Security
Exploiting Qilin Ransomware: Harnessing WSL for Linux Encryptors on Windows
A recent discovery has unveiled the Qilin ransomware operation’s tactics of executing Linux encryptors within Windows using the Windows Subsystem for Linux (WSL) to avoid detection by conventional security tools.
Originally known as “Agenda” when it emerged in August 2022, the ransomware rebranded itself as Qilin by September and has continued its malicious operations under this new name ever since.
Qilin has rapidly become one of the most active ransomware operations globally, with reports from Trend Micro and Cisco Talos indicating that the cybercrime group has targeted over 700 victims across 62 countries in the present year.
Both cybersecurity firms have highlighted the group’s prolific nature, with statistics showing that Qilin has been responsible for over 40 new victims per month in the latter half of 2025.
According to research findings, Qilin affiliates employ a combination of legitimate software and remote management tools to infiltrate networks and steal credentials. These tools include AnyDesk, ScreenConnect, and Splashtop for remote access, as well as Cyberduck and WinRAR for data theft.
Furthermore, the threat actors utilize common Windows utilities like Microsoft Paint (mspaint.exe) and Notepad (notepad.exe) to scan documents for sensitive information before exfiltrating them.
Exploiting Vulnerable Drivers to Disable Security Measures
Recent observations by Trend Micro and Talos have revealed that Qilin affiliates engage in Bring Your Own Vulnerable Driver (BYOVD) attacks to circumvent security software before deploying encryptors.
The attackers deploy signed but vulnerable drivers, such as eskle.sys, to halt antivirus and EDR processes. Additionally, they use DLL sideloading to introduce additional kernel drivers (rwdrv.sys and hlpdrv.sys) that provide elevated kernel-level privileges.
Talos noted that the threat actors utilize tools like “dark-kill” and “HRSword” to disable security software and erase any traces of their malicious activities.
Cisco Talos explained, “We have frequently observed attempts to disable EDR through various methods, including directly executing the EDR’s ‘uninstall.exe’ or stopping services using the sc command. Moreover, attackers have been seen using open-source tools like dark-kill and HRSword.”
Launching Linux Encryptors via WSL
In December 2023, reports surfaced regarding a new Qilin Linux encryptor that specifically targets VMware ESXi virtual machines and servers.
The encryptor offers command-line options for debug mode activation, conducting dry runs without encryption, and customizing the encryption process for virtual machines and their snapshots.
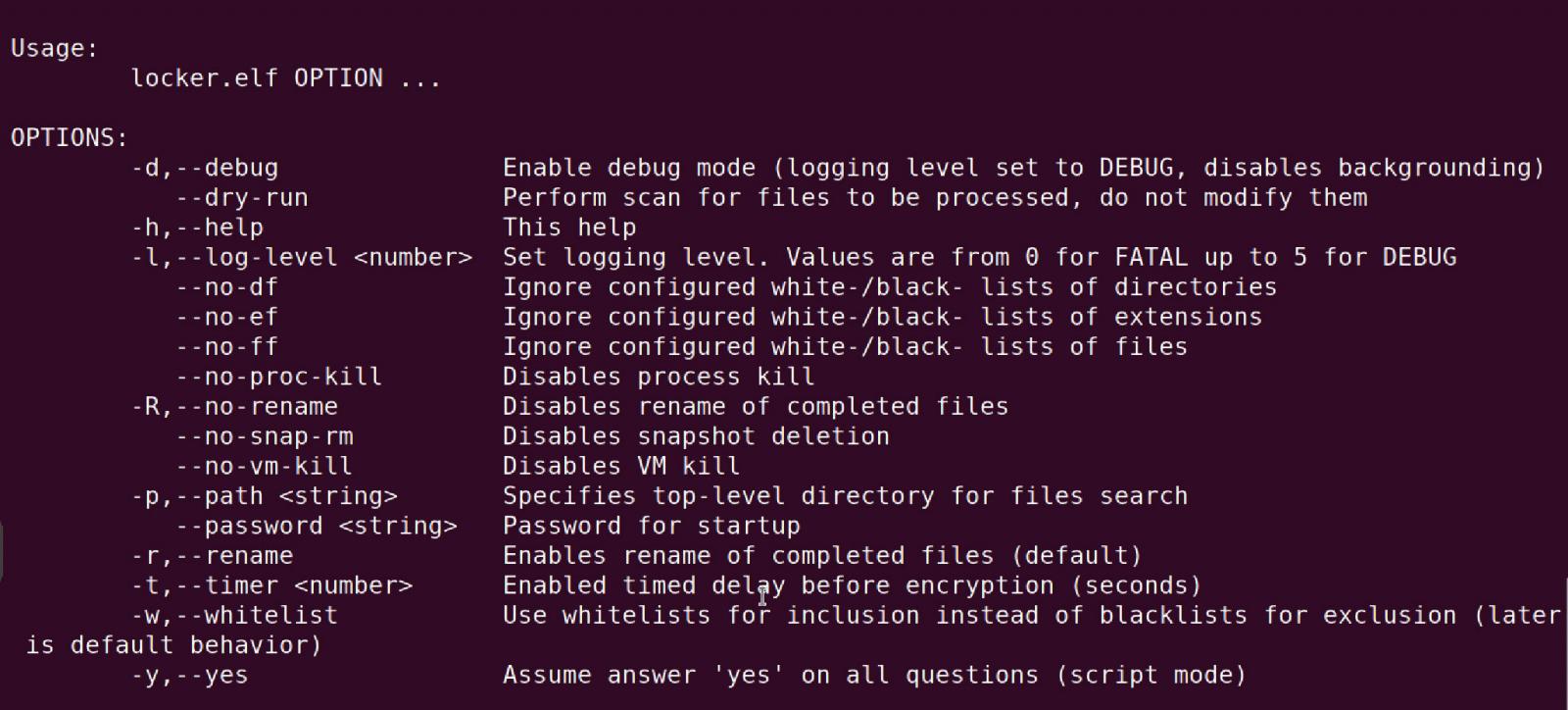
Source: BleepingComputer
Researchers at Trend Micro have identified instances where Qilin affiliates leverage WinSCP to transfer the Linux ELF encryptor to compromised devices. Subsequently, the encryptor is launched using the Splashtop remote management software (SRManager.exe) within the Windows environment.
Although initially labeled as cross-platform, Qilin’s Linux encryptors are ELF executables, necessitating a runtime environment like the Windows Subsystem for Linux (WSL) for execution.
Further investigations revealed that threat actors indeed utilize WSL to execute the encryptor on compromised systems.
WSL is a Windows feature that enables the installation and operation of Linux distributions directly within the Windows environment. Threat actors exploit this feature by installing WSL upon gaining access to a device and using it to execute the Linux encryptor, effectively evading traditional Windows security measures.
Trend Micro highlighted, “The threat actors were able to run the Linux encryptor on Windows systems by leveraging the Windows Subsystem for Linux (WSL), a built-in feature that facilitates the execution of Linux binaries on Windows without the need for a virtual machine.”
As many Windows EDR products focus on Windows PE behavior, malicious activities occurring within WSL often evade detection, allowing ransomware to bypass traditional security measures.
This technique underscores ransomware operators’ adaptation to hybrid Windows and Linux environments to expand their reach and outsmart conventional defenses.

46% of environments had passwords cracked, nearly doubling from 25% last year.
Discover more insights on prevention, detection, and data exfiltration trends in the Picus Blue Report 2025.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS
































