-transit schematics, utility maps, and government contracts.
Source: Hudson Rock
Additionally, Hudson Rock has uncovered another set of 30 victims sold under the alias “Sentap.” They emphasize that cloud exposure is a systemic issue stemming from organizations’ lax security practices, with infected computers identified at major companies like Deloitte, KPMG, Samsung, Honeywell, and Walmart.
Hudson Rock has informed ShareFile of the breaches and plans to notify Nextcloud and OwnCloud for appropriate action.

As MCP (Model Context Protocol) becomes the standard for connecting LLMs to tools and data, security teams are moving fast to keep these new services safe.
This free cheat sheet outlines 7 best practices you can start using today.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS