Security
Cellik Android Malware: How Google Play Apps are Being Weaponized

Cellik Android Malware: A New Threat Targeting Google Play Apps
A recent emergence in the cybercrime landscape is the Cellik Android malware-as-a-service (MaaS), which is currently being promoted on underground forums. This malicious software offers a wide range of capabilities, including the ability to embed itself in any app found on the Google Play Store.
Cybercriminals can handpick apps from the official Android app store and create modified versions that mimic the original app’s interface and functionality. This tactic makes the trojanized apps appear legitimate and trustworthy, increasing the likelihood of evading detection.
Cellik infections have the potential to remain undetected for extended periods due to their ability to blend seamlessly with authentic apps. The seller of the malware also suggests that this method may help bypass Google’s Play Protect security measures, although this claim has not been verified.

According to findings by mobile security firm iVerify, Cellik was discovered on underground forums where it is offered for a monthly fee of $150 or a lifetime access fee of $900.
Capabilities of Cellik Malware
Cellik is a sophisticated Android malware that boasts features such as real-time screen capturing and streaming, interception of app notifications, file system browsing, data exfiltration, data wiping, and communication with a command-and-control server through an encrypted channel.
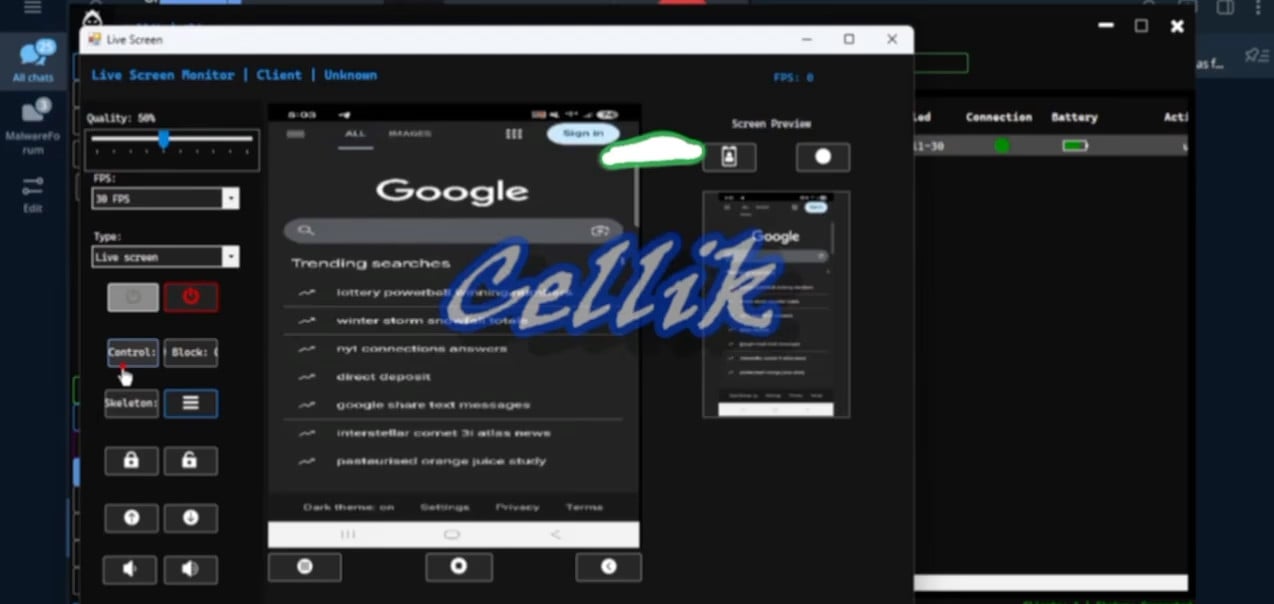
Source: iVerify
Additionally, Cellik features a hidden browser mode that enables attackers to access websites using the victim’s stored cookies, enhancing their ability to carry out malicious activities.
The malware includes an app injection system that allows cybercriminals to overlay fake login screens or inject malicious code into apps, enabling the theft of user credentials.
Another notable capability is the option to inject payloads into legitimate apps, making it harder to detect the infection. Trusted apps can suddenly exhibit malicious behavior, complicating the identification process.

Source: iVerify
One of the standout features of Cellik is its integration with the Play Store in the APK building process. This functionality enables cybercriminals to browse the store, select desired apps, and create malicious variants of them.
iVerify explains, “The seller claims Cellik can bypass Google Play security features by wrapping its payload in trusted apps, essentially disabling Play Protect detection. While Google Play Protect typically flags unknown or malicious apps, trojans hidden inside popular app packages might slip past automated reviews or device-level scanners.”
BleepingComputer reached out to Google for clarification on whether Cellik-bundled apps can evade Play Protect, but a response was not immediately available.
To safeguard against such threats, Android users are advised to refrain from downloading APKs from untrustworthy sources, ensure that Play Protect is active on their devices, review app permissions, and remain vigilant for any unusual activities.

Broken IAM isn’t just an IT problem – the impact ripples across your whole business.
This practical guide covers why traditional IAM practices fail to keep up with modern demands, examples of what “good” IAM looks like, and a simple checklist for building a scalable strategy.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS


























